Sharing real phone numbers with strangers or temporary contacts is risky. One bad interaction can turn into spam, harassment, or compliance headaches for the whole team.
Call masking replaces real phone numbers with temporary proxy numbers, so callers can talk or text through your system without exposing private contact details on either side.

In a SIP or VoIP environment, call masking sits between your IP PBX / UC platform and the carrier. The platform presents temporary virtual numbers 1 to both sides, handles routing for voice and SMS, and keeps a clean audit trail. Done well, you get privacy, control, and analytics, without breaking your CRM or compliance story.
How does number masking protect my privacy?
Customers want fast contact, but they do not want their personal number to live forever in someone else’s phone. Staff feel the same about their own mobiles.
Number masking protects privacy by routing calls and SMS through temporary virtual numbers, so neither side sees the other’s real phone number while your system still controls the session.
How number masking works in practice
At a technical level, masking is simple: the platform uses one proxy number as a meeting point. Both real numbers connect to that proxy.
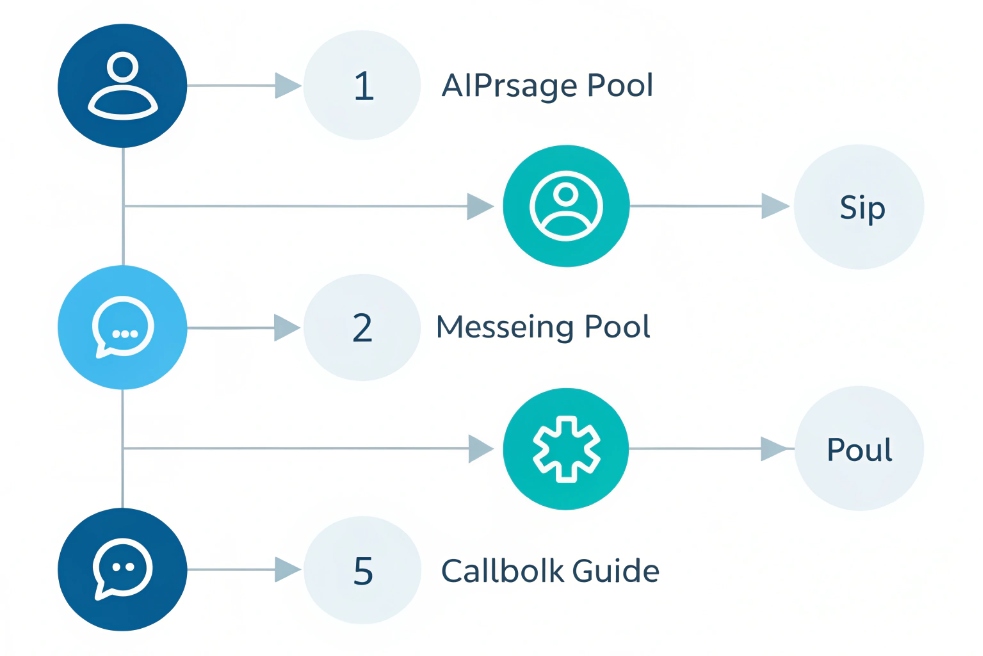
Typical flow for a masked voice call:
- Your app or CRM requests a masked session between Party A and Party B.
- The platform picks or creates a virtual DID (local or toll-free).
- When A calls B, your PBX or CPaaS re-writes the caller ID to the proxy.
- The platform looks up the current binding and sends the call to B’s real number.
- When B calls back the same proxy, the platform routes back to A.
Both sides only see the proxy on their phone screens. They cannot call the other party directly once the mask expires.
Here is a simple comparison:
| Scenario | What each side sees | Who knows the real numbers |
|---|---|---|
| No masking | A sees B’s real number, B sees A’s | Carrier and both end users |
| Caller-ID blocking (*67) | One side sees “Private/Unknown” | Carrier, but not the callee |
| Call masking with proxy | Both see the proxy business number | Your platform and carrier only |
This is why ride-share apps, delivery platforms, medical services, and marketplaces like masking. Drivers, couriers, or staff can coordinate with customers in real time, but nobody walks away with a personal number stored in their contacts.
Masking also helps inside larger organizations. For example:
- Support agents call from masked outbound CLIs tied to queues, not personal DIDs.
- Doctors call patients from clinic numbers while using their own mobiles.
- Contractors call customers without exposing personal SIM cards.
Behind the scenes, your SIP trunks and IP PBX still see the real numbers, stored in secure mapping tables. You can log, record, and report on sessions. But external phones only see the clean, branded, controllable proxy numbers you chose.
Can I mask both calls and SMS on SIP?
Voice is only half the story. Many workflows need follow-up codes, directions, or links by text, but people still do not want to expose their real numbers.
Yes. You can mask both calls and SMS by using virtual numbers that support voice and messaging, then routing SIP calls and API-based SMS through the same proxy identity.
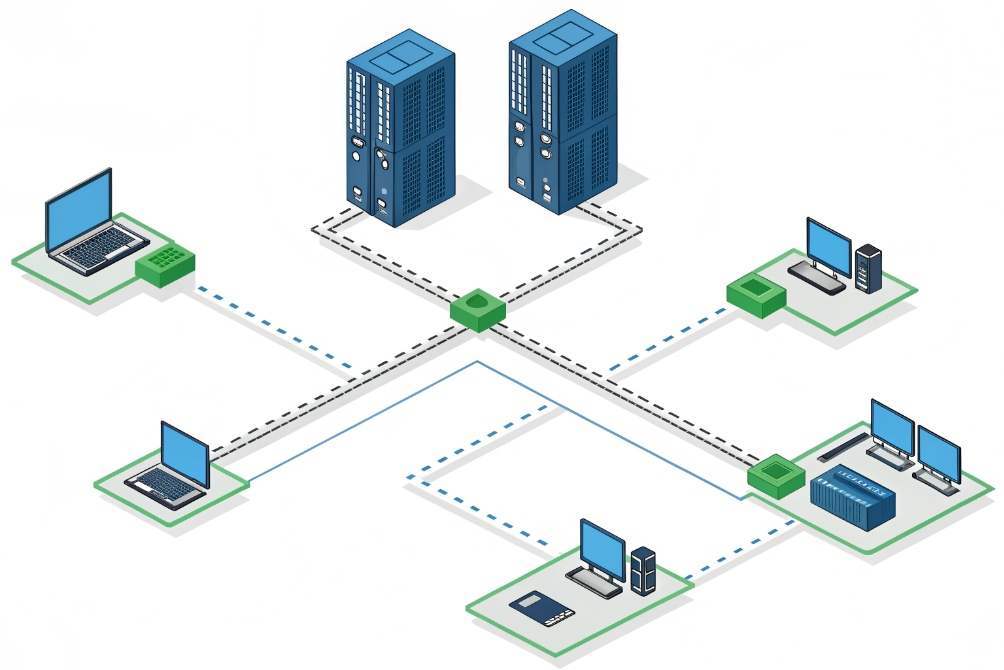
Voice and SMS masking architecture
SIP handles voice signaling and media. SMS usually rides on separate messaging APIs or SMPP links, even if you buy both from the same provider. Call masking ties these together at the number level, not the protocol level.
A common pattern:
- You lease virtual DIDs from a CPaaS/UCaaS provider.
- Those DIDs are enabled for SIP voice and SMS.
- Your IP PBX uses SIP trunks for calls.
- Your apps or middleware use messaging APIs for SMS on the same numbers.
When you create a masked pair (A ↔ B):
- Voice calls route via SIP using the proxy as caller and called number.
- SMS messages to the proxy route via the messaging API and re-map to the other side.
So the real “glue” is not SIP itself. It is the session binding between real identities and proxy numbers inside your business logic.
A simple view:
| Channel | Transport layer | How masking works |
|---|---|---|
| Voice | SIP + RTP/SRTP | Caller ID re-written to proxy DID |
| SMS | HTTP API or SMPP | To/From numbers re-written to proxy DID |
| Apps | REST / Webhooks | Business logic creates, updates, ends bindings |
For DJSlink-style SIP deployments, this means your IP phones, SIP intercoms, and softphones still talk SIP. A middleware layer (or cloud CPaaS) handles SMS and number maps. The user experience stays simple: one “business number” acts as the mask for both calls and texts.
You must also watch a few limits:
- Some carriers do not support SMS for every DID country or type.
- MMS or rich messaging may need different routes.
- Long masked sessions should expire, so old proxies cannot be abused.
If you design the mapping as short-lived and task-based (one mask per order, ride, ticket, or case), you get clean privacy, simple audits, and a predictable user story.
How do I audit masked sessions for compliance?
Privacy is good, but compliance teams still need to see what happened. They need logs, not just nice promises about anonymity.
You audit masked sessions by logging both proxy and real-party identifiers in secure systems, using mapping tables, role-based access, and clear retention policies that balance traceability with privacy.
Building a compliant audit trail
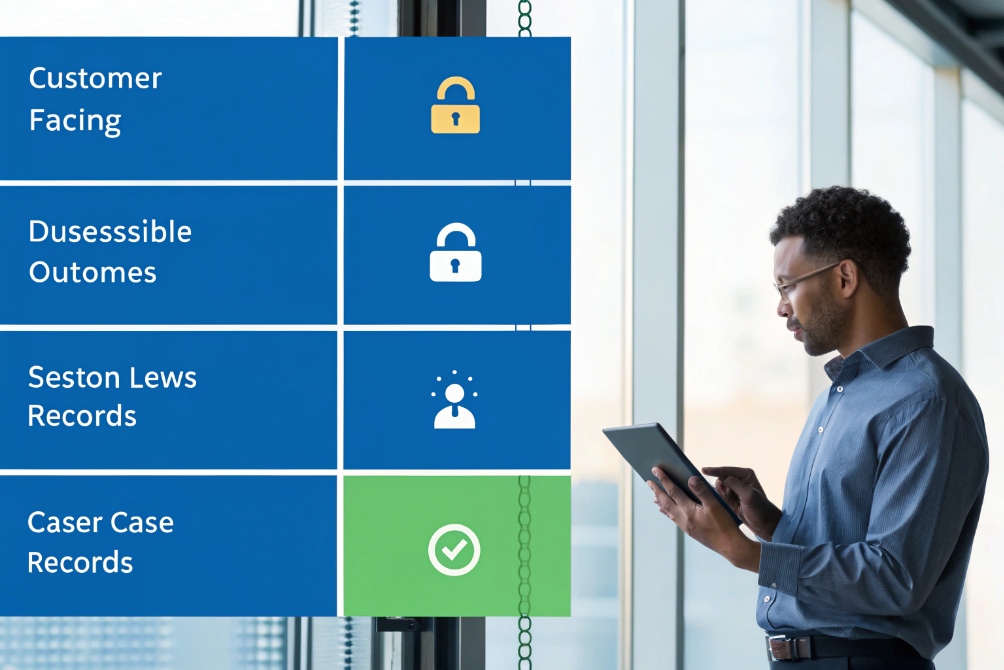
The trick is to keep two views of the same session:
- A customer-facing view that only shows proxy numbers and basic details.
- An internal secured view that includes real phone numbers and business context.
You usually need three layers of data:
- Call detail records (CDRs) / message logs
- Time, duration, direction, proxy number, trunk, status.
- Masking map table
- Proxy number + session ID → real A and real B numbers, order/ride/ticket IDs.
- CRM or operational system
- Customer identity, agent identity, case or order status and notes.
A simple structure:
| Dataset | Contains | Who should see it |
|---|---|---|
| CDR / SMS logs | Proxy numbers, times, basic metrics | Ops, WFM, team leaders |
| Mapping table | Proxy ↔ real numbers + session IDs | Security, compliance, limited admins |
| CRM / ticketing | Customer IDs, case details, outcomes | Agents, supervisors, analysts |
For compliance with GDPR/CCPA-style rules, you also:
- Use pseudonymization: real numbers stored separately from general logs.
- Encrypt mapping tables at rest and in transit.
- Restrict who can run queries that reveal real numbers.
- Define retention times for mappings, not just for CDRs.
When a regulator or legal team needs to reconstruct an interaction, they can follow the chain:
Proxy number + timestamp → mapping table → real parties → CRM case → recording and transcript (if enabled).
For everyone else, reports and dashboards only show:
- Proxy numbers or internal IDs.
- Aggregated statistics.
- Redacted transcripts where needed.
This way, you honour privacy promises while still having enough data to defend against fraud, harassment complaints, or billing disputes.
You also need clear rules for:
- E911 / emergency calls: which numbers are allowed to be masked or not.
- Lawful intercept: where and how recording and export happen.
- PII redaction in speech analytics and message archives.
If you build the audit model at the start of the project, masked numbers become a controlled tool instead of a blind spot.
Does masking affect caller ID analytics?
Masked calls show different numbers on the network. That obviously touches caller ID, spam scores, and all your dashboards that rely on CLIs.
Call masking shifts analytics from real numbers to proxy numbers. You keep volume and outcome metrics, but per-caller history and some caller ID reputation signals now attach to your masked pool instead of the original phones.

What changes in analytics when you mask
When you use masked CLIs:
- Carriers and analytics tools see only the proxy DID as the origin or destination.
- CNAM name lookups show whatever is registered for the proxy, not the real caller.
- STIR/SHAKEN signatures and spam filtering attach to the proxy number’s reputation.
Inside your own system, you still know who is who. But on the public network, all calls from a certain line of business or marketplace route through shared masked numbers.
Impact on metrics:
| Metric type | Impact of masking |
|---|---|
| Call volume and duration | No real change, still accurate |
| Answer rates | Depend on proxy number reputation and CNAM |
| Per-caller history | Must be rebuilt from CRM / mapping, not raw CLI |
| Spam / labeling risks | Move to proxy numbers; need good hygiene there |
The good news: you can brand your CNAM for those proxies. For example, “ACME RIDESHARE SUPPORT” instead of a random mobile. This can improve answer rates versus unknown mobile CLIs.
The trade-off: if you change proxy pools often, external analytics tools cannot build stable histories. Your own analytics must lean on internal IDs, mapping tables, and CRM data, not just on external CLIs.
Designing analytics around proxies, not raw numbers
To keep insight, design your reporting model as:
- Session-centric (order, ride, ticket, case), not caller-number-centric.
- User-centric (customer ID, agent ID), not SIM-centric.
Your internal dashboards can show:
- Customer journey across calls, SMS, and chats.
- Agent performance and queue metrics.
- Marketplaces or partner accounts that generate more calls.
They do not need raw external numbers on every screen.
At the same time, you should:
- Monitor proxy number reputation with carriers and spam APIs.
- Track answer and completion rates per proxy pool.
- Rotate or retire numbers that become too “warm” or mis-labeled.
For SIP carriers that support STIR/SHAKEN call authentication 6, work with them to:
- Properly sign your masked outbound traffic.
- Use consistent attestation levels.
- Keep your proxy ranges clean of abusive traffic.
Done right, masking becomes an analytics shift, not a loss. You move focus from “this SIM called that SIM” to “this customer and agent interacted through our controlled identity space”, which is much closer to how modern contact centers think.
Conclusion
Call masking uses proxy numbers to protect real identities while your SIP and analytics stack still sees full context, so you gain privacy without giving up control, logging, or insight.
Footnotes
-
Twilio Proxy docs explain proxy numbers, session bindings, and routing for voice/SMS masking. ↩ ↩
-
Visual walkthrough of SIP-style routing via a proxy number between two parties. ↩ ↩
-
Architecture view of using one virtual DID as the shared identity for voice and SMS. ↩ ↩
-
Example access-control view for limiting who can reveal real numbers behind proxies. ↩ ↩
-
Dashboard visual for how proxy-number pools affect performance and caller ID metrics. ↩ ↩
-
FCC overview of STIR/SHAKEN and caller ID authentication to reduce spoofing and improve trust. ↩ ↩











