Unsecured SIP is still common in harsh sites. One misconfigured switch or a tapped cabinet can expose call control and keys, even when the phone enclosure is certified Ex.
Yes, many explosion-proof SIP telephones can support TLS for SIP signaling, and SRTP for media. The key is to specify the exact security stack, certificate workflow, and cipher policy in your tender before installation.

A simple security checklist that survives real industrial deployments?
What “secure SIP” really includes
Secure signaling alone is not enough. SIP signaling protects registration, call setup, and sometimes SRTP key exchange. Media protection is a separate layer. A practical target for an Ex phone is:
- SIP over TLS (often called SIPS by many teams)
- SRTP for RTP/RTCP media
- A defined SRTP keying method (DTLS-SRTP or SDES), chosen to match your PBX/SBC
- Hardened management (HTTPS, strong credentials, disable legacy services)
- Network controls (VLAN/QoS, 802.1X, and switch port policies)
Why hazardous-area constraints still matter
TLS is software, but the installation is physical. If the phone uses two RJ45 entries, that means two glands, two shields, and two bonding decisions. Those choices affect ESD and surge behavior, which affects uptime. On offshore and mining sites, most “security outages” start as electrical noise and end as reboots.
What to put in your tender so vendors cannot dodge
| Topic | Minimum requirement | Proof to request |
|---|---|---|
| SIP signaling | TLS enabled and documented | Packet capture or lab report summary |
| Media | SRTP supported | Interop test with your PBX/SBC |
| Keying | DTLS-SRTP or SDES (state which) | Exact mode list + screenshots |
| Certificates | CSR + CA chain install | Sample certificate workflow |
| Cipher policy | Legacy suites can be disabled | Cipher list export |
| Device management | HTTPS provisioning | Provisioning guide + sample config |
Once this baseline is clear, the rest becomes an engineering choice instead of an argument in commissioning meetings.
Next, the security stack itself needs to be chosen with care, because “TLS + SRTP” has more than one valid keying path.
Which SIP security standards are available—TLS 1.2/1.3, SIPS, and SRTP with DTLS or SDES?
Security features often get sold as one checkbox. In real VoIP, they are a chain. If one link is weak, the system is still weak.
The common secure stack is SIP over TLS (TLS 1.2, and sometimes TLS 1.3) plus SRTP for media. SRTP keys are negotiated either using SDES in SDP or using DTLS-SRTP on the media path, and the correct choice depends on your PBX/SBC support.
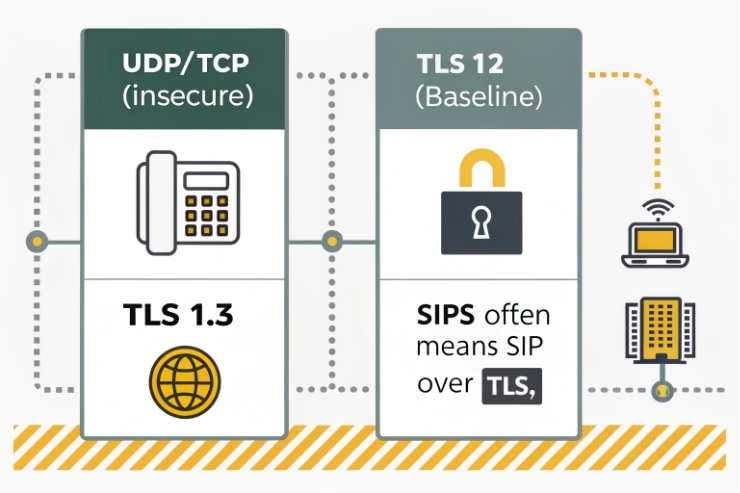
SIP over TLS and “SIPS”
SIP can run over TLS, and the SIPS URI scheme 1 exists to indicate secure contact. In practice, many industrial networks say “SIPS” when they mean “SIP over TLS.” The important part is the behavior you require: TLS must be enabled, and the phone must validate the server identity using certificates.
TLS 1.2 is still widely deployed. TLS 1.3 2 is newer and cleaner, but not every embedded SIP stack supports it yet. A safe tender line is “TLS 1.2 required, TLS 1.3 preferred,” plus “no TLS 1.0/1.1.”
SRTP for media
Secure Real-time Transport Protocol (SRTP) 3 protects RTP and RTCP traffic with confidentiality and integrity features. It should be required for any site that treats voice as a safety function, because audio can be captured from many places in a plant network.
SRTP keying: DTLS-SRTP vs SDES
This is where many projects get stuck:
- DTLS-SRTP: keys are established using DTLS on the media path. This avoids placing SRTP keys directly into SIP/SDP messages. It is clean when supported end-to-end, especially with a documented DTLS-SRTP keying profile 4.
- SDES (SDP Security Descriptions): SRTP keys are carried in SDP attributes. SDES can be acceptable only when SIP signaling is protected (TLS) and when key exposure risks are controlled, per SDES for SRTP 5.
A simple decision table for industrial teams
| Keying method | Best when | Main operational risk |
|---|---|---|
| DTLS-SRTP | SBC/PBX supports it and you want stronger key handling | More interop testing needed |
| SDES | Legacy PBX support and stable TLS is in place | Keys can leak if signaling is exposed |
| “SRTP only” (no clear keying) | Avoid | Usually becomes “not really secure” |
If a vendor says “supports TLS and SRTP,” always ask: “Which SRTP keying modes are actually implemented?”
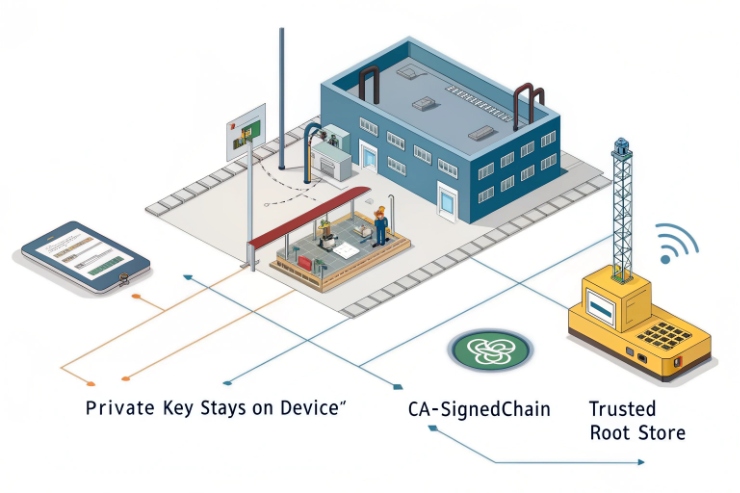
How are certificates handled—device CSR, CA-signed chains, OCSP/CRL checks, and auto-provisioning over HTTPS?
Certificate work is where secure VoIP deployments either scale nicely or collapse into manual device handling.
A robust Ex phone should support on-device CSR generation, import of CA-signed chains, and HTTPS-based provisioning. Revocation handling (CRL or OCSP) is a bonus feature that should be requested if your compliance policy demands it.
Certificate lifecycle that works for mass deployment
A workable process in industrial rollouts looks like this:
1) Device boots and joins a staging VLAN.
2) It generates a CSR (or receives a preloaded identity).
3) Your CA issues a device certificate.
4) The phone installs the certificate and CA chain.
5) Provisioning applies SIP/TLS settings and locks down management access.
This is far better than exporting private keys by hand. It also fits tender audits.
Server validation and chain handling
Minimum requirements that should be written clearly:
- Phone can store the trusted CA chain (root + intermediate).
- Phone validates the SIP server certificate chain.
- Phone checks server name matching (domain/SAN) to prevent “any certificate works.”
Revocation checks: keep expectations realistic
CRL/OCSP checking is more common on servers than on small embedded devices, but it is still worth asking for if your environment requires strict revocation controls. If the phone does not support revocation checks, the compensating control is short certificate lifetimes plus fast rotation. If your policy requires it, reference the Online Certificate Status Protocol (OCSP) 6 behavior you expect.
HTTPS provisioning and certificate pinning
Provisioning over HTTPS should be the baseline. For higher security, request:
- mutual TLS for provisioning, or
- certificate pinning to a private CA,
- signed configuration files,
- and a defined rollback method.
Documentation table to request from suppliers
| Document | What it should include | Why it matters |
|---|---|---|
| TLS/SRTP admin guide | Exact settings and supported modes | Prevents “checkbox security” |
| Certificate workflow | CSR steps + chain install | Enables real PKI rollout |
| Provisioning guide | HTTPS, file format, parameters | Supports mass deployment |
| Revocation note | CRL/OCSP support and limits | Helps compliance review |
| Test evidence | Capture or report summary | Stops guesswork |
If certificate handling is clean, cipher policy becomes the next gate for compliance teams, especially in regulated projects.
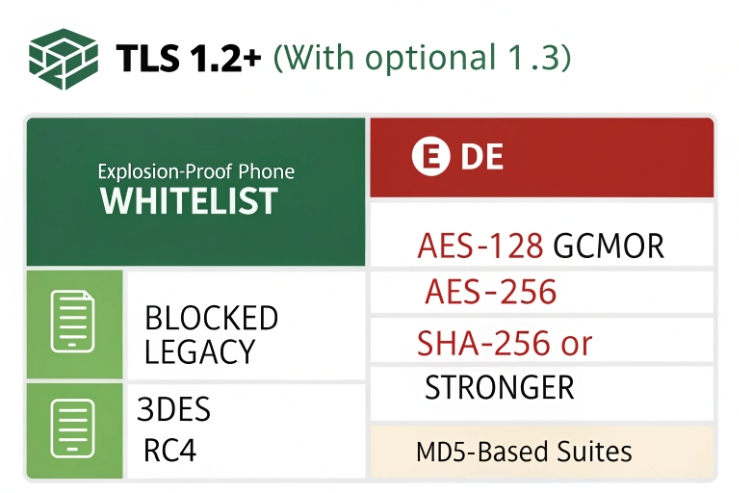
Do cipher policies meet compliance—FIPS 140-3 modules, ECDHE key exchange, AES-GCM, SHA-256, and legacy suite blocking?
A phone can “support TLS” and still fail a compliance review if it cannot control ciphers or if its crypto module is not validated where required.
For high-compliance sites, require TLS 1.2+ with modern suites (ECDHE + AES-GCM + SHA-256 family), the ability to disable legacy suites, and a clear statement on whether the device uses a FIPS 140-3 validated cryptographic module.
What to ask for in plain procurement language
- TLS 1.2 required; TLS 1.3 preferred.
- No SSLv3 / TLS 1.0 / TLS 1.1.
- Only forward-secret key exchange (ECDHE preferred).
- AEAD ciphers (AES-GCM preferred).
- SHA-256 or stronger hashing for signatures and integrity.
- Ability to export or display the enabled cipher list.
- Ability to block weak suites and weak signature algorithms.
FIPS 140-3: what it is and what it is not
FIPS 140-3 is about validated cryptographic modules. It does not magically make a product secure. It proves the crypto module was tested under the CMVP rules. If your customer demands FIPS, the tender should request:
- the module vendor and certificate reference
- the Security Policy document
- the exact TLS versions and cipher suites supported in the validated mode
If you need an authoritative baseline, point compliance reviewers to NIST’s FIPS 140-3 program information 7.
If FIPS is not required, do not force it. It can increase cost and limit firmware choices. Instead, focus on strong TLS policy plus stable patching.
A practical compliance table
| Compliance need | What to specify | What to verify |
|---|---|---|
| “Modern security” | TLS 1.2+, ECDHE, AES-GCM, legacy blocked | Cipher list + config screenshots |
| “Regulated / federal” | FIPS 140-3 validated module required | Security Policy + evidence of mode |
| “Legacy PBX” | TLS 1.2 with limited suites may be needed | Interop test plan |
| “Long life plant” | Patch policy and signed firmware | Vendor update commitment |
Cipher policy is not only a checkbox. It controls whether the security team can approve the endpoint without exceptions.
Now the last piece is the access layer. Many plants want 802.1X, voice VLAN automation, and secure remote management while still keeping SIP/RTP encrypted end-to-end.
Can network access be hardened with 802.1X, LLDP-MED, DHCP options, and secure TR-069/SSH while keeping SIP/RTP encrypted?
Hardening is not one feature. It is how the phone joins the network, how it gets settings, and how it is managed later without opening weak doors.
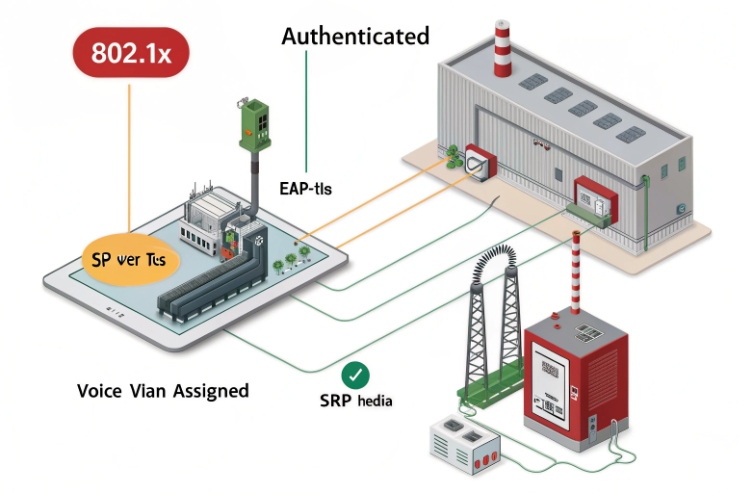
Yes, VLAN/QoS automation and access control can coexist with SIP/TLS and SRTP. The safest design uses 802.1X for port access, LLDP-MED or DHCP options for voice VLAN, HTTPS provisioning, and SSH only when needed, while SIP runs over TLS and media runs as SRTP.
802.1X: keep unauthorized devices off the voice network
802.1X is port-based network access control. It can require device authentication before the switch opens the port. In harsh sites, this stops “plug-and-go” rogue devices in cabinets. Practical tender items:
- EAP method support (match your RADIUS policy)
- certificate-based auth option
- fallback behavior (critical voice points often need a controlled fallback plan)
Voice VLAN automation: LLDP-MED or DHCP options
LLDP-MED is widely used to auto-place endpoints into a voice VLAN and apply edge policies. Where LLDP-MED is not available, some deployments use DHCP options to deliver VLAN ID and priority (options vary by ecosystem). If you require this, write it explicitly, and demand a working example.
Secure management without breaking voice encryption
- Keep web UI on HTTPS only.
- Disable Telnet and weak services.
- Use SSH with strong keys only when needed.
- If TR-069 is used, require HTTPS transport and a clear authentication method.
Keep QoS consistent with encryption
Encryption does not stop QoS. DSCP and VLAN PCP marking still work, since the IP header fields remain visible to the network. A clean model is:
- RTP (SRTP) gets the highest voice priority class
- SIP/TLS gets a control priority class
- video intercom gets a separate class with shaping
- multicast paging gets controlled via IGMP snooping and a defined priority
A design table that ties everything together
| Function | Best practice | What to lock down |
|---|---|---|
| Network admission | 802.1X | EAP method + cert handling |
| Voice VLAN | LLDP-MED preferred | VLAN ID + priority behavior |
| Provisioning | HTTPS | CA trust + file signing (if needed) |
| SIP signaling | TLS 1.2+ | Server validation + cipher policy |
| Media | SRTP | DTLS-SRTP or SDES (state which) |
| Paging/video | IGMP + QoS classes | Multicast control + bandwidth limits |
This approach keeps the phone secure, keeps voice stable, and keeps operations simple for large deployments.
Conclusion
Explosion-proof telephones can support secure SIP, but only when TLS/SRTP modes, certificates, and access hardening are specified as testable requirements in the tender.
Footnotes
-
SIP standard reference for SIPS URIs and secure signaling behavior. (↩︎) ↩
-
Defines TLS 1.3 protocol details to validate “TLS 1.3 preferred” claims. (↩︎) ↩
-
SRTP specification for encrypted media protection requirements and terminology. (↩︎) ↩
-
DTLS-SRTP profile used to negotiate SRTP keys without exposing them in SDP. (↩︎) ↩
-
SDES method for transporting SRTP keys in SDP, useful for legacy PBX compatibility checks. (↩︎) ↩
-
OCSP definition for certificate revocation checking expectations in secure SIP deployments. (↩︎) ↩
-
NIST reference for FIPS 140-3 and validated crypto module requirements in regulated environments. (↩︎) ↩











