In the age of cyber warfare 1, an industrial telephone is no longer just a voice device; it is a network endpoint. A compromised phone on an oil rig can become a listening device for corporate espionage or a backdoor for hackers to attack the plant’s operational technology 2 (OT) network. Physical safety is useless if your digital security is wide open.
Yes, modern explosion-proof VoIP telephones support TLS (Transport Layer Security) for encrypting signaling (SIP) and SRTP (Secure Real-Time Transport Protocol) for encrypting the voice media. This ensures that call metadata and audio streams are unreadable if intercepted by malicious actors on the network.

The Digital Shield for OT Networks
At DJSlink, we treat our telephones like IT assets. We understand that in critical infrastructure 3—power plants, refineries, defense sites—unencrypted traffic is a vulnerability you cannot afford.
-
SIP (Signaling): Contains who is calling whom, and auth credentials. If unencrypted, hackers can steal passwords and make fraudulent calls.
-
RTP (Media): The actual voice. If unencrypted, anyone with Wireshark 4 can replay your confidential conversations.
Which ciphers, TLS versions, and SRTP profiles are implemented?
You wouldn’t use a lock that can be picked with a hairpin. Similarly, old encryption protocols (like SSL v3) are vulnerabilities, not protections.
Leading industrial phones implement TLS 1.2 (and increasingly TLS 1.3) using strong cipher suites like ECDHE-RSA-AES256-GCM-SHA384. For voice media, SRTP uses AES-128 or AES-256 encryption profiles (typically AES_CM_128_HMAC_SHA1_80) to ensure low-latency but unbreakable audio privacy.
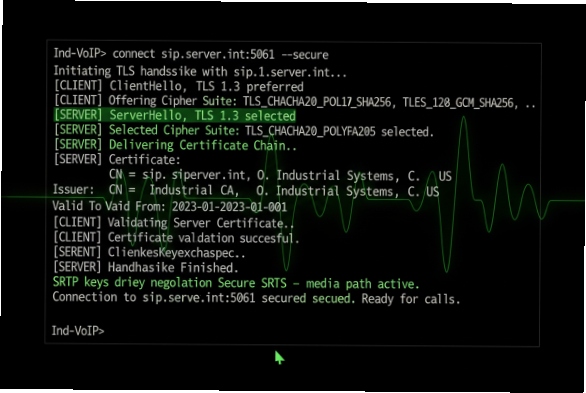
The Standard We Enforce
-
Deprecated Protocols: We disable SSLv3, TLS 1.0, and TLS 1.1 by default. They are obsolete and unsafe.
-
Forward Secrecy: We prioritize cipher suites that support Perfect Forward Secrecy 5 (PFS), meaning even if a private key is compromised later, past sessions remain secure.
-
SRTP Key Exchange: We typically use SDES (via TLS-protected SIP) or DTLS-SRTP (mandatory for WebRTC 6 integration) to securely swap the keys needed to decode the voice stream.
Are certificates, 802.1X, and VLANs supported in OT networks?
You don’t let strangers walk into your control room. 802.1X ensures you don’t let unknown devices plug into your network switch.
Yes, robust DJSlink phones support IEEE 802.1X (EAP-MD5, EAP-TLS) for port-based network access control, ensuring only authorized devices can connect. They also support LLDP-MED for automatic VLAN discovery, segregating voice traffic into a prioritized, isolated Voice VLAN separate from the control system data.
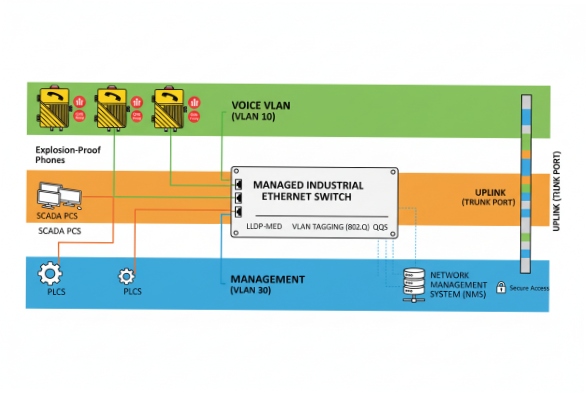
The "Zero Trust" Approach
-
Trusted CA Certificates: You can upload your company’s Root CA certificate to the phone. This allows the phone to validate that it is talking to your real SIP server, not a hacker’s "Man-in-the-Middle 7" fake server.
-
Mutual Auth (mTLS): For high-security sites, we support client certificate uploads. The server validates the phone, and the phone validates the server.
-
VLAN Tagging: We keep voice packets (VLAN 10) away from SCADA 8 packets (VLAN 20). This reduces congestion and prevents a compromised phone from easily attacking a PLC 9.
Do secure boot and signed firmware protect endpoints?
A physical attacker might try to load a malicious operating system onto the phone to create a permanent spy device.
Enterprise-grade explosion-proof phones utilize "Secure Boot" mechanisms. The hardware checks the digital signature of the firmware before loading it. If the firmware has been tampered with or is not signed by the manufacturer (DJSlink), the device refuses to boot, preventing the installation of rootkits or malware.
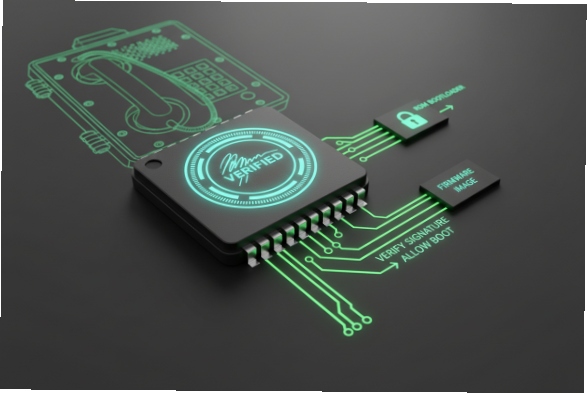
Firmware Integrity
-
The Threat: "Supply Chain Attacks 10" or local tampering. Someone downloads a modified firmware version that looks normal but copies all audio to a remote IP.
-
The Defense: Our firmware images are cryptographically signed. The bootloader burned into the chip validates this signature. You cannot "flash" a DJSlink phone with non-DJSlink code.
How are keys provisioned and rotated at scale?
Manually typing 64-character passwords into 500 phones is impossible. Automation is key to security hygiene.
Security credentials and configuration files are provisioned securely via TR-069 or HTTPS using encrypted XML/CFG files (often AES-256 encrypted). This allows for "Zero Touch Provisioning" where the phone fetches its specific configuration, including unique SIP passwords and certificates, immediately upon boot without manual intervention.

Managing the Fleet
-
No Plaintext: We never store passwords in plaintext in the config file.
-
Rotation: If an employee leaves or a password is suspected compromised, the central PBX/Device Management System pushes a new config file. The phone reboots and updates its credentials automatically.
Conclusion
Industrial security is no longer just about preventing sparks; it’s about preventing data breaches. An explosion-proof phone must be a hardened network appliance. By demanding TLS 1.2+, 802.1X, and Signed Firmware, you ensure that your voice communication system protects your conversations just as reliably as it protects your facility from explosions.
Footnotes
-
Use of digital attacks to disrupt vital computer systems or espionage. ↩
-
Hardware and software that detects or causes changes in industrial processes. ↩
-
Assets and systems essential for the functioning of a society and economy. ↩
-
A popular network protocol analyzer used for troubleshooting and traffic analysis. ↩
-
Feature ensuring that compromised long-term keys do not compromise past session keys. ↩
-
Open source project enabling real-time audio and video communication in web browsers. ↩
-
Cyberattack where attackers secretly intercept and relay communications between two parties. ↩
-
Control system architecture using computers and data communications for process management. ↩
-
Ruggedized industrial computer adapted for the control of manufacturing processes. ↩
-
Cyberattacks targeting less-secure elements in an organization’s supply network. ↩











