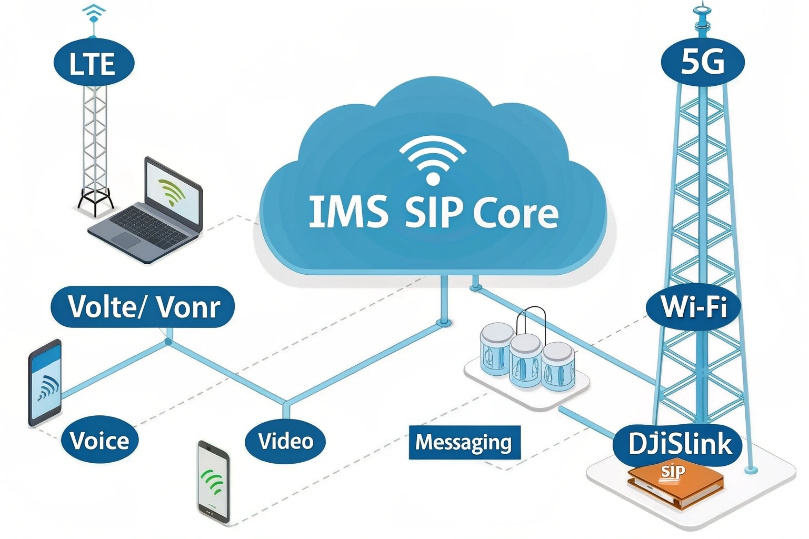
Users want mobile-grade voice everywhere. Outages and jitter erode trust. IMS promises consistency across LTE, 5G, and Wi-Fi.
IMS is a 3GPP SIP-based core that delivers voice, video, and messaging over IP. It decouples services from access and unifies control across mobile and fixed networks.
Carriers built IMS for telecom reliability under a 3GPP IMS architecture 1. Enterprises now interconnect to it with SIP trunks and SBCs. The result is predictable quality, roaming support, and a path to VoLTE (Voice over LTE) 2, VoWiFi (IMS voice over WLAN) 3, and converged services.
How does IMS architecture work—CSCF, HSS, and SBCs?
Teams struggle with many moving parts. Without a map, troubleshooting feels random. IMS breaks roles into clean blocks that scale.
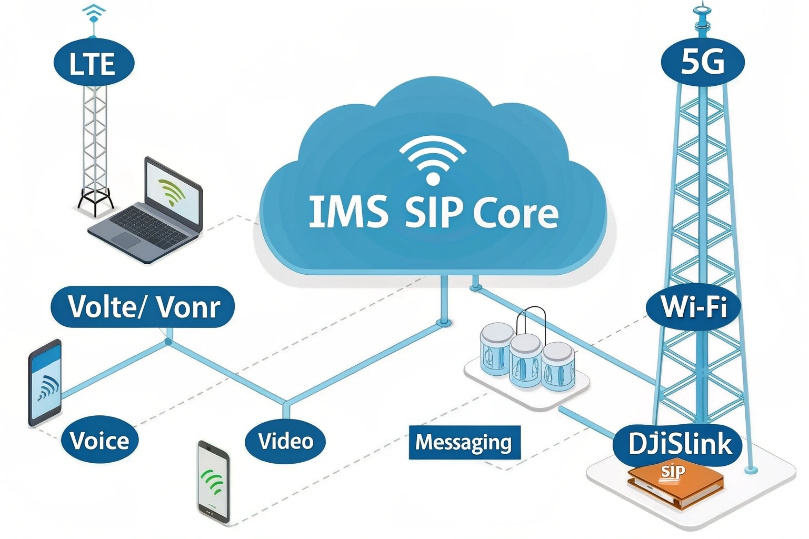
IMS uses P-CSCF, I-CSCF, and S-CSCF SIP control functions 4 for SIP control; HSS/UDM for subscribers; and SBCs plus gateways for borders and PSTN.
Dive deeper Paragraph:
The control plane at a glance
- P-CSCF (Proxy-CSCF): First hop for the device (UE, PBX, or SBC). It enforces policy, compresses SIP if needed, and anchors security (IPsec or TLS).
- I-CSCF (Interrogating-CSCF): Front door to the home network. It queries the HSS/UDM to locate the right S-CSCF for the user.
- S-CSCF (Serving-CSCF): Brain for registration and service logic. It applies initial filter criteria and routes to Application Servers (AS) for features like call forwarding, barring, or supplementary services.
Subscriber data and policy
- HSS/UDM: Stores identities (IMPI/IMPU), service profiles, and authentication vectors for IMS-AKA, and commonly interfaces using the Diameter base protocol 5.
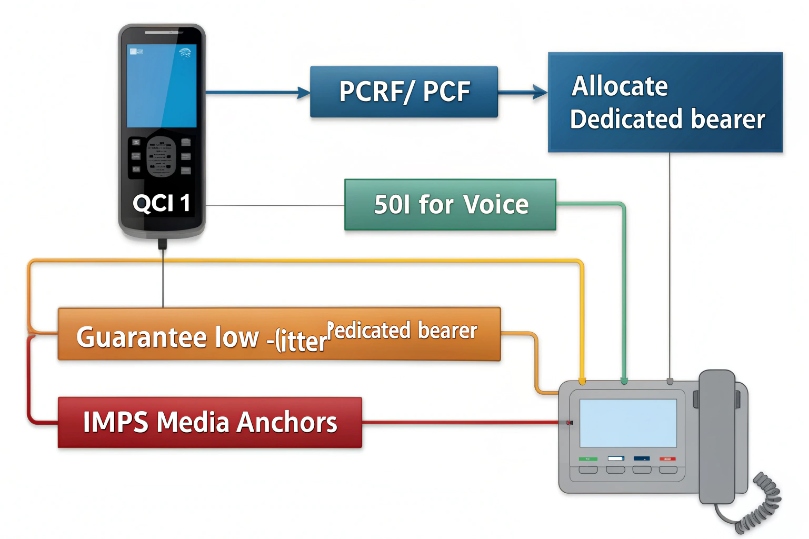
- PCRF/PCF: Issues policy and QoS decisions. It binds sessions to bearers with QCI (4G) / 5QI (5G) so media gets priority and bandwidth.
Media and interworking
- BGCF/MGCF/MGW: Bridge SIP to the PSTN/CS domain when needed. MGW handles RTP/TDM conversion. BGCF chooses the right breakout.
- SBCs: Sit at edges for topology hiding, SIP normalization, NAT traversal, SRTP anchoring, and DDoS control. They also enforce interconnect policy and number formats (E.164/ENUM).
Why this separation helps
Clear roles make scale easier. You add S-CSCF instances to handle registrations. You expand AS clusters to add features. You extend SBC capacity at peering edges without touching subscriber data. Troubleshooting also improves: registration issues point to S-CSCF/HSS; media asymmetry points to SBC/MGW; QoS mismatches point to PCRF/PCF.
| Block | Primary role | Typical protocols |
|---|---|---|
| P-/I-/S-CSCF | SIP control, routing, services | SIP, Diameter |
| HSS/UDM | Identities and auth vectors | Diameter (Cx, Sh), Nudm |
| PCRF/PCF | Policy and QoS control | Diameter (Gx, Rx), HTTP/2 in 5G |
| SBC | Security and interconnect | SIP/TLS, SRTP, ENUM |
| BGCF/MGCF/MGW | PSTN/CS interworking | SIP, ISUP/BICC, RTP/TDM |
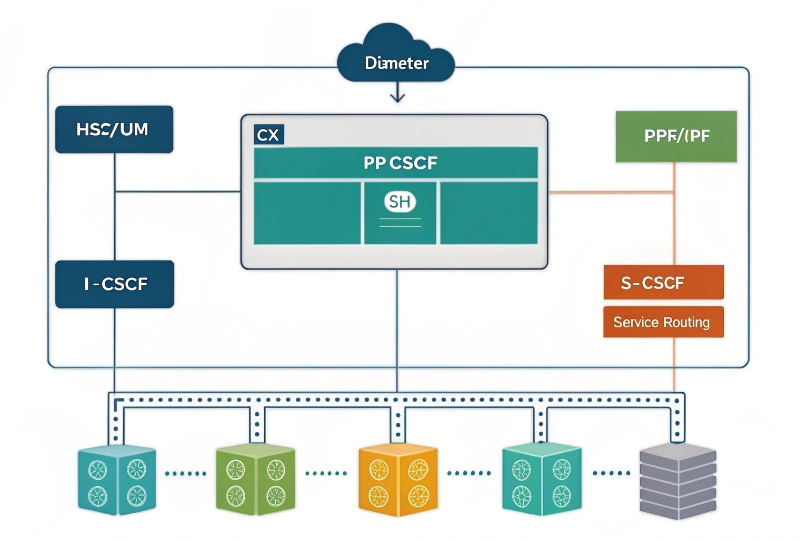
Can I integrate IMS with SIP trunks, PBX, and VoLTE?
Yes. IMS was designed to interconnect. The trick is to speak clean SIP, present numbers in E.164, and let SBCs normalize differences.
You can terminate enterprise SIP trunks into IMS, register PBXs, and bridge mobile services like VoLTE/VoNR and VoWiFi.
Dive deeper Paragraph:
Enterprise paths that work
- SIP trunks to IMS: Your enterprise SBC forms a trunk to the operator’s IMS SBC. You exchange E.164 DIDs. The operator handles number portability and routing. You gain carrier-grade QoS and reach.
- PBX registration: Some operators allow enterprise PBXs or SBCs to register as UEs. Others use static peering. In both models, the IMS edge SBC normalizes headers, codecs, and timers so the PBX does not need mobile-specific logic.
- VoLTE/VoNR/VoWiFi bridging: Calls from mobile devices hit the S-CSCF, then hairpin through IMS AS/SBC toward your enterprise trunk. S8HR or LBO roaming models decide if media stays local or crosses back to the home network. This impacts end-to-end latency.
Service interworking
- Supplementary services: IMS AS can host forwarding, hunt, and barring. Your PBX features can coexist if you avoid feature “echo.” Decide which side owns each service.
- Messaging: SMS over IP and RCS can pass via IMS messaging AS. For enterprise, many keep SMS/MMS on separate APIs to reduce coupling.
- Emergency calling: IMS supports E911/E112 with location conveyance and emergency bearers. If your PBX sends calls to IMS, align emergency routing, ELIN/ERLs, and callback handling.
Practical integration tips
- Normalize CLI to E.164 (+countrycode).
- Choose codecs both sides support (AMR-WB ↔ G.722/Opus/G.711 via transcoding at SBC/MGW if needed).
- Keep SRTP end-to-end where possible; transcode only at anchors you control.
- Test early media, PRACK/100rel, UPDATE, and session timers. Mobile cores rely on these for seamless call setup.
- Document ENUM and portability flows so enterprise dial plans do not fight carrier routing.
| Integration case | Best anchor | Notes |
|---|---|---|
| Enterprise SIP trunk | SBC ↔ IMS SBC | Static IPs, mutual TLS, E.164 |
| PBX as UE | P-CSCF/S-CSCF | IMS-AKA or NNI creds; timers |
| Mobile to PBX | IMS AS/SBC | Pay attention to roaming path |
What benefits does IMS offer for QoS, roaming, and scalability?
Voice fails when quality dips or when users roam. IMS was built to fix both at carrier scale.
IMS gives bearer-level QoS, controlled roaming behavior, and horizontal scale across services and geographies.
Dive deeper Paragraph:
QoS that is enforced, not hoped
- Policy control (PCRF/PCF): The control plane binds SIP sessions to dedicated bearers using 3GPP Policy and Charging Control (PCC) 6. This sets bandwidth, delay, and priority for RTP/SRTP. It is more than DSCP; it is end-to-end enforcement across the mobile packet core.
- Consistent MOS: Because bearers are reserved, voice sees stable delay and low jitter even under load. For fixed networks, operators map IMS policy to QoS in their IP/MPLS core and at peering.
Roaming that does not break calls
- Visited P-CSCF selection lets devices register close to where they are.
- Roaming models:
- S8 Home Routing (S8HR): Control and sometimes media go back to home IMS. Simple billing, higher latency.
- Local Breakout (LBO): Media breaks out locally. Better latency, more complex policy and charging.
- Emergency services work in roam with correct routing and priority bearers.
Scale that adds features, not pain
- Cloud-native IMS lets operators scale CSCFs, SBCs, and AS independently. You can add RCS, conferencing, or video calling without touching the access layer.
- IPv6-first deployments reduce NAT pain. SBCs handle IPv4/IPv6 interworking for enterprises still on v4.
- Migration aids like SR-VCC/eSR-VCC hand calls from LTE/5G to legacy CS if coverage drops.
| Benefit | How IMS delivers | What you notice |
|---|---|---|
| QoS | Dedicated bearers (QCI/5QI) + policy | Fewer jitter spikes, stable MOS |
| Roaming | Visited P-CSCF + S8HR/LBO | Fewer drops, predictable delay |
| Scale | Separated planes + AS | Faster feature rollout |
How do I secure IMS—authentication, encryption, and interconnects?
Security must be native, not bolted on. IMS bakes identity, crypto, and border policy into the control plane.
Use IMS-AKA for devices, protect signaling with IPsec or TLS, encrypt media with SRTP, and lock down interconnects with SBCs.

Dive deeper Paragraph:
Device and user authentication
- IMS-AKA: UEs authenticate with USIM/ISIM credentials. P-CSCF and S-CSCF coordinate with HSS/UDM to challenge and verify.
- Enterprise trunks: Use mutual TLS with certificates or strong credentials. Avoid anonymous trunks. Rotate keys and enforce modern ciphers.
Signaling and media protection
- UE ↔ P-CSCF: Common profiles use IPsec ESP for SIP. Many fixed/enterprise interconnects use TLS for SIP.
- Media: Use Secure Real-time Transport Protocol (SRTP) 7 for confidentiality and integrity. Keys via SDES (within TLS) or DTLS-SRTP. Keep payload secure end-to-end where possible; decrypt only at controlled SBC/MGW anchors.
Interconnect hardening
- SBC edges perform topology hiding, SIP header normalization, rate limiting, and DDoS scrubbing. They also do NAT traversal and media anchoring to stop hairpins.
- Numbering hygiene: Enforce E.164 and use ENUM and portability databases to block spoofing and misroutes.
- Fraud controls: Limit call rates, apply call admission control, and monitor anomalous destinations.
Operational items that close gaps
- Certificate management: Short-lived certs and automated renewal.
- Logging and LAES: Keep legal intercept and audit trails as required.
- Idle timers and session policies: Kill zombie registrations, cap early media, and enforce sane retry logic.
- SIP ALG off on non-SBC firewalls. Let the SBC own SIP awareness.
| Layer | Mechanism | Goal |
|---|---|---|
| Identity | IMS-AKA / mTLS | Strong auth |
| Signaling | IPsec ESP / TLS | Integrity + privacy |
| Media | SRTP (SDES/DTLS) | Confidential audio/video |
| Edge | SBC policies | Interop + protection |
Conclusion
IMS is the carrier-grade SIP core behind VoLTE/VoNR and VoWiFi. Tie your PBX and trunks to it with SBCs, use its QoS and roaming strengths, and secure every hop with AKA, TLS/IPsec, and SRTP.
Footnotes
-
3GPP spec defining IMS architecture, entities, and reference points. ↩︎ ↩
-
LTE core network architecture reference that underpins VoLTE service delivery and bearer behavior. ↩︎ ↩
-
Non-3GPP access architecture reference supporting IMS voice over Wi-Fi and trusted/untrusted WLAN access. ↩︎ ↩
-
IMS call control spec describing CSCF behavior, registration, and session handling. ↩︎ ↩
-
Diameter protocol fundamentals used for subscriber, authentication, and policy signaling in telecom cores. ↩︎ ↩
-
3GPP PCC specification explaining policy/QoS control and bearer binding for media prioritization. ↩︎ ↩
-
SRTP standard detailing RTP encryption, integrity protection, and operational considerations for secure media. ↩︎ ↩