Missing recordings cause disputes after incidents. In hazardous sites, that risk is bigger. A clear recording plan keeps evidence solid and operations calm.
Yes, explosion-proof SIP telephones can work with call recording servers, but the recorder usually integrates with the PBX/SBC, not the handset. SIPREC is the cleanest method. Port mirroring works only when RTP is visible and not SRTP-encrypted.

Recording compatibility: what makes an Ex telephone “recording-ready”?
Recording is a system function, not a handset checkbox
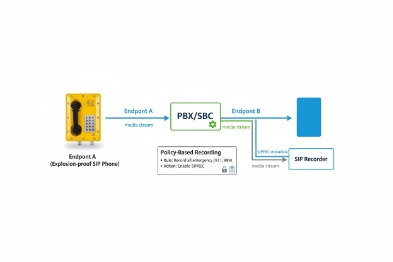
A rugged Ex telephone is a SIP endpoint. Most recording happens in the call control layer. The PBX, SBC, or B2BUA 1 sees signaling and media, so it can copy streams and metadata to the recorder. The handset often does not need to “support recording” at all. What matters is whether the endpoint behaves in a standard way and whether the network design lets the recorder capture what it needs.
Three recording architectures used in refineries and terminals
Most projects use one of these paths:
1) SIPREC from PBX/SBC to a recorder
This is the cleanest for audits. The recorder gets media plus metadata such as call IDs, parties, and timing. It also works well when calls are peer-to-peer or move across multiple switches.
2) Media forking at the SBC/B2BUA
Some systems fork RTP to a recorder or a media relay. It is strong for mixed vendors. It also centralizes recording at the boundary where security teams already place SBCs.
3) Port mirroring / SPAN capture
This copies packets to a recorder NIC. It can work in small networks. It can fail in real plants when RTP stays local between two endpoints, or when SIP and RTP are encrypted (SIPS/SRTP). It also needs careful switch capacity planning.
What to request from vendors and integrators
A good procurement checklist focuses on proof, not promises:
| Item to confirm | What “good” looks like | Why it matters |
|---|---|---|
| Recording method | SIPREC or SBC forking preferred | Works across complex networks |
| RTP visibility | RTP flows through the recording point | Port mirroring fails without this |
| Encryption plan | Recorder supports SRTP keys or media path | Passive capture cannot decrypt SRTP |
| Metadata | Call-ID, extension, timestamps, reason codes | Makes evidence usable |
| Time sync | NTP across PBX/recorder/endpoints | Aligns logs during audits |
A simple rule helps: if the project needs audit-grade recordings, plan recording around the PBX/SBC and time sync. Do not depend on a passive tap at the edge.
The next sections break down each key question. Each one can be turned into a clear line in your tender, so suppliers respond with real evidence and not vague marketing words.
Which recording methods work—SIPREC, port mirroring, or SPAN to the recorder?
Recording gaps often come from choosing a “cheap” capture method that cannot see the media. A plant network is not a lab. A safer method prevents rework later.
SIPREC is the most reliable choice because it sends media and metadata from the PBX/SBC to the recorder. SPAN/port mirroring can work, but only if SIP and RTP traverse the mirrored link and remain unencrypted or the recorder is in the media path.
SIPREC: clean media plus clean metadata
SIPREC 2 is designed for recording. It typically runs between a Session Recording Client (in the PBX/SBC) and a Session Recording Server (the recorder). The recorder receives:
-
the media stream(s)
-
and a clear set of metadata that explains who called whom, when, and why
This matters in refineries because the same phone can be used for normal operations, emergency calls, and drills. Without metadata, recordings become a pile of audio files with no meaning.
SPAN/port mirroring: simple, but easy to break
Port mirroring copies traffic from a switch port or VLAN to a monitoring port. It sounds perfect. In practice, two issues show up:
-
RTP may not pass the mirrored point. Many SIP calls send RTP directly between endpoints. If the recorder mirrors a gateway port, it may miss internal calls.
-
Encryption can make the capture useless. If the site enables SIPS and SRTP, the recorder sees packets but cannot decode them.
Port mirroring still works well for:
-
troubleshooting and temporary capture
-
small systems where all RTP flows pass a central point
-
legacy systems that do not support SIPREC
A practical decision table for heavy industry
| Method | Best fit | Main risk | What to demand in writing |
|---|---|---|---|
| SIPREC | Audit-grade recording | Needs PBX/SBC support | “SIPREC supported with metadata and timestamps” |
| SBC media forking | Multi-vendor systems | Extra SBC configuration | “Fork RTP + preserve call IDs” |
| SPAN/mirroring | Small networks, diagnostics | Missed RTP, SRTP blocks decode | “Show where RTP flows and show capacity plan” |
For most hazardous-area projects, the safe move is SIPREC or SBC-based recording. Port mirroring should be treated as a special case, not the default.
Do SIP endpoints support dual registration or B2BUA passthrough for lawful intercept?
A common request is “dual registration” so the recorder sees calls. That idea often creates instability and is hard to secure.
Most SIP endpoints should not dual-register to a recorder. The better path is a PBX/SBC that acts as a B2BUA and provides SIPREC or controlled forking. Lawful intercept workflows are usually implemented in the network and call control layer, not inside the handset.

Dual registration sounds easy, but it is not a safe default
Dual registration means one endpoint registers to two SIP servers. In real deployments it can cause:
-
split routing and missed calls
-
confusing authentication rules
-
inconsistent SRTP key handling
-
hard-to-audit behavior during failover
In hazardous sites, reliability matters more than clever tricks. A phone should register to the PBX that owns call routing and emergency rules.
B2BUA/SBC passthrough is the clean control point
A B2BUA (often the PBX or SBC) terminates and re-originates calls. That gives one place to:
-
apply recording policy by extension, by group, or by call type
-
enforce encryption consistently
-
create a stable path to the recorder
This also matches how plants manage change. The SBC 3 is already a controlled device. The handset is often deployed in the field with limited access.
Lawful intercept: keep it policy-driven and logged
“Lawful intercept” 4 is a sensitive topic and it is controlled by local law and customer policy. From a technical point of view, the safest approach is:
-
implement recording rules in the PBX/SBC
-
produce a clear audit trail of who has access
-
store recordings with integrity checks and retention rules
A handset-level intercept feature is rarely desired in industrial B2B projects because it adds risk and is hard to govern.
A simple compliance-friendly approach
| Need | Safer design | Why it is safer |
|---|---|---|
| Record all emergency calls | PBX/SBC policy + SIPREC | Central control and consistent metadata |
| Record certain extensions | Role-based rules in recorder | Clear access control and logs |
| Keep encryption on | SRTP end-to-end with recorder in the media plan | Avoids passive capture failures |
| Provide audit evidence | NTP + CTI events + immutable storage | Defensible timelines |
If a vendor claims “dual registration for recording,” it is smart to treat that as an exception and ask for real test evidence under failover and SRTP.
What codecs and security are supported—G.711/G.722/Opus, SIPS, SRTP, and HTTPS control APIs?
Recording fails when the recorder cannot decode the codec or cannot receive keys for encrypted media. Many projects discover this only after installation.
G.711 is the safest codec for recording compatibility. G.722 is common for wideband voice. Opus can be used, but recorder support varies and may require transcoding. If SIPS and SRTP are enabled, the recorder must integrate through SIPREC or be in the media path, because passive capture cannot decode encrypted media. HTTPS APIs help manage retention, export, and audit controls.
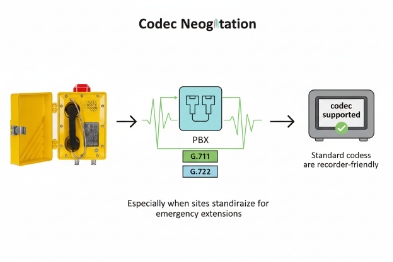
Codec reality in plants
For incident evidence, clarity and compatibility matter. Many industrial customers choose:
-
G.711 for maximum interoperability and simple playback
-
G.722 when wideband 5 improves understanding in noisy environments
-
Opus when the platform supports it end-to-end, including recorder decoding
A practical point: even if endpoints support Opus, many recorders store in a standard format. Some recorders can transcode. Some cannot. If transcoding is needed, plan CPU capacity and quality impact.
Security reality: encryption changes the recording design
Encryption is good. It also changes how recording works:
-
SIPS (SIP over TLS) hides signaling from passive capture.
-
SRTP encrypts media, so a SPAN recorder cannot decode it.
So the recording plan should match the security plan. The system can stay secure and still record, but the recorder must be integrated in a supported way.
Control APIs: what they should be used for
HTTPS control APIs are not just a “nice feature.” They support:
-
automated export for incident management
-
retention policies by call type
-
role-based access and audit logs
-
integration with case management tools
In a refinery, this saves time after an incident because teams can retrieve the right recording fast, with the right chain of custody.
A codec and security checklist table
| Topic | Preferred default | What to verify during FAT |
|---|---|---|
| Codec | G.711 6 (baseline) | Recorder can decode and store correctly |
| Wideband | G.722 | Quality in high-noise environments |
| Modern codec | Opus (optional) | End-to-end support or transcoding plan |
| Signaling security | SIPS | Recorder still receives metadata |
| Media security | SRTP | Recorder gets media through SIPREC/media path |
| Management | HTTPS API | Access control, logs, export workflow |
When codec and security are aligned, recording becomes predictable. When they are not aligned, the site ends up disabling SRTP or losing recordings. Neither outcome is acceptable in serious industrial deployments.
How can PBX/VMS integration ensure auditability—CTI/API events, RTSP streams, and NTP-synced timestamps?
Recordings are only useful when they can be trusted. A single missing timestamp or missing extension mapping can make evidence weak.
Auditability comes from complete metadata, reliable event feeds, and consistent time. Use PBX CTI/API events for call start/stop and identities, use SIPREC metadata when possible, record video via RTSP in the VMS when video is involved, and keep PBX, recorder, and NVR on the same NTP reference.
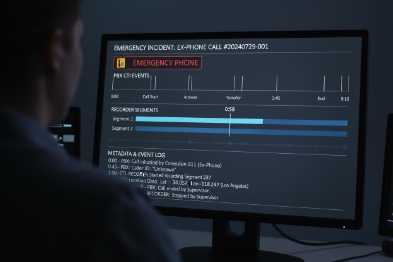
Use CTI/API events to tie audio to identities and actions
Call audio alone is not enough. Plants need:
-
who pressed the emergency key
-
which device triggered the alarm
-
who answered
-
how long it took
-
and what follow-up paging happened
CTI 7 or PBX APIs can provide reliable event records:
-
call start, call answer, call end
-
call direction
-
extension IDs and device IDs
-
reason codes and routing decisions
These events should be stored with the recording so the file is self-explaining.
Video intercom: record video in the VMS, not in the handset
If the Ex phone is paired with a camera, video recording normally belongs in the VMS:
-
RTSP streams go to the NVR
-
events from the phone or PBX create bookmarks
-
operators can pull video and audio evidence together
This split approach works because VMS platforms are built for video retention and export workflows.
Time sync is the glue that makes evidence defensible
Audit-grade systems require aligned timestamps. The clean model is:
-
all systems sync to the same on-prem NTP servers
-
logs store UTC or store timezone with clear rules
-
exports include timestamps and device IDs
If systems drift, the incident timeline becomes confusing. A strong project sets drift thresholds 8 and alarms when NTP sync is lost.
A simple “audit pack” the customer can request
| Evidence item | Source | What it proves |
|---|---|---|
| Audio recording | Recorder | Content of the call |
| Call metadata | SIPREC or PBX | Who, when, and where |
| Event log | CTI/API + syslog | Routing and alarm actions |
| Video clip | VMS/NVR 9 via RTSP | Visual verification when needed |
| Time proof | NTP logs | Trust in timestamps |
This approach scales across terminals and multiple plant areas. It also reduces post-incident workload because the evidence is already organized.
Conclusion
Explosion-proof SIP telephones work well with recording servers when recording is done at the PBX/SBC using SIPREC, with codecs 10 and SRTP planned, and with NTP-aligned logs across voice and VMS.
Footnotes
-
[Back-to-Back User Agent, a SIP element that mediates calls between endpoints for control and security.] ↩
-
[Standard protocol for session recording, enabling the capture of SIP sessions and metadata.] ↩
-
[Session Border Controller, a device used to secure and manage VoIP networks.] ↩
-
[Legal requirement for telecommunications networks to allow authorized monitoring of communications.] ↩
-
[Audio technology that extends the frequency range of transmitted sound for better clarity.] ↩
-
[ITU-T standard for audio companding, commonly used in digital telephony.] ↩
-
[Computer Telephony Integration, allowing computers to manage telephone calls.] ↩
-
[Limits set for acceptable time deviation in synchronized network clocks.] ↩
-
[Network Video Recorder, a specialized computer system for recording video surveillance footage.] ↩
-
[Algorithms used to compress and decompress digital audio and video data.] ↩











