In critical infrastructure 1 like air traffic control, emergency dispatch, and offshore drilling, "he said, she said" is not an acceptable post-incident analysis. Every command to open a valve or shut down a pump must be recorded. Interfacing your explosion-proof telephony with a robust recording system is essential for liability protection, accident investigation, and operational quality assurance 2.
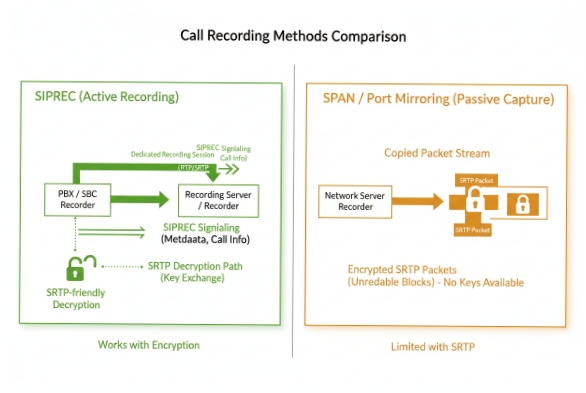
Explosion-proof VoIP telephones are typically interfaced with recording systems using the SIPREC standard (active recording) or network Port Mirroring (passive recording). SIPREC is the modern preferred method as it offloads the stream directly from the phone or PBX to the recorder. Advanced systems support dual-stream recording for stereo separation and Lawful Intercept compliance, with AES-256 encrypted storage to meet GDPR and industry regulations.

The "Black Box" of Industry
At DJSlink, we advise clients that a phone system without recording is an incomplete safety system. When a Mayday call comes in from a Zone 1 3 platform, the operator’s reaction time and instructions need to be captured.
Unlike old analog taps where you physically wired onto the copper line, modern VoIP 4 recording is data-centric. It happens either at the Endpoint (the phone sends the audio), the Network (the switch copies the packets), or the PBX (the server forks the call).
Do SIPREC, port mirroring, or API methods support capture?
Choosing the right capture method depends on your network architecture and encryption requirements.
SIPREC (RFC 7866) is the industry standard for active recording, allowing the Session Border Controller (SBC) or the phone itself to initiate a separate recording session to the logging server. Port Mirroring (SPAN) is a legacy passive method that copies raw network traffic but struggles with modern encrypted calls (SRTP) because the recorder lacks the decryption keys.
Method Comparison
| Method | Mechanism | Pros | Cons |
|---|---|---|---|
| SIPREC | Active. The SIP server/phone invites the Recorder to the call. | Works with SRTP (Encryption). Metadata rich. Scalable. | Requires SIPREC license on PBX/Phone. |
| Port Mirroring (SPAN) | Passive. Network switch copies packets to a recorder port. | No impact on call flow. "Invisible" to users. | Fails if voice is encrypted (SRTP 5). Complex to manage across subnets. |
| Active API | Server-side. The Recording Server bridges into the call. | Great for "On-Demand" recording triggered by user. | Adds latency. Consumes conference resources. |
DJSlink Recommendation: For modern secure sites using SRTP, SIPREC is the only viable long-term solution. It ensures that even if you encrypt your voice for privacy, the authorized recorder gets a clear, decrypted stream.
Are dual-stream and lawful intercept features available?
In an investigation, you need to know exactly who spoke when. If the recording is a mixed mono track, shouting matches become unintelligible.
Yes, high-end industrial recording supports "Dual-Stream" capabilities, capturing the caller and callee on separate audio channels (Stereo) for precise voice analytics. Lawful Intercept (LI) features are standard in carrier-grade systems (ETSI/CALEA), allowing authorities to silently monitor target extensions without detecting artifacts like clicks or volume drops.

Why Stereo Matters for Safety
-
The Scenario: A pump room operator is screaming over machinery noise while the control room tries to give instructions.
-
Mono Recording: The two voices mix with the background noise. It’s a wall of sound. Transcription 6 is impossible.
-
Dual-Stream (Stereo): You can isolate the Control Room track. You hear their instructions clearly. You can isolate the Pump Room track to analyze the background machinery noise (e.g., "was the turbine spinning down?").
How is storage encrypted and retention controlled?
Storing voice data is a liability. If a hacker steals unencrypted recordings of your security protocols, you are compromised.
Recordings are encrypted at rest using AES-256 standards, managed by Key Management Servers (KMS). Retention policies are granularly controlled by the recording software, allowing automated deletion after set periods (e.g., 30 days for routine calls, 7 years for incident-tagged calls) to comply with legal frameworks like GDPR or SOX.

The Chain of Custody
-
Encryption: As soon as the file lands on the disk, it is scrambled. Only authorized users with the decryption key and audit rights can play it.
-
Watermarking: To prevent tampering, files are digitally signed 7. If someone tries to edit the audio to change the evidence, the signature breaks.
-
Lifecycle Management:
-
Routine Ops: Delete after 90 days.
-
Emergency: If a user tags a call as "Incident," the system locks it ("Legal Hold 8") so it is never auto-deleted until the investigation closes.
-
Do recordings integrate with dispatch and QA workflows?
A recording is useless if you can’t find it. Searching for "that call from last Tuesday" is inefficient.
Modern recorders integrate deeply with Dispatch Consoles and QA software. They tag recordings with rich metadata (Caller ID, Geo-Location, Radio ID, Emergency State). This allows Quality Assurance teams to replay incidents on a map, reconstruct the timeline of calls, and score operator performance for training purposes.

The "Instant Replay" Function
In DJSlink dispatch centers, we enable "Instant Recall":
-
The Feature: A dedicated button on the operator’s console.
-
The Use Case: An operator hears a garbled message from a Zone 2 field technician. Instead of asking them to repeat (wasting time), they hit "Instant Replay" to hear the last 30 seconds again, boosted and noise-cancelled 9.
-
The Metadata: The recording isn’t just audio; it’s tagged with "Zone 2 – Pump Station 4". Searching by location becomes possible.
Conclusion
Interfacing explosion-proof telephones with recording systems is the bridge between operations and accountability. By moving away from passive sniffing to active SIPREC streaming, enabling Dual-Stream capture for clarity, and securing data with AES-256, you turn every phone call into a verifiable data point that enhances safety culture and simplifies incident reconstruction.
Footnotes
-
Systems and assets typically physical or virtual so vital that their incapacity or destruction would have a debilitating impact on security. ↩
-
A systematic process of determining whether a product or service meets specified requirements. ↩
-
A hazardous area classification where an explosive atmosphere is likely to occur in normal operation. ↩
-
Technology that delivers voice communications and multimedia sessions over Internet Protocol (IP) networks. ↩
-
A profile of RTP intended to provide encryption, message authentication and integrity, and replay attack protection for voice data. ↩
-
The process of converting spoken language into written text, essential for reviewing accident details in noisy recordings. ↩
-
A mathematical scheme for verifying the authenticity of digital messages or documents. ↩
-
A legal process used to preserve all forms of relevant information when litigation is reasonably anticipated. ↩
-
A method for reducing unwanted ambient sound using active noise control engineering. ↩











