Weak port security can let the wrong device join the voice VLAN. A single mistake can disrupt dispatch and emergency calling.
Most SIP explosion-proof telephones can act as 802.1X supplicants, but EAP method coverage varies by firmware. Treat EAP-TLS and PEAP as feature items that must be proven in FAT.

How to read 802.1X support on an Ex telephone without getting trapped by marketing
What “802.1X supported” should mean on a hazardous-area phone
Many vendors write “802.1X 1” on a datasheet. That is not enough. A real plant rollout needs answers to four points:
-
Which EAP method the phone can use (EAP-TLS 2, PEAP 3, EAP-TTLS, others)
-
Which TLS version and cipher sets the supplicant supports
-
How certificates and keys are stored and provisioned
-
What happens when authentication fails, especially for emergency calling
Explosion-proof phones often run embedded SIP 4 stacks. Some stacks expose only one or two EAP methods. Some expose several methods but with limited TLS control. The safest assumption is simple: capabilities differ by model and firmware. That is why each project should lock the exact firmware and do one packet capture during FAT.
A practical selection ladder for real sites
The security goal is to stop unknown endpoints from joining the voice network, while keeping phones reachable for emergency operations. This ladder works in most plants:
1) Prefer EAP-TLS for new deployments where a PKI 5 exists
2) Use PEAP-MSCHAPv2 only when certificate logistics are not ready
3) Avoid weak methods like EAP-MD5 and avoid “open ports” except as a controlled emergency policy
4) Add a survivable method so emergency calling still works when 802.1X is down
What to demand in a compliance-ready submittal
A procurement package should include:
-
a feature statement listing supported EAP methods and TLS versions
-
a hardening guide for certificate and password handling
-
a switch/RADIUS interoperability note (tested platforms and settings)
-
a FAT checklist that includes link-up, auth success, auth failure, and recovery after reboot
EAP method choice in one table
| EAP method | Security level | Operational effort | Best-fit use |
|---|---|---|---|
| EAP-TLS | High | Higher (PKI needed) | refineries, terminals, long-life assets |
| PEAP-MSCHAPv2 | Medium | Medium (user/pass lifecycle) | transitional projects and mixed IT/OT |
| EAP-TTLS | Medium–High | Medium | when client support exists and policy requires it |
| EAP-MD5 | Low | Low | not recommended for voice security |
This is the baseline. The next sections answer your specific questions in a way that can be copied into a specification and FAT script.
Are EAP-TLS and PEAP-MSCHAPv2 both available?
A phone that supports only one method can still be secure, but it can force painful changes in the network policy.
Many SIP explosion-proof telephones offer EAP-TLS and PEAP-MSCHAPv2, but it is not universal. The real check is whether the supplicant can import a client certificate for EAP-TLS and can store PEAP credentials safely for PEAP-MSCHAPv2.

Why EAP-TLS is the cleanest long-term option
EAP-TLS uses mutual authentication. The phone proves identity with a client certificate. The network proves identity with the RADIUS 6 server certificate. This reduces the risk of credential reuse and password drift. It also scales better over a 10–15 year asset life because there is no shared password that installers copy into notebooks.
EAP-TLS still needs discipline:
-
Unique device certificates per phone
-
A controlled CA chain
-
A revocation or rotation story
-
A plan for lost devices and RMA replacements
Why PEAP-MSCHAPv2 still exists in plants
PEAP-MSCHAPv2 is common because it is familiar to IT teams. It can be deployed quickly using username/password logic. It is also easier in mixed fleets where not every endpoint can store a private key securely.
The trade is operational:
-
passwords expire
-
passwords get copied
-
password resets become outages
-
shared accounts create audit noise
What to verify on the phone UI and on the wire
A real support claim should show these items:
-
EAP method dropdown includes EAP-TLS and PEAP
-
Fields exist for CA certificate, client certificate, and private key (for EAP-TLS)
-
Fields exist for identity, anonymous identity (optional), and password (for PEAP)
-
The handshake succeeds with your RADIUS server policy and does not fall back silently
FAT steps that prevent late surprises
-
Authenticate with EAP-TLS and confirm the certificate chain is accepted
-
Rotate a certificate (or replace it) and confirm the phone recovers cleanly
-
Authenticate with PEAP and confirm password changes do not brick the phone
-
Verify voice VLAN assignment and QoS policy after authentication
If only one method is available, the network can still be safe. The project just needs to align the RADIUS policy and provisioning flow to that single method.
Can device certificates be provisioned securely at scale?
Manual certificate loading is fine for ten units. It is painful for 500 units across multiple countries.
Yes, secure certificate provisioning is possible at scale, but the method must match the phone platform. The best options are factory-injected unique certificates, SCEP/EST enrollment, or a controlled provisioning server that installs certificates over a protected channel.

What “secure provisioning” should look like
A scalable and auditable approach has these traits:
-
Each phone has a unique identity (certificate subject or SAN)
-
The private key is not emailed, not shared, and not reused
-
Enrollment is tied to a controlled process (serial number, purchase order, or onboarding list)
-
The device can be re-enrolled after repair without losing traceability
Three practical provisioning models that work in B2B deployments
1) Factory-injected certificates (best for predictable rollouts)
A supplier can inject a unique keypair and certificate at the factory, then provide the CA chain and mapping list to the client. This reduces field work and reduces key leakage risk.
Key checks to require:
-
proof that private keys are unique per device
-
a list export that maps serial number to certificate identity
-
a change-control note so OEM branding does not replace the supplicant stack
2) SCEP/EST enrollment (best for IT-managed PKI)
If the phone supports certificate enrollment protocols, the phone can request a certificate after first boot. This is strong when the enterprise already runs a PKI and wants short-lived certificates.
Key checks:
-
secure bootstrap identity (how does the device earn trust on day one?)
-
renewal behavior (will it renew before expiry without downtime?)
-
failure behavior (what happens if PKI is temporarily unreachable?)
3) Secure provisioning server (best when phones are centrally managed)
Many plants already use provisioning for SIP accounts. The same system can deliver 802.1X settings and certificates. This can be secure if:
-
provisioning is protected (TLS, strong admin control)
-
certificate files are encrypted at rest
-
the provisioning event is logged and repeatable
A scaling checklist for procurement
| Topic | What to require | Why it matters |
|---|---|---|
| Uniqueness | unique cert per device | avoids fleet-wide compromise |
| Storage | protected private key handling | prevents extraction and cloning |
| Rotation | renewal workflow defined | avoids expiry outages |
| Audit | logs and mapping export | supports compliance reviews |
| RMA flow | re-issue and revoke plan | keeps identity clean after replacement |
If the project cannot guarantee secure key storage on the device, a safer pattern is to treat the phone as a managed endpoint in a tightly controlled voice VLAN, then layer security with switch controls and monitoring.
Is TLS 1.2+ with modern ciphers enforced?
Some phones claim “supports TLS 7,” but that can mean old TLS versions and weak ciphers, which modern RADIUS policies will reject.
A modern deployment should enforce TLS 1.2 or newer for EAP methods that use TLS (EAP-TLS and PEAP). The phone must also support modern cipher suites that the RADIUS server policy allows. This should be proven by validating the negotiated TLS version in a capture.

What “modern” means in a plant reality
Most enterprise security baselines now reject:
-
TLS 1.0 and TLS 1.1
-
old ciphers like RC4 and many 3DES profiles
-
weak key sizes and weak certificate chains
The phone must match the RADIUS server policy. Even if the phone supports TLS 1.2, it can still fail if it only offers older RSA key exchange suites that your server forbids.
The two certificate checks that matter most
-
The phone must trust the RADIUS server certificate chain
-
The phone must validate the server identity (or the deployment becomes vulnerable to rogue RADIUS)
In PEAP deployments, skipping server validation is a common “quick fix.” It is also a common audit finding. It should be avoided.
A simple verification method that works every time
During FAT:
-
run a packet capture at the switch mirror port
-
confirm the TLS version used in the EAP handshake
-
confirm the cipher suites 8 used
-
confirm the certificate chain and server identity checks pass
If the phone cannot meet TLS 1.2 requirements, the correct fix is not to weaken the RADIUS server. The correct fix is to choose a phone firmware or model with a modern supplicant.
A short hardening table for the spec
| Control | Preferred setting | Why |
|---|---|---|
| TLS version | TLS 1.2+ | aligns with modern baselines |
| Server validation | required | prevents rogue RADIUS attacks |
| CA trust | limited to site CA | reduces trust sprawl |
| Cipher policy | modern AES-GCM/ECDHE class | improves security posture |
This hardening work is useful only if emergency calling remains available. That brings the last question: fail-open policies and how to keep emergency calling alive without turning the port into an unmanaged hole.
Do fail-open policies preserve emergency calling?
A strict 802.1X policy can block a phone after a power event. In a hazardous area, that risk must be managed.
Yes, fail-open policies can preserve emergency calling, but they must be designed carefully. The safest approach is a controlled fail-open that places the phone into a restricted emergency VLAN, not a full-trust voice VLAN.
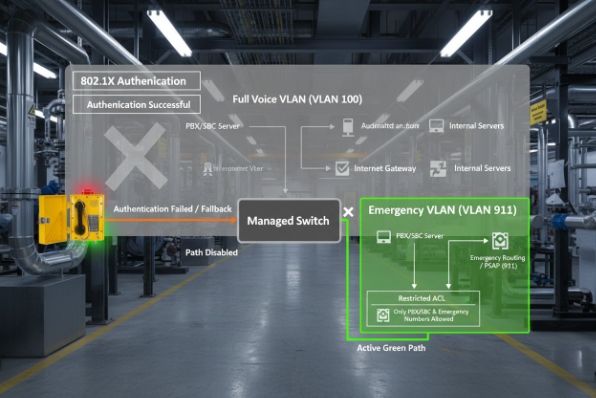
What “fail-open” should mean for emergency phones
Fail-open can mean several things in switch policy. A safe design separates “phone can call emergency numbers” from “phone can reach the entire enterprise.”
Two patterns work well:
1) Critical voice fallback VLAN
If 802.1X fails or the RADIUS server is unreachable, the switch places the port into a limited VLAN that can reach:
-
the local IP PBX or SBC
-
emergency call routing
-
NTP/provisioning only if required
This keeps emergency calling alive without opening access to sensitive networks.
2) MAB fallback with strict allowlist
If the phone cannot complete EAP due to a certificate issue, the port can fall back to MAC Authentication Bypass 9 (MAB) for known devices only. This is weaker than EAP-TLS, but it is better than full open access when managed well.
This pattern needs:
-
a controlled MAC inventory
-
alerts when MAB is used
-
a plan to return to 802.1X after recovery
Recovery behavior is as important as failure behavior
Emergency phones often sit idle. After a plant-wide power event, hundreds of endpoints can reboot at once. The port policy should handle that storm without leaving phones stuck in an unauthenticated state.
Key controls:
-
retry timers and backoff are reasonable
-
DHCP and voice VLAN assignment remain stable
-
the phone can re-auth after link flap without manual reboot
A fail-open design table that matches plant risk
| Policy choice | Availability | Security | Best use |
|---|---|---|---|
| Fail-closed | lowest | highest | low-risk endpoints, not emergency phones |
| Full fail-open | highest | lowest | not recommended in plants |
| Restricted emergency VLAN | high | medium–high | emergency calling endpoints |
| MAB fallback for allowlisted phones | medium–high | medium | transitional fleets and mixed devices |
This keeps both sides honest. Security remains real, and emergency calling remains available.
Conclusion
Choose EAP-TLS first, prove TLS 1.2+ in captures, automate certificate provisioning (SCEP 10), and use a restricted fail-open VLAN so emergency calling survives outages without opening the whole network.
Footnotes
-
[Standard for port-based network access control.] ↩
-
[Authentication protocol using Transport Layer Security.] ↩
-
[Protocol encapsulating EAP within a TLS tunnel.] ↩
-
[Signaling protocol used for initiating voice and video sessions.] ↩
-
[Framework for managing digital certificates and public-key encryption.] ↩
-
[Networking protocol for centralized authentication and accounting.] ↩
-
[Cryptographic protocol designed to provide communications security.] ↩
-
[Sets of algorithms used to secure network connections.] ↩
-
[Feature allowing non-802.1X devices to connect via MAC address.] ↩
-
[Protocol for automatic certificate management on network devices.] ↩











