Many flows still expose customer and agent mobiles on caller ID, so conversations work today but create privacy, compliance, and abuse problems for tomorrow.
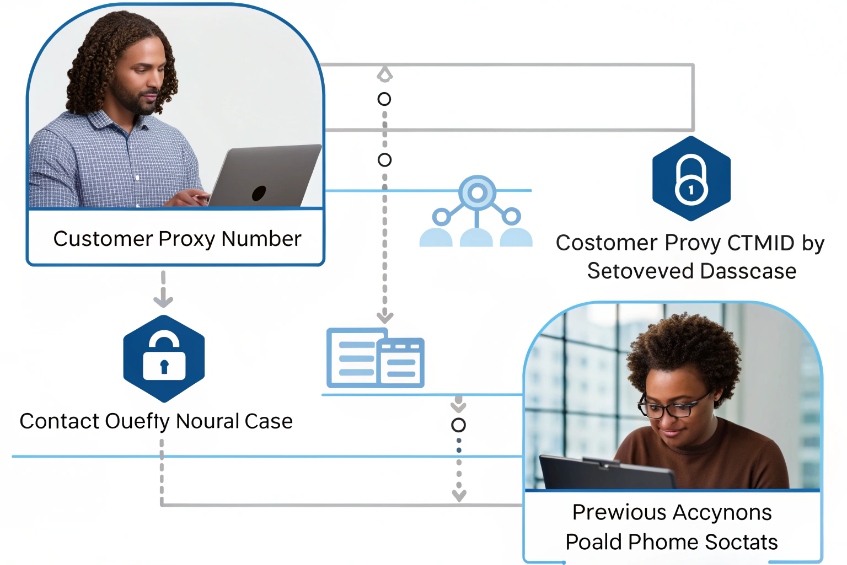
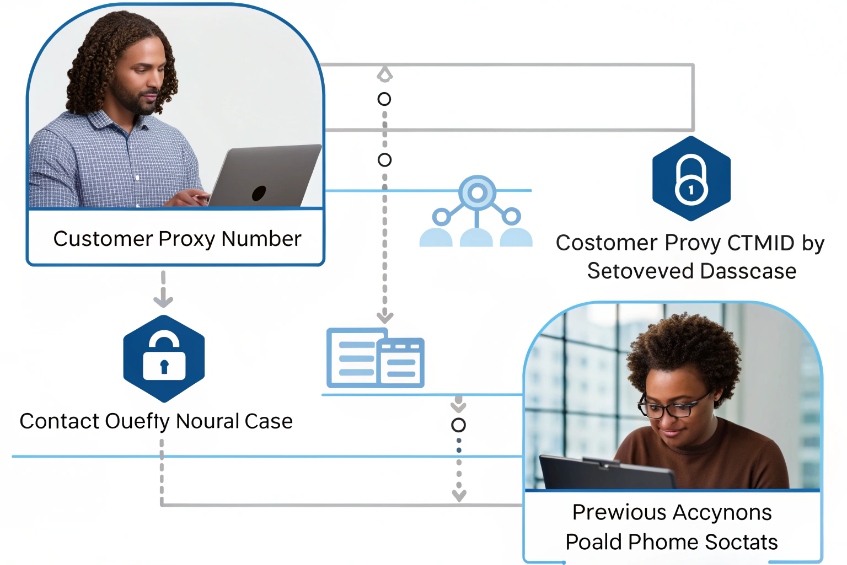
Masked phone numbers are temporary proxy DIDs that sit between customers and agents. My contact flow routes both sides through that proxy so they can talk or text without sharing real numbers.

In a masked flow, neither side calls the other directly. The platform allocates a virtual number from a pool 1, binds it to both parties using attributes like customer ID or order ID, and rewrites the To/From headers 2 on each leg. Calls, SMS, and recordings still pass through the PBX or CPaaS, but the real numbers stay hidden. This design improves trust, but it also changes how I handle compliance, logging, billing, and even simple callbacks.
How does masking protect customer privacy and compliance?
Many companies say they care about privacy but still store raw phone numbers everywhere, from PBX logs to spreadsheets and agents’ mobiles.
Masking protects privacy because agents and customers only see proxy numbers, while the platform stores real numbers in controlled systems and links them through pseudonymous session keys.
What masking changes in the data path
When I add masking to a contact flow, I change three things at once:
-
What people see
- Customers see a local or toll-free proxy, not an agent’s real number.
- Agents see an internal or proxy number, not the customer’s personal phone.
-
What systems store
- The telephony layer stores the real numbers in a limited place, often in an encrypted table.
- The rest of the stack (CRM, ticketing, QA tools) works with a session or case ID instead.
-
How I join events later
- I use a pseudonymous key such as
session_7f38…to link recordings, transcripts, and metrics. - I only touch real numbers when I truly need them, for example for refunds or fraud checks.
- I use a pseudonymous key such as
This is classic data minimisation 3. The fewer systems that know the real number, the easier it is to protect it and to answer auditors when they ask where personal data lives.
Compliance touchpoints in everyday terms
Number masking supports many privacy rules, but it does not replace them. I still must:
- Play consent prompts for recording on every leg.
- Honor SMS opt-out keywords like “STOP” 4 even when they hit a proxy.
- Avoid routing emergency calls through masked numbers, so caller ID and location stay correct.
The difference is that my default mode is safer. Agents no longer leave with a list of customer mobiles in their call history. Third-party tools receive session IDs, not raw numbers. Data subject access requests and deletion requests become easier because less data is spread around.
A simple way to think about it:
| Area | Without masking | With masking |
|---|---|---|
| What people see | Real numbers everywhere | Proxies on caller ID for both sides |
| What apps store | Raw phone numbers in many databases | Session IDs in most apps, real numbers in one place |
| Abuse risk | Easier off-platform contact and harassment | Off-platform contact more difficult |
| Compliance story | Hard to prove minimal data use | Cleaner map of where real numbers live |
Masking does not make me “instantly compliant,” but it gives me a solid base. If I combine it with clear consent prompts and simple retention rules, my contact flows are much easier to defend from both a legal and a security view.
Can I display a proxy number per session or agent?
If I always use the same caller ID, customers save it, call it months later, and expect context that the system no longer has.
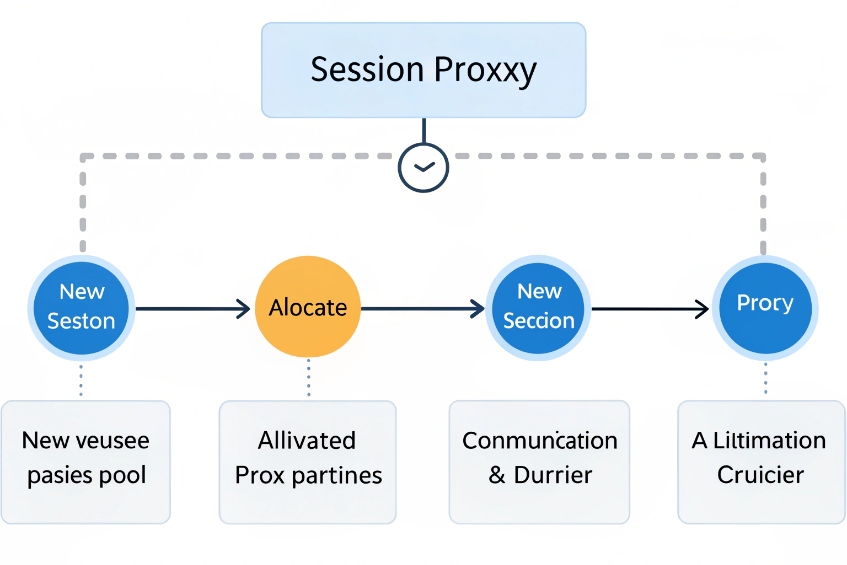
Yes. I can allocate proxy numbers per session, per order, per customer, or per agent. The flow just needs a number pool and clear rules for how to bind and release each mapping.
Common proxy assignment patterns
The masking logic lives in a very small decision: “Given this interaction, which proxy number should I show?” In practice, I see a few stable models:
| Model | What it binds to | Good for |
|---|---|---|
| Session-based | One call or short-lived session | One-off deliveries, ride-sharing, escorts |
| Case / order-based | Ticket ID or order ID | Support cases, marketplaces, repairs |
| Customer-based | Customer profile | Ongoing account management, VIP customers |
| Agent-based | Specific agent or team | Direct relationships, B2B accounts |
A session-based proxy might live for 30–90 minutes. Once both sides hang up and the time-to-live ends, the proxy goes back to the pool. This is common in on-demand delivery and transport, where the customer and driver should not call each other next week.
A case-based proxy lasts as long as the ticket stays open. The same masked number works for callbacks from both sides, and the contact flow can reopen the right context. When I close the case, the binding expires.
An agent-based proxy gives each agent a stable external identity. This is handy in B2B sales or account management, where the customer wants to save “their” advisor’s number without seeing the real mobile. I can still swap devices and soft clients without changing that external face.
Geo-matching and number pool design
To make masking feel natural and cost-effective, I need a good pool:
- Local numbers for each important city or country so customers see familiar area codes.
- Enough numbers so I avoid collisions between active sessions.
- Simple routing rules so inbound calls to any proxy land in the correct flow.
A basic design might be:
| Country | Pool type | Allocation rule |
|---|---|---|
| US | Local DIDs by state | Prefer same-state number as customer |
| EU | Country-wide DIDs | Match customer’s country |
| Others | Regional numbers | Use closest available proxy |
In the flow, I look up an existing binding first by customer ID or case ID. If one exists and is still valid, I reuse the same proxy so the number feels stable. If not, I pick a new free number that matches the customer’s region.
The important part is expiry. Each binding needs a clear end of life, defined by time, case status, or last activity. Otherwise my pool will fill up with stale links, and I will waste numbers or route old calls into dead cases.
How do I record and bill masked calls accurately?
Masking can break reporting if I only track proxies. Calls will look like they start and end inside my platform, and it becomes harder to tie them back to customers, agents, and projects.
I record and bill masked calls by treating each leg as its own CDR, linking them with a session ID, and billing based on leg usage while keeping personal numbers out of most reports.
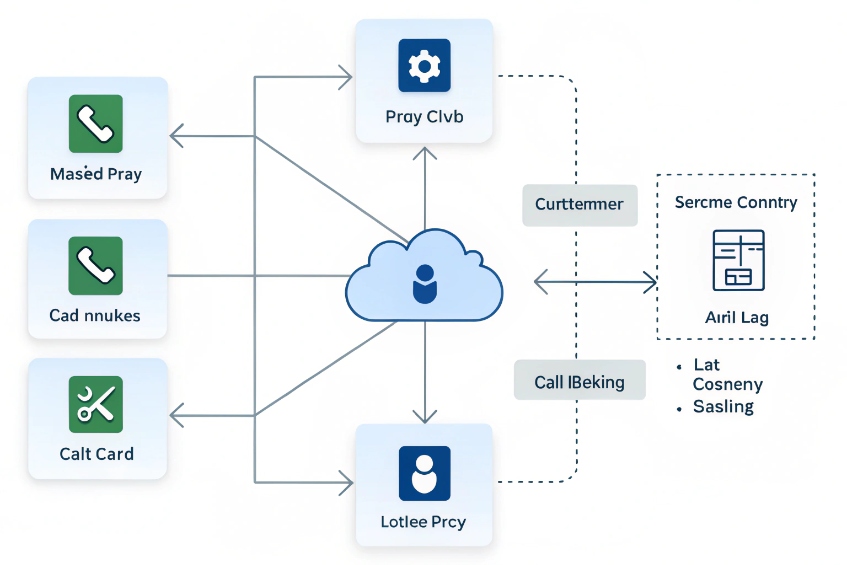
Think in call legs, not single calls
Masked interactions usually have at least two legs:
- A-leg: platform ↔ customer (or driver, patient, buyer).
- B-leg: platform ↔ agent (or seller, dispatcher, support).
Sometimes I add more legs for transfers, conferences, or IVRs. For each leg, I want:
- Start time and end time.
- Billed seconds and applied rate.
- Proxy number used on that leg.
- Pseudonymous session or case ID.
Real numbers stay inside a secure mapping table that links session IDs to raw CLIs. Most reports only need the session ID, project code, and maybe country or area, not the full number.
A simple logging model looks like this:
| Field | Example |
|---|---|
| session_id | sess_7f38c9… |
| leg | A / B / transfer |
| proxy_did | +1 212 555 0100 |
| remote_country | US |
| billable_seconds | 183 |
| recording_id | rec_94ab… |
When I bill, I sum billable_seconds by customer account or project. When I do QA, I open recording_id by session_id. Only if I have a strong reason do I open the CLI mapping table.
Recording flows with masked numbers
Masking does not change how I technically record calls. It changes where I store and present recording metadata.
I still:
- Start and stop recording based on contact flow logic or queue policies.
- Respect opt-in prompts and regional recording laws.
- Store the raw media in a secure bucket or recording server.
In the metadata about that recording, I keep:
- Session ID and case ID.
- Agent ID or extension.
- Proxy DID used.
- Tags for project or campaign.
If someone from QA or training listens to that call, they see the case ID and agent. They do not see the customer’s real number. This matches the idea of pseudonymisation 5 that many regulations encourage: the content is still personal, but I reduce direct identifiers where I can.
Cost, rating, and double-leg math
Masked calls have a cost quirk: I often pay for both legs. That means I must think about:
- Internal rating: how I recharge these costs to the right project, vendor, or business unit.
- External rating: what I charge the marketplace or customer if this is a paid service.
A helpful view is:
| Concern | What to track | How masking changes it |
|---|---|---|
| Carrier cost | Per-leg rates, per country | Often two legs instead of one |
| Internal billing | Project, case, or tenant ID | Use session ID to group all legs and media |
| Partner billing | Duration, direction, count of sessions | Hide real numbers; report on proxies only |
If I design my call detail records (CDRs) 6 schema with masking in mind from day one, reporting, QA, and finance teams can all work with the same session ID while keeping personal phone numbers in a smaller, better controlled area of the platform.
Why do callbacks reveal real numbers sometimes?
Even with masking in place, users sometimes see a real mobile on callback, or a customer calls back later and reaches a personal device instead of the masked route.
Callbacks reveal real numbers when some calls bypass the masking layer, when outbound caller ID is misconfigured, or when apps and phones store and reuse original CLIs instead of proxies.

Typical leakage points
Number masking works only if every path goes through the proxy. In real life, a few cracks appear:
-
Agent dials directly from their mobile
They call the customer’s real number outside the platform, so the customer now has the agent’s true CLI. -
Agent’s outbound caller ID bypasses the platform identity
If the SIP path trusts headers like P-Asserted-Identity (PAI) 7, the far end may see a non-proxy identity unless you enforce proxy presentation. -
CRM or app shows raw numbers
The agent copies and pastes the real number into their phone or a third-party dialer. -
Customer saves the real number from an earlier interaction
If older flows did not use masking, saved contacts may bypass new proxies.
These issues are process and configuration problems, not masking failures. The platform can only protect numbers if all official calls stay inside it.
Fixing caller ID and callback paths
I usually harden callback behavior in three layers:
-
Enforce outbound caller ID
Outbound calls from agents use a mask or a generic business number, never their personal DID or SIM CLI. The platform ignores device-level caller ID when it conflicts. -
Force callback through the proxy
Notifications and SMS from the system always show the proxy number. Links in apps initiate calls back to that proxy, not to the raw number. -
Hide raw numbers in everyday tools
User-facing screens show masked or shortened numbers unless the user has a special role that needs full access.
A quick troubleshooting table helps map symptoms to causes:
| Symptom | Likely cause | Fix |
|---|---|---|
| Customer sees agent’s mobile | Agent called outside the platform | Lock processes, remove direct dialing path |
| Customer callback hits wrong line | Outbound caller ID showed real number | Force caller ID to use proxy or main business |
| Agent sees raw number in CRM | CRM stores and displays full CLI | Mask or partially mask numbers in the UI |
Handling late callbacks and expired bindings
Another subtle case is timing. If a customer calls back after the binding expired:
- The proxy number might already be assigned to another session.
- The flow may route them to a generic IVR, not the original agent.
That is not a privacy leak, but it can confuse people. The safe pattern is:
- Keep bindings alive long enough for reasonable callbacks (for example, 24–72 hours in support, shorter in on-demand services).
- If a callback hits an expired or unknown binding, send the caller to a smart IVR that can find their case by other data (ANI match, case number, etc.).
This way, I protect privacy and still give customers a clear path, even when they call back days later.
Conclusion
Masked phone numbers turn real CLIs into temporary proxies, so my contact flows can protect privacy, stay compliant, and still record, route, and bill calls with full control.
Footnotes
-
Twilio Proxy explains pooling and temporary proxy numbers for masked calling and texting. ↩ ↩
-
SIP RFC 3261 defines core headers like To and From used when platforms rewrite identities. ↩ ↩
-
ICO guidance explains the data minimisation principle for limiting where real phone numbers are stored. ↩ ↩
-
CTIA best practices describe standardized STOP opt-out handling that must still work through proxies. ↩ ↩
-
DPC guidance explains pseudonymisation and why keeping identifiers separate reduces exposure. ↩ ↩
-
CDR basics help design per-leg reporting and billing without exposing real numbers in everyday reports. ↩ ↩
-
RFC 3325 explains P-Asserted-Identity and trusted identity behavior that can affect masked caller ID presentation. ↩ ↩