Calls cross borders full of firewalls, NAT, and odd SIP. An SBC sits at that border. It keeps signaling clean, media stable, and bad traffic out.
An SBC is a Session Border Controller. It is a B2BUA at your SIP edge. It secures, normalizes, and routes calls while anchoring media so remote phones and trunks work under real network conditions.

Next I will explain why an SBC helps with SIP trunks and remote phones. Then I will show how it secures SIP with TLS, SRTP, ACLs, and topology hiding. After that I will cover NAT fixes, media anchoring, and codec mismatch. Finally, I will compare on-prem, cloud, and carrier-edge deployments so you can choose the right place.
Why do I need an SBC for SIP trunks and remote phones?
Trunks and roaming clients raise risk and interop pain. Carriers speak many dialects. Home routers break NAT. An SBC smooths all of this.
You use an SBC to protect the edge, normalize SIP and SDP, anchor media, and enforce policy. It keeps trunks stable and gives remote phones a reliable path through NAT and firewalls.
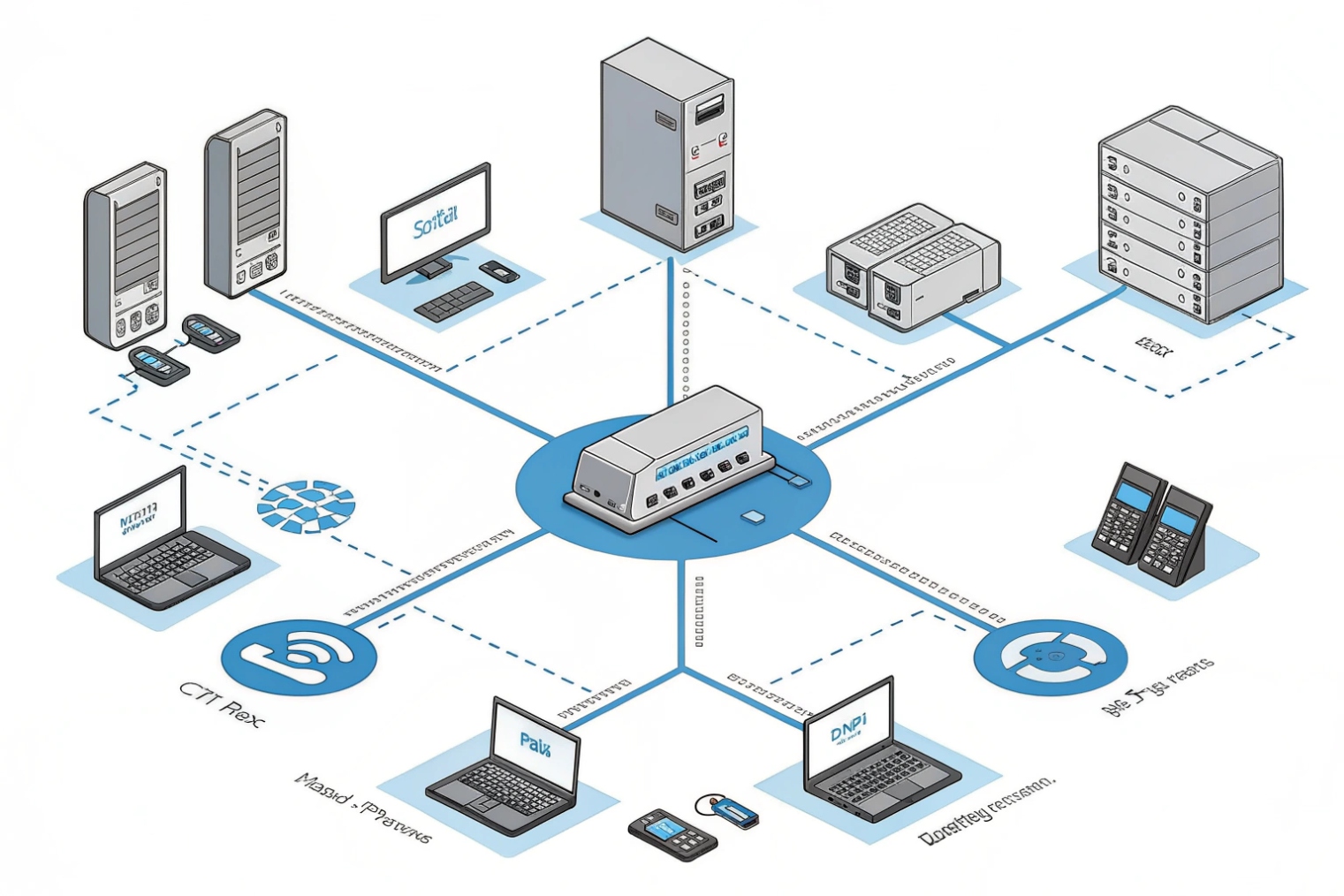
A Session Initiation Protocol (SIP) 1 trunk is not just a pipe. It is another network with its own timers, header expectations, early media rules, and codec lists. Without a control point, your PBX must adapt to every carrier change. That wastes time and causes outages. An SBC terminates signaling as a Back-to-Back User Agent (B2BUA) 2. It accepts the carrier’s INVITE, checks the headers, rewrites what your PBX expects, and starts a new INVITE inside. This stops oddities like unusual Diversion, the P-Asserted-Identity header 3, or different PRACK requirements from leaking inward. It also means you can swap carriers with fewer PBX changes.
Remote phones are a different problem. Home NATs, double NAT, and hotel firewalls break symmetrical RTP and hide private addresses in SDP. An SBC sits on a stable public IP. It maintains session pinholes, keeps registrations alive with keepalives, and relays media when direct paths fail. For softphones and browsers, the same SBC can speak SIP over WebSocket and even do WebRTC interworking. One place, one policy.
Security is the other half. The internet scans SIP all day. Password brute force, toll fraud, and malformed packets are common. An SBC rate-limits bad traffic, challenges unknown sources, and drops floods before they hit your PBX. It can also enforce dial policy and call admission controls so a burst of calls does not saturate your WAN. When a link or carrier fails, the SBC can route around it using rules tied to SIP codes or media quality. The result is simple: fewer surprises, faster cutovers, and cleaner incident handling.
| Need | Pain without SBC | What the SBC adds |
|---|---|---|
| Trunk interop | Header/timer mismatches | SIP/SDP normalization |
| Remote users | NAT, one-way audio | Registrations, media relay |
| Security | Scans, fraud, DoS | TLS/SRTP, rate limits, ACLs |
| Quality | Jitter, drops | QoS marking, CAC |
| Resilience | Manual failover | Policy routing on codes/metrics |
How does an SBC secure SIP—TLS, SRTP, ACLs, and topology hiding?
You cannot bolt security on at the end. The SBC makes it part of session setup from the first packet to the last RTP frame.
The SBC terminates TLS for SIP, negotiates SRTP keys, filters sources with ACLs, and hides internal IPs by rewriting headers and SDP. It also rate-limits and validates messages.
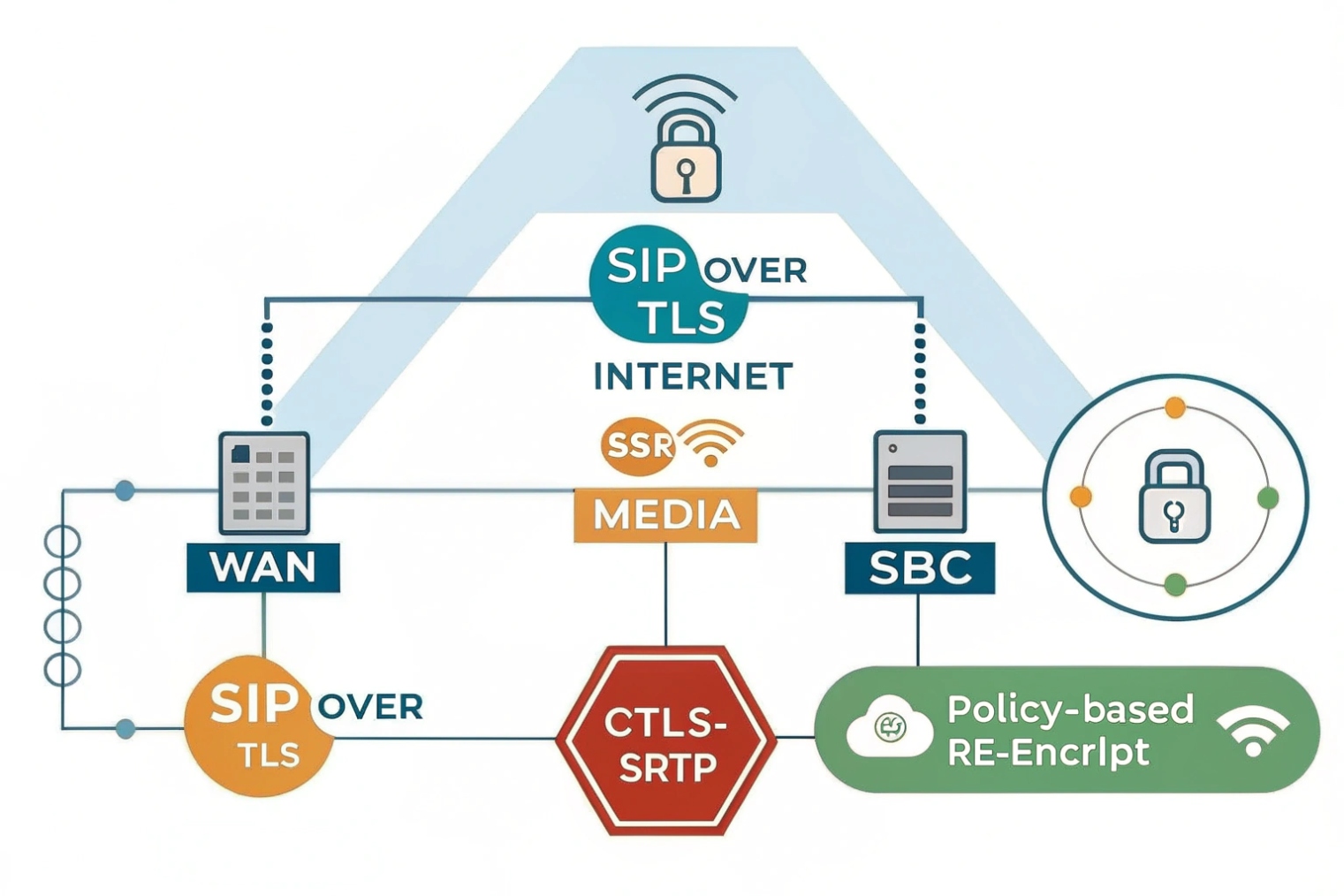
Start with signaling. SIP over TLS prevents simple snooping and MITM on register and invite flows. The SBC presents a certificate, checks client certs if you use mutual TLS, and enforces cipher and version policies. Inside your network, the SBC can speak TLS, TCP, or UDP to the PBX based on what your equipment supports. This lets you harden the WAN side without breaking the LAN side.
Media uses Secure Real-time Transport Protocol (SRTP) 4 for privacy and integrity. The SBC negotiates SRTP keys using SDES or DTLS-SRTP, then re-encrypts or decrypts at the border as policy requires. For example, you may keep SRTP between browser and SBC, then use RTP to a legacy PBX, or SRTP end-to-end if trunks support it. Either way, keys never leave their zone, and the SBC blocks unknown SSRCs or ports.
Access control lists stop random hosts from talking to your SIP ports. You allow only carrier IP ranges and your remote worker subnets or VPN pools. Unknown sources get dropped before any authentication. Add request-rate limits per source for REGISTER and INVITE. Tie these to alarms so you see brute-force attempts early. For country or region limits, a simple geo ACL on the SBC reduces noise further.
Topology hiding protects your private addressing and internal hostnames. The SBC rewrites Via, Record-Route, Contact, and the SDP c= and m= lines so outside parties only see the SBC’s public IPs and domains. It also strips vendor-specific headers that reveal brand and version. If a call forks, the SBC can aggregate branches so the outside party never sees your internal dial plan.
Finally, validation keeps bad messages from crashing your stack. The SBC enforces message size limits, header counts, method whitelist, and strict parsing. It drops malformed messages, rejects odd sequences, and normalizes timer behavior like Session-Expires and 100rel/PRACK (reliable provisional responses) 5. Security is not only about blocking; it is also about being predictable when the other side is not.
| Control | What it protects | Example policy |
|---|---|---|
| SIP over TLS | Signaling privacy/integrity | TLS 1.2+, modern ciphers |
| SRTP (DTLS/SDES) | Media privacy | SRTP mandatory, fallback per trunk |
| ACLs / Geo ACLs | Edge exposure | Allowlist carrier IPs and VPN pools |
| Topology hiding | Internal IPs/domains | Rewrite Via/Contact/SDP c=/m= |
| Rate limiting | DoS and brute force | INVITE/REGISTER caps per source |
| Validation | Parser robustness | Header count/size/method whitelist |
Can an SBC fix NAT, media anchoring, and codec mismatch in calls?
Yes. This is where the SBC earns its keep. It makes paths real, even when networks fight you, and it speaks enough “dialects” to bridge endpoints.
The SBC anchors RTP to stable public IPs, relays when NAT breaks direct flow, and transcodes or renegotiates codecs and DTMF. It also controls early media, PRACK, and 180/183 rules.
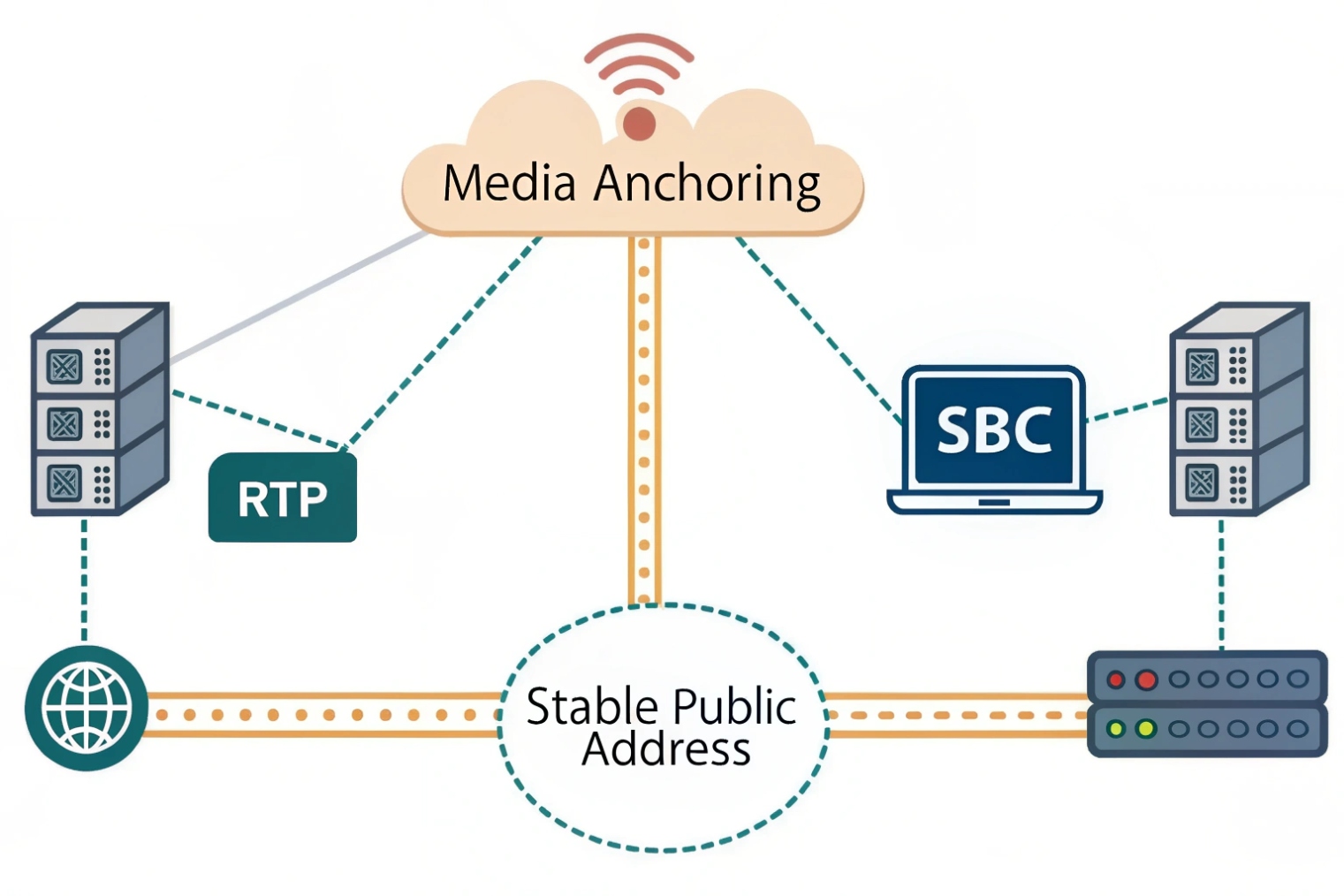
NAT first. Phones and PBXs often put private IPs in SDP. Many home routers change ports without warning. The SBC solves this by anchoring media. It advertises its own public IP and port range to both sides, receives RTP from each, and forwards to the other. The result is a single stable stream per leg. With symmetric RTP and keepalives, the pinholes stay open even when the path moves. For roaming clients or WebRTC, the SBC also handles ICE candidates and can fall back to a relay when direct routes fail.
Codec mismatch is common too. Browsers send Opus; trunks may demand G.711; legacy devices might insist on G.729. The SBC can transcode between these sets when no common codec exists, or it can negotiate a shared subset to avoid CPU load. For DTMF, it can switch between inband, RTP events for DTMF (RFC 4733) 6, and SIP INFO so IVRs work regardless of endpoint quirks. For fax, it can offer T.38 or pass-through based on detect rules.
Early media and ringback cause confusion across networks. One side may expect 180 without SDP (local ringback). The other sends 183 with SDP (network ringback). The SBC can normalize this: generate early media to the caller while presenting 180 to the callee, or vice versa. It can enforce PRACK/100rel when a trunk requires reliable provisional responses and hide that complexity from your PBX. This avoids the classic “silence before answer” where NAT or policy blocked early RTP.
Quality needs policy too. The SBC can remark DSCP Expedited Forwarding (EF, 46) 7 for RTP and CS3/AF31 for SIP at the border so your routers prioritize correctly. It can do Call Admission Control to cap concurrent calls below link capacity. If media quality drops—high jitter or loss—the SBC can re-INVITE to a different media relay, force a new route, or fail the leg cleanly so your logic can overflow to another carrier.
| Problem | Symptom | SBC action |
|---|---|---|
| NAT breaks media | One-way/no audio | Anchor RTP, symmetric RTP, keepalives |
| Codec mismatch | 488/415 errors | Transcode or renegotiate |
| Wrong ringback | Silence pre-answer | Normalize 180/183, manage early media |
| DTMF fails | IVR not hearing tones | Convert inband/RTP events/SIP INFO |
| Poor quality | Choppy audio | QoS remarking, CAC, reroute on metrics |
Should I deploy the SBC on-prem, cloud, or at the carrier edge?
Placement changes latency, control, and cost. Pick the spot that best fits your traffic and risk. There is no single right answer.
On-prem gives control and low jitter to local PBXs. Cloud gives reach for remote users and quick scale. Carrier-edge offloads complexity and shortens PSTN paths. Many teams mix two or all three.
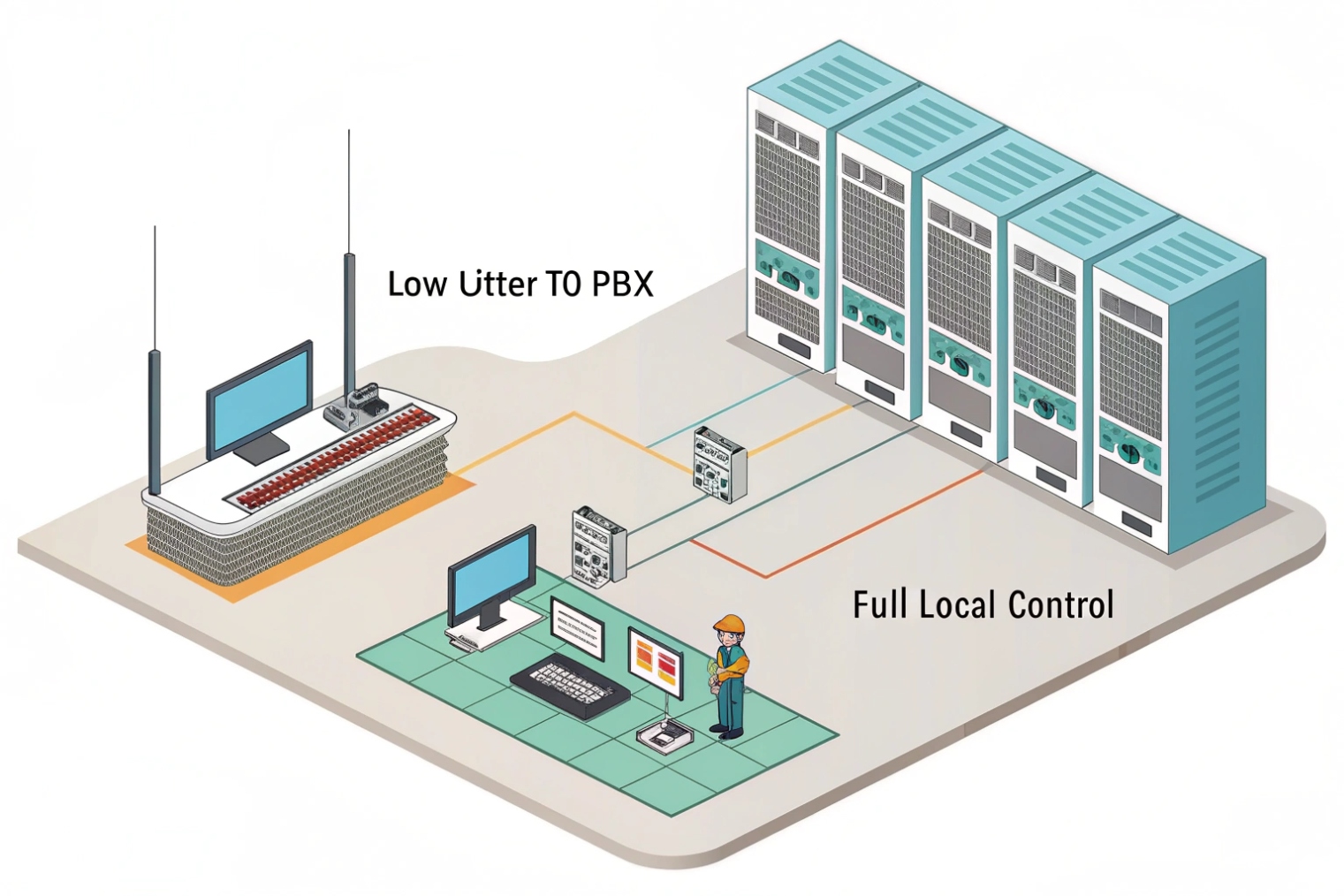
On-prem SBCs sit close to your PBX and LAN phones. They keep media local for site-to-site calls and lower jitter to your switches. You have full control of routing, certificates, and logs. You can integrate with internal identity and monitoring. You also own the high availability story: redundant appliances, shared VIPs, and link diversity. This is strong for campuses, factories, and places with strict data rules. The downside is scale during spikes from the internet or remote users. You also manage hardware lifecycles.
Cloud SBCs live near users and SaaS platforms. They scale up and down, deploy fast, and sit on fat peering with many carriers. They are ideal when agents work from anywhere or when browsers use WebRTC. Latency to the PBX can be higher if your PBX stays on-prem, so many teams move the call control or media servers closer to the cloud SBC. Costs shift to OPEX, and you rely on the provider’s HA. Make sure you get per-tenant keys, clear logs, and API control.
Carrier-edge SBCs (SBC-as-a-service at the trunk provider) remove most interop and DDoS headaches. The carrier handles TLS, SRTP, surge protection, and routing on their backbone. Your PBX peers to their edge over VPN or public internet with strict ACLs. Media often stays inside the carrier network longer, which lowers PSTN hairpinning. You lose some knobs: fine-grained header rewrites or custom failover logic may be limited. Many teams use a small enterprise SBC in front of the PBX and a carrier SBC—enterprise for policy and topology hiding, carrier for reach and scale.
Think traffic patterns. If most calls are internal or site-to-site, keep media local with on-prem. If most calls involve remote browsers or mobile agents, bias to cloud. If you want the simplest trunking story, push work to the carrier edge. A hybrid gives you control without giving up reach.
| Option | Strengths | Trade-offs | When to choose |
|---|---|---|---|
| On-prem | Low jitter to PBX, full control | Hardware/HA burden | Campuses, strict compliance |
| Cloud | Fast scale, global reach, WebRTC | Extra hops to on-prem PBX | Remote agents, web apps |
| Carrier edge | Simple trunking, DDoS shield | Fewer custom knobs | Lean IT, fast rollout |
| Hybrid | Best of each where needed | More design effort | Multi-region enterprises |
Conclusion
Place an SBC at your SIP edge to secure, normalize, and anchor calls. Use TLS/SRTP, ACLs, and topology hiding. Fix NAT and codecs at the border. Choose on-prem, cloud, or carrier edge based on where your users and trunks live.
Footnotes
-
Defines SIP signaling fundamentals used by trunks, registrations, and SBC interoperability. ↩︎ ↩
-
Explains B2BUA behavior and why SBCs terminate and re-originate SIP dialogs at the border. ↩︎ ↩
-
Details the P-Asserted-Identity header for trusted caller identity between networks and carriers. ↩︎ ↩
-
SRTP standard for encrypting and authenticating RTP media, used by SBCs for secure voice. ↩︎ ↩
-
Clarifies reliable provisional responses (100rel/PRACK) that affect early media and ringback interoperability. ↩︎ ↩
-
Spec for RTP events carrying DTMF tones so IVRs work across different endpoints and trunks. ↩︎ ↩
-
Defines Expedited Forwarding PHB for prioritizing voice packets when SBCs remark DSCP at the network edge. ↩︎ ↩











