Problems: confusing rates, blocked destinations, fraud risk.
Agitate: one mistake can burn budget and break compliance.
Solve: design dial plans, limits, and monitoring around long-distance.
Long-distance in VoIP means calls outside your local area, rated by destination prefixes. Your PBX normalizes numbers, picks a trunk, and enforces limits to keep costs and risk under control.

Your SIP carrier prices by E.164 dialing prefixes 1. Your system decides who may dial what, when, and how much. The core loop is simple: normalize to +E.164, match a route, apply limits, present a verified caller ID, then record outcomes. Do this well and long-distance becomes predictable and safe.
How do long-distance rates work on SIP trunks and carriers?
Pain: invoices show strange per-minute charges.
Agitate: hidden mobile/premium ranges spike cost.
Solve: map prefixes to rates, and route with quality and price in mind.
Carriers rate by destination prefix (country/area/mobile/premium). Your PBX selects routes using least-cost and quality rules. Rates change; keep a current tariff and alerts for unusual spend.
Dive deeper Paragraph:
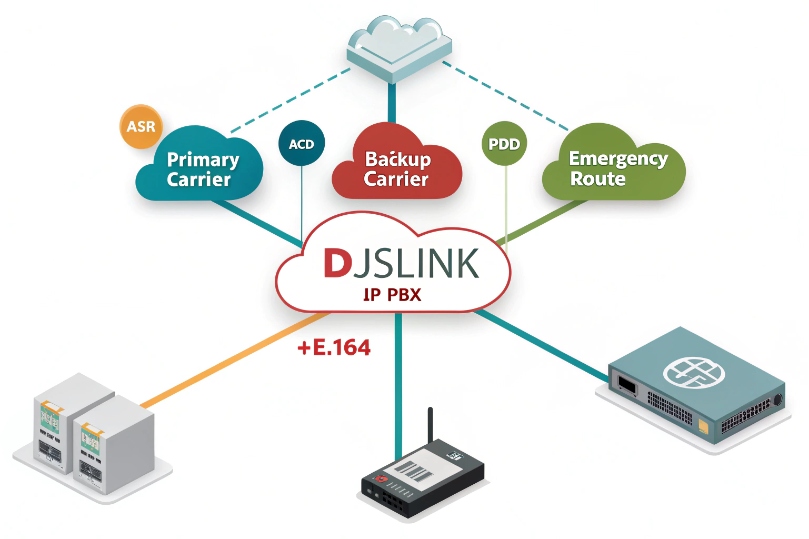
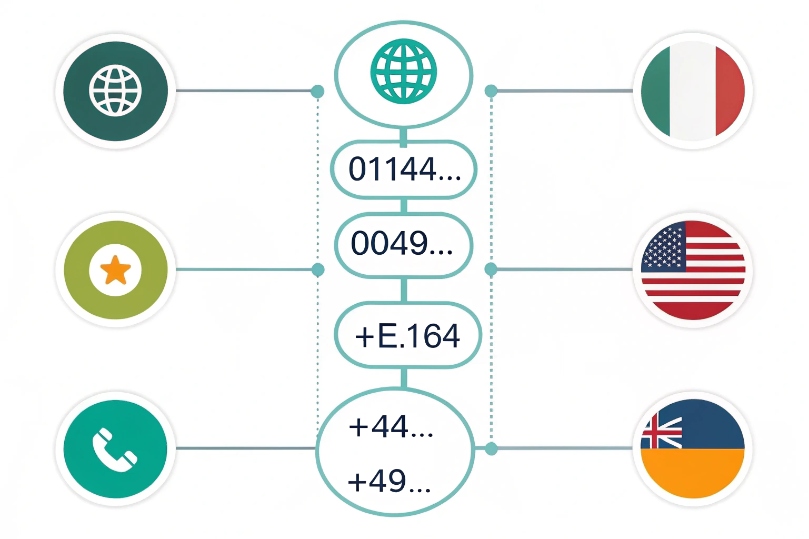
Every long-distance decision starts with the dialed number turned into +E.164. The carrier checks longest-prefix match against a tariff: country → region → operator → special range. Landline, mobile, premium, satellite, and shared-cost numbers all carry different prices, even inside the same country. That is why a “domestic” mobile call may cost more than a landline call, and why toll/short codes are often barred by default. Your PBX should maintain a route list per destination group: primary trunk, backup trunk, and a last-resort route for emergencies. Add least-cost routing (LCR) 2 with quality metrics like Answer-Seizure Ratio (ASR) and Average Call Duration (ACD) 3 to avoid cheap but unreliable routes that cause dead air. Store the carrier’s rate deck and your dial plan groups in the same place so finance can compare billed minutes to expected charges. Build alerts for daily cost anomalies and high-cost destinations (e.g., satellite, premium, or island countries). For multi-site teams, consider local breakout: route EU calls via an EU PoP and US calls via a US PoP to cut both latency and cost. Finally, reflect rates in user policy: sales may reach global mobiles; warehouse may reach domestic only. A simple table beats guesswork.
| Rate Dimension | Examples | Why Cost Varies | Control Lever |
|---|---|---|---|
| Country/Region | +1, +44, +61 | Distance, interconnect fees | Route by PoP/Trunk |
| Line Type | Landline vs Mobile | Mobile termination charges | Per-prefix policy |
| Special Ranges | Premium, satellite | High wholesale costs | Block or PIN |
| Time/Day | Peak vs off-peak | Some carriers still tier | Schedules/LCR |
| Quality | High ASR/ACD routes | Better costs more | Weighted routing |
Can I enable international dialing with country codes and limits?
Pain: staff cannot reach customers abroad.
Agitate: opening the world also opens risk.
Solve: enable +E.164 dialing with strict guardrails.
Yes. Normalize to +E.164, allow specific countries, and cap spend and duration. Require authorization codes for high-cost routes, and use class-of-service per user or group.
Dive deeper Paragraph:
Start with normalization. Accept user input like 011, 00, or bare national numbers and convert everything to +E.164. Publish a short user guide with examples by region so people know what to dial. Next, define allowlists by role: domestic only, domestic + select countries, and admin for full access. Keep a separate list for emergency international (government, embassy, or partner hotlines). Add per-call and per-day limits: cap maximum call duration (e.g., 60 minutes), cap daily spend (e.g., $20 per user), and cap concurrent international calls per site. For sensitive destinations, require an authorization code or account code (entered via DTMF before routing) to tag and approve the call. Use class-of-service at the PBX so desk phones, softphones, and common-area phones have different rights. On mobile apps, enforce the same rules; otherwise your softphone becomes a bypass. For flexibility, create a temporary window policy: let a manager enable a country for 24 hours for a project, then auto-disable. Always log who dialed, when, route used, CLI presented, duration, cost, and keep it searchable for audits. Pair this with a test list of international numbers per region so you can check reachability after changes.
| Control | Example | Default | Purpose |
|---|---|---|---|
| Country allowlist | +1, +44, +49 | Role-based | Reduce exposure |
| Max duration | 60 min/call | On | Limit run-away calls |
| Daily spend | $20/user/day | On | Contain fraud |
| Auth codes | Required for high-cost | On for premium/satellite | Accountability |
| Temporary enable | +66 for 24h | By request | Operational agility |
How do I block fraud and toll bypass on long-distance calls?
Pain: a single weekend hack can burn months of budget.
Agitate: fraudsters love premium islands and night hours.
Solve: layered controls on trunks, PBX, and user devices.
Block premium/unknown prefixes, set spend ceilings, enforce strong auth, and watch for anomalies. Lock remote access, disable SIP ALG quirks, and rate-limit attempts.
Dive deeper Paragraph:
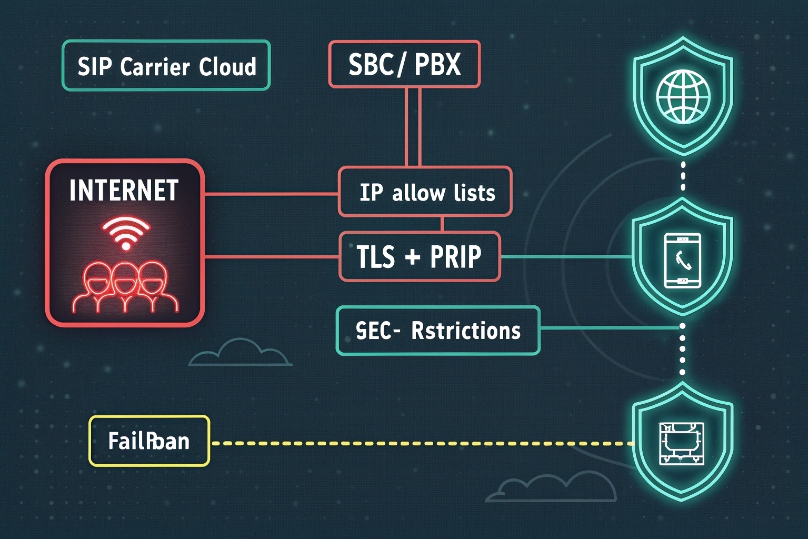
Most fraud starts with a weak credential, exposed portal, or open transfer rule. Begin at the edge: allow-list your PBX/SBC with the carrier, and restrict SIP registration to known IPs or geo regions. Use TLS + SRTP to prevent credential snooping. Encrypt RTP media with Secure Real-time Transport Protocol (SRTP) 4 where your endpoints and trunks support it. Disable unauthenticated DISA or IVR paths that can launch external calls without a PIN. On the PBX, block premium and satellite prefixes by default. Create a high-risk list (e.g., +882, +870, +262, +676, +297 premium ranges) and require manager approval. Add rate limiting and fail2ban-style bans for repeated failed attempts. Enforce least privilege: most users need domestic only. For administrators, use MFA on portals and separate accounts for daily work vs. change control. Turn on per-user/per-site spending caps with immediate lock when the threshold hits; release only with a ticket. Instrument real-time alerts: sudden call bursts after hours, long-duration calls to new countries, or spikes in short, failed attempts. For transfers, restrict forward-to-external and inspect rules after imports. Finally, keep CDRs and SIP logs for fast forensics. When you detect fraud, freeze international, rotate credentials, audit admin accounts, and provide your carrier with specific call-IDs for credit review.
| Risk Vector | Example | Mitigation |
|---|---|---|
| Stolen credentials | Bot guesses SIP passwords | TLS, strong auth, IP ACLs, MFA |
| Open transfer/forward | IVR → external | PINs, COS blocks, review rules |
| Premium destinations | +882/+870 | Block by default, auth codes |
| Off-hours bursts | 2 AM runs | Schedules, alerts, caps |
| Portal exposure | Weak admin login | MFA, RBAC, audit logs |
Will long-distance affect caller ID, E911, and compliance rules?
Pain: calls fail or show “Unknown.”
Agitate: wrong IDs hurt answer rates and break laws.
Solve: verify CLIs, map emergency routing, and respect local rules.
Yes. Outbound caller ID must be verified and reachable. E911 ties to your DID, not the destination. Some countries require local CLIs or will mask unverified IDs. Align recording and consent per region.
Dive deeper Paragraph:
Caller ID (CLI/CNAM): Many carriers require that your outbound CLI is a verified DID you own. International carriers often block or reformat numbers that are not valid in E.164 or not reachable back. Some countries demand a local in-country CLI; others prohibit CLI spoofing entirely. If your brand needs a local identity, buy a local DID and present that per route. Keep STIR/SHAKEN caller ID authentication 5 aligned on domestic legs; outside the US/CA, other frameworks or none may apply. CNAM dips are usually domestic-only; do not expect your name to show abroad.
E911: Emergency calling follows your originating DID and registered address, not whether the call is long-distance. Make sure every device and user has a correct dispatchable address and meets dispatchable location requirements 6. Long-distance outbound rules must not intercept or hairpin 911/112/999 flows. Test with 933 where supported.
Recording and consent: Laws differ. Some countries require two-party consent; others allow one-party. If you record calls or run AI transcription, prompt and capture consent per destination and agent location. Store audio and metadata per your retention policy and regional privacy laws.
Data jurisdiction: If you route via cloud SBCs, confirm where media and metadata traverse and rest. Some industries require data residency.
Branding and answer rates: For sales and service lines, use in-country DIDs and present a familiar CLI to improve answer rates while staying compliant. Keep return call flows ready on those DIDs.
| Area | What to Check | Typical Action |
|---|---|---|
| Outbound CLI | Verified +E.164 | Per-route caller ID policies |
| Local CLI rules | Some countries require local | Buy local DID, map trunk |
| STIR/SHAKEN | Domestic enforcement | Sign where applicable |
| E911 | Device address mapping | 933 test, lock bypass |
| Recording | Consent by region | IVR notice, agent script |
Conclusion
Define rates and routes, enable countries with limits, and lock fraud doors. Keep caller ID verified, E911 clean, and rules by region. Long-distance will be predictable, safe, and clear.
Footnotes
-
Understand E.164 formatting so your dial plan normalizes numbers consistently across carriers. ↩ ↩
-
See how LCR selects routes by price and quality so you can control costs and reachability. ↩ ↩
-
Reference ASR and ACD definitions to evaluate carrier quality and spot bad routes quickly. ↩ ↩
-
Read the SRTP standard to understand how media encryption protects RTP voice streams. ↩ ↩
-
Review FCC guidance on STIR/SHAKEN caller ID authentication and related call-blocking obligations. ↩ ↩
-
Check FCC MLTS 911 rules for dispatchable location requirements and direct-dial expectations in VoIP systems. ↩ ↩











