A VoIP outage is bad. Losing call recordings, CDRs, and configs is worse. Nightly backups often miss the moment right before a mistake or an attack.
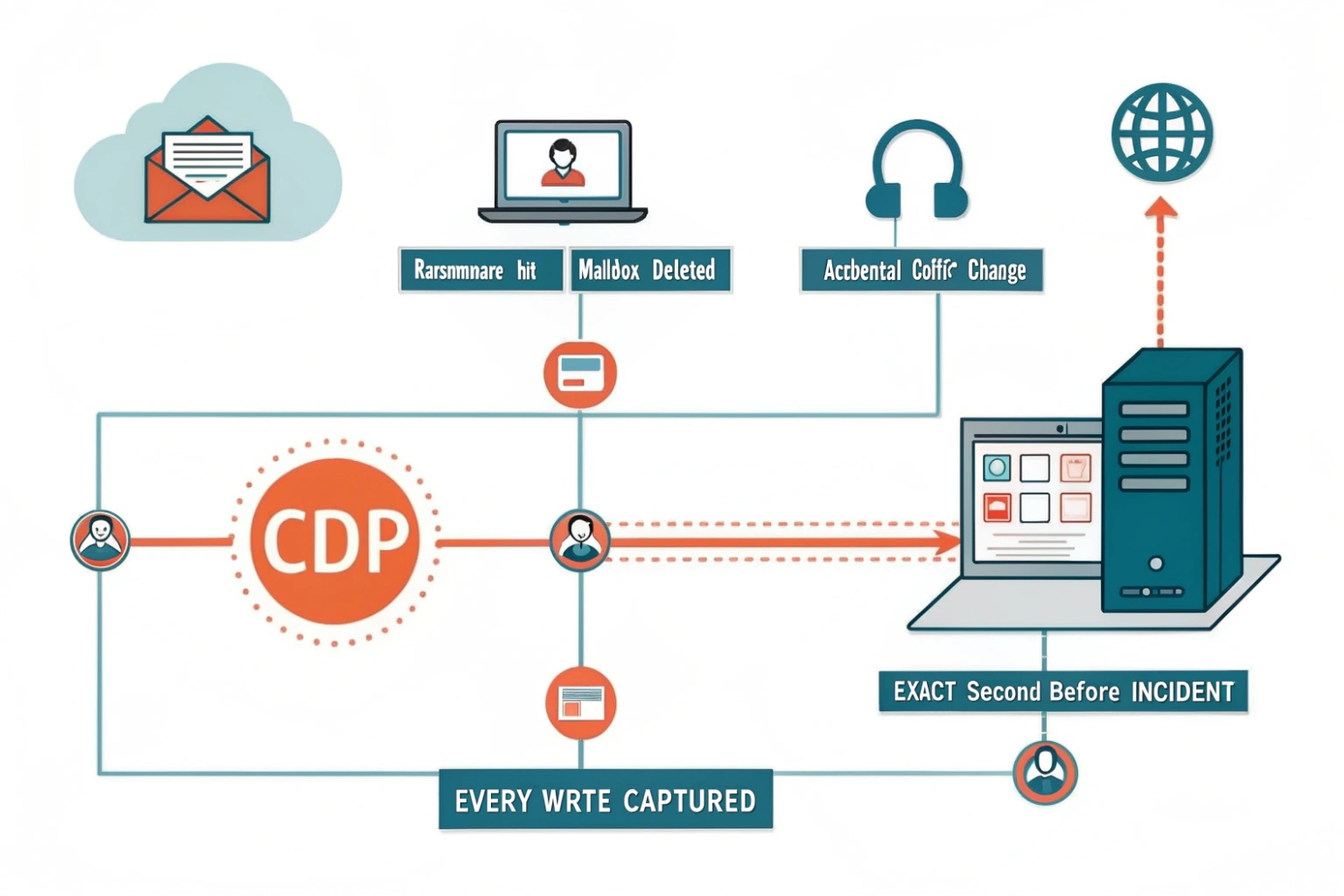
Continuous data protection (CDP) captures data changes as they happen, so VoIP assets like recordings, voicemail, and configs can be restored to a precise point in time with near-zero data loss.
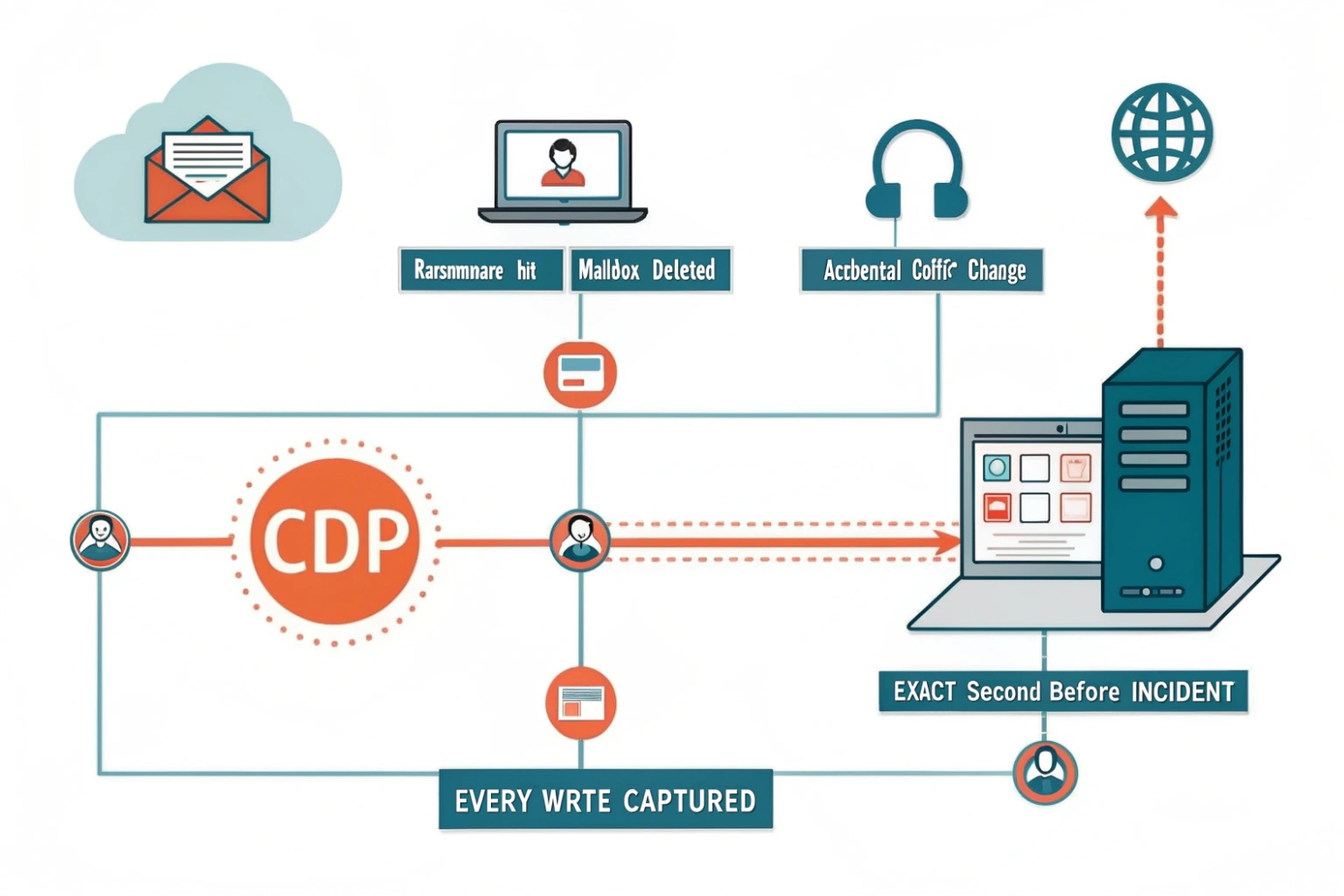
Continuous data protection (CDP) 1{#ref-1} is not the same as high availability (HA). HA keeps calls running. CDP lets you roll data back after deletion, corruption, bad updates, or ransomware. When both are planned together, recovery becomes predictable instead of hopeful.
How does CDP differ from snapshots and nightly backups for me?
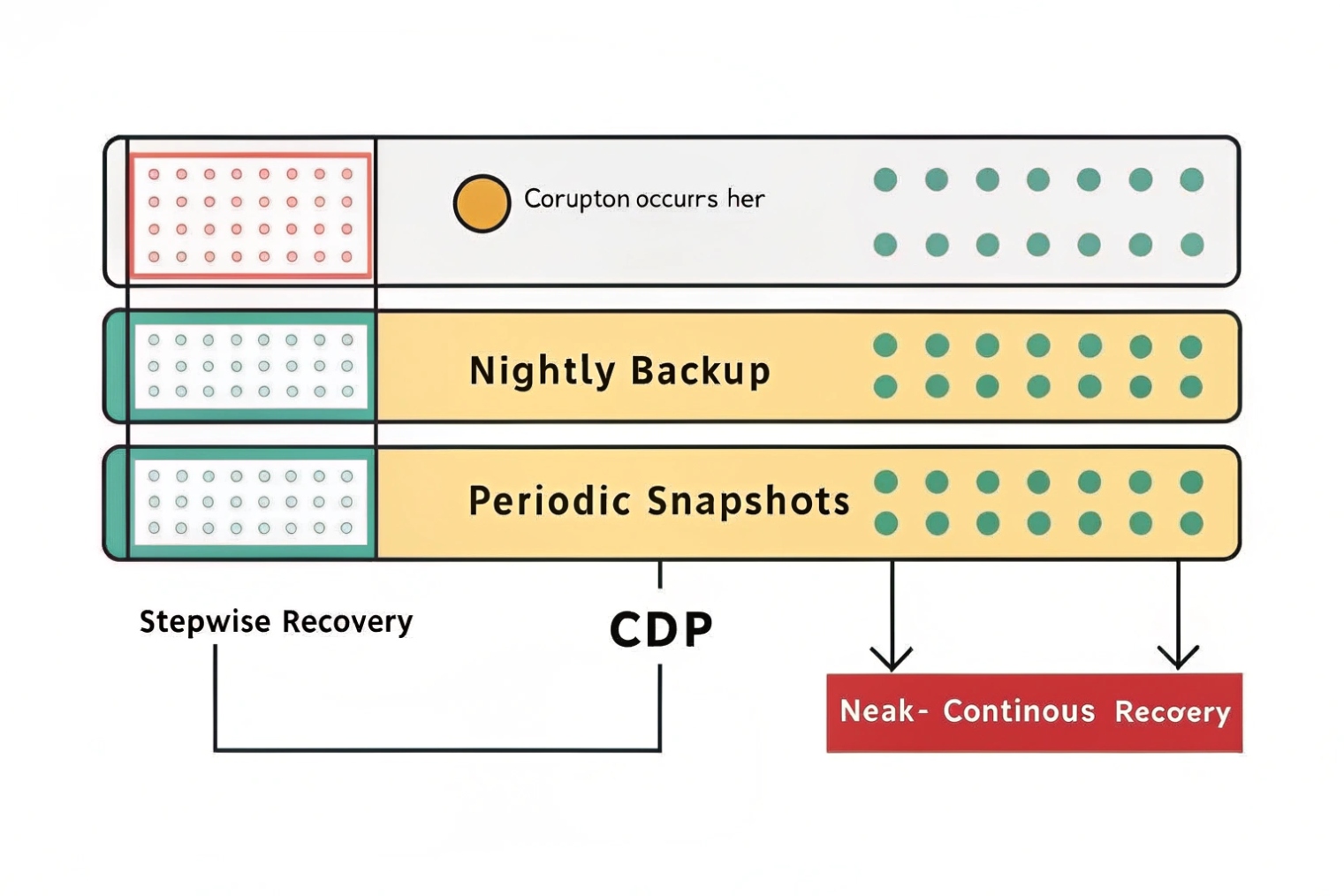
Backups that run once a day are fine until a recording is deleted at 2:05 PM or a database corrupts at 4:12 PM. Then “restore last night” is not good enough.
CDP logs changes continuously, snapshots capture point-in-time images at intervals, and nightly backups copy data on a schedule. CDP gives the smallest RPO and the most granular rollback when VoIP data changes all day.
What “continuous” really means
CDP typically works by journaling every write (or near every write) so you can restore to a specific time like 2:04:37 PM. Some products market “near-CDP” by taking very frequent snapshots (e.g., every 5–15 minutes). That can be useful, but it is not the same as true journaling.
CDP vs snapshots vs backups in simple terms
| Method | How often it captures changes | Typical RPO | Typical restore choice | Best use |
|---|---|---|---|---|
| Nightly backup | Daily | 12–24 hours | “Last night” | Low-change systems, archive |
| Snapshot | Hourly / every few minutes | Minutes to hours | “Snapshot at 2 PM” | Fast rollback, simple storage |
| CDP (journal) | Continuous | Seconds to minutes | “2:04:37 PM” | Ransomware, corruption, human error |
One more difference that matters: consistency
Restoring a VoIP stack is not one file. It’s usually multiple moving parts:
- PBX config + PBX database
- Recording files + recording metadata/index
- Voicemail files + voicemail database/metadata
CDP platforms that support consistency groups (or application-consistent checkpoints) help ensure those pieces restore to the same moment, preventing “orphaned recordings” and mismatched data.
Can CDP protect call recordings, CDRs, configs, and voicemail in real time?
Most teams start CDP for call recordings, then discover the harder part is metadata and databases. The audio file is easy to copy. The “who called who” record must match it.
Yes. CDP can protect recordings, CDRs, configs, and voicemail in near real time, but it must include the databases and indexes that tie those files together, or restores will be incomplete.
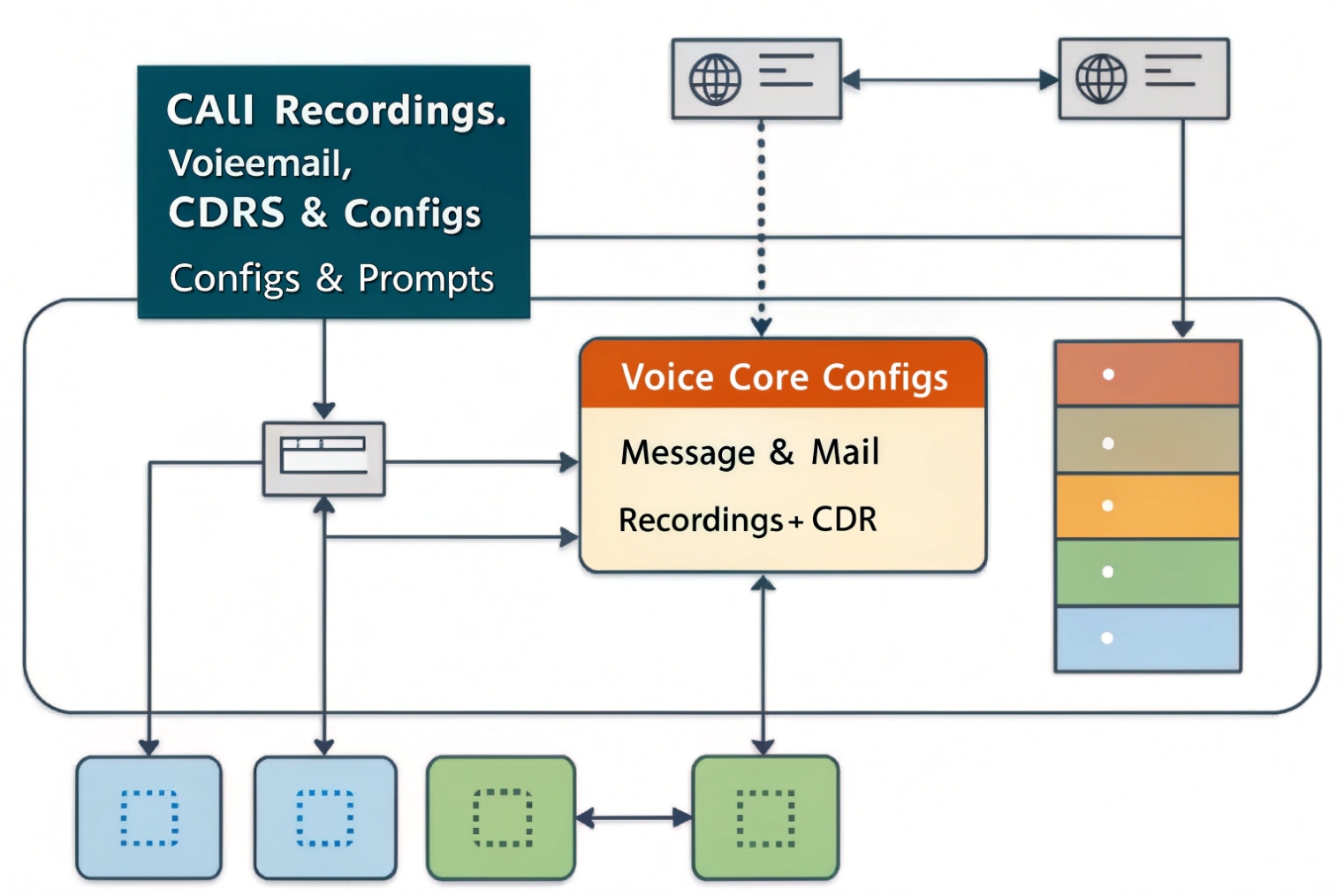
What to protect in a VoIP system (practical map)
Call recordings
- High volume, sustained writes.
- CDP works well, but you must plan bandwidth, caching, and storage throughput.
CDRs and analytics
- Usually database-based.
- CDP can capture block-level changes, but database consistency matters (crash-consistent restores can require replay/repair). If available, use DB-aware hooks or periodic app-consistent points.
PBX configs and provisioning templates
- Small but high impact.
- Put them in CDP and treat them like code when possible (export + version history/change log).
Voicemail
- Typically files + metadata.
- Protect both, or restores look “half right” (files exist but UI doesn’t show them, or the reverse).
Consistency group approach (easy to operate)
- Group A: PBX database + PBX config store
- Group B: Recording store + recording metadata DB/index
- Group C: Voicemail store + voicemail metadata DB
| VoIP asset | CDP value | Main risk | Design fix |
|---|---|---|---|
| Recordings | Prevents loss and speeds restore | Sustained write load | Throttle + cache + capacity planning |
| CDR DB | Precise rollback after corruption | App consistency | DB-aware points or consistency groups |
| PBX configs | Fast recovery from bad changes | Old configs restored | Add config exports + change logs |
| Voicemail | Restores user trust fast | Orphaned messages | Protect files + metadata together |
Pair CDP with immutability for ransomware
CDP alone is not enough if an attacker can delete your recovery points. For real ransomware posture, add immutable storage (WORM/object lock), and separate backup credentials from day-to-day PBX admin access.
What RPO/RTO, storage, and retention policies should I set for compliance?
Many teams set one global retention rule and call it done. That often fails compliance and wastes storage. Voice data is not all equal.
Set RPO and RTO per data type: near-zero RPO for configs and databases, practical RPO for recordings based on link cost, and retention based on regulation, legal risk, and business needs, with immutable copies for regulated recordings.
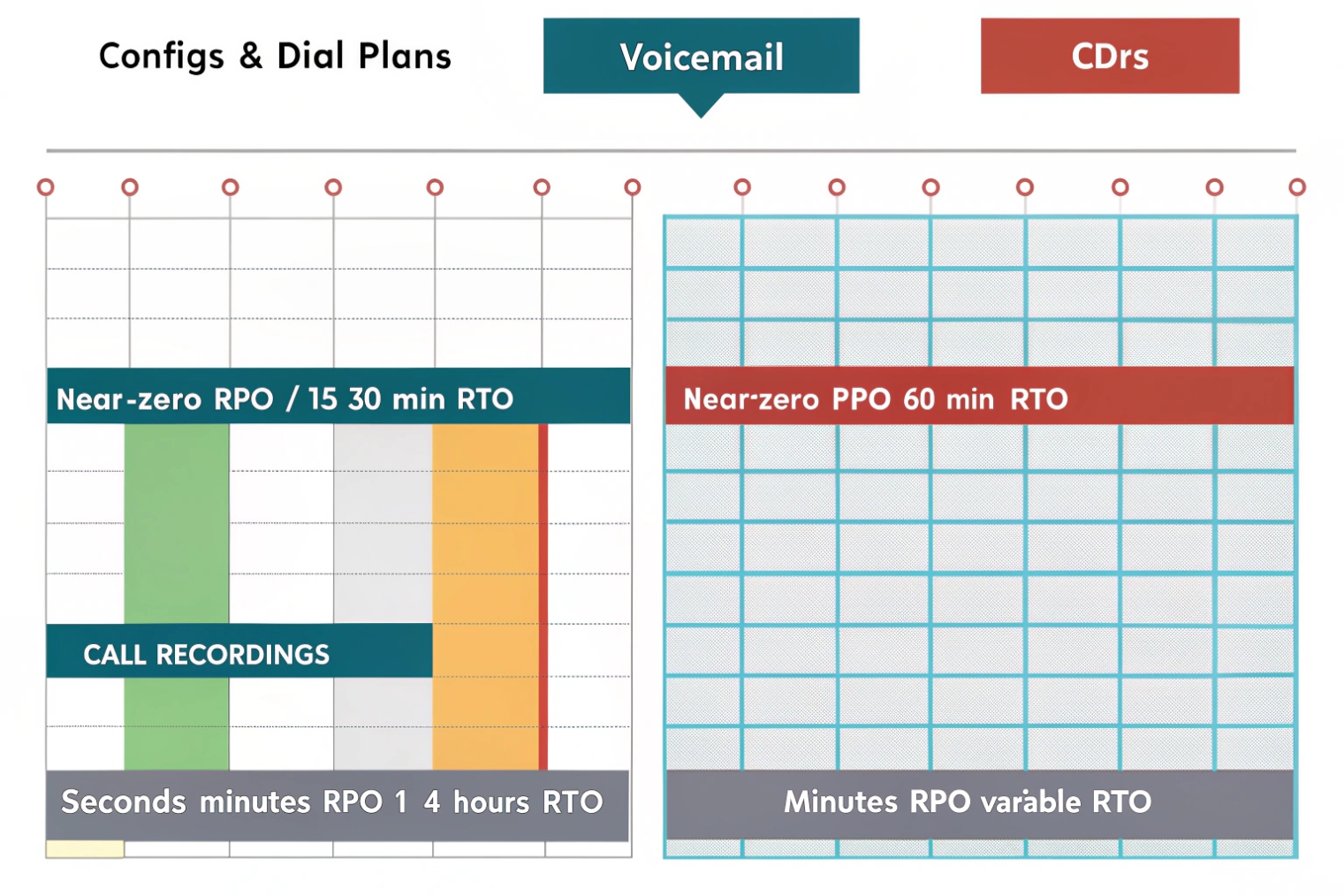
Baseline RPO/RTO starting point (adjust to your risk)
| Data type | Suggested RPO | Suggested RTO | Why |
|---|---|---|---|
| PBX configs/templates | 0–5 minutes | 15–60 minutes | Bad changes are common and painful |
| CDR database | 5–15 minutes | 1–4 hours | Reporting, billing, investigations |
| Call recordings | 5–60 minutes | 4–24 hours | Big data; restore time depends on size |
| Voicemail | 5–15 minutes | 1–4 hours | Users notice fast |
Retention: split “rollback” from “archive”
A common structure that stays cost-effective:
- CDP journal window: 3–30 days (point-in-time rollback)
- Compliance/archive retention: months/years (object storage + immutability)
Storage sizing: the hidden driver is write rate
Sizing depends on:
- Daily recording volume + codec/bitrate
- Database write rate (CDR, metadata, queue stats)
- Journal window length
- Compression/dedupe support
Best practice: measure real change rate for at least a week, then size for peak day plus headroom.
How do I deploy CDP across on-prem PBX, cloud, and S3 with encryption?
VoIP stacks are rarely “one server.” A clean CDP deployment covers on-prem PBX nodes, cloud services, and object storage without opening new security holes.
Deploy CDP by protecting on-prem PBX and databases with agent or storage-based replication, exporting cloud PBX data via provider tools/APIs, and storing long-term copies in S3 with encryption, access controls, and immutability, while isolating backup credentials from PBX admins.
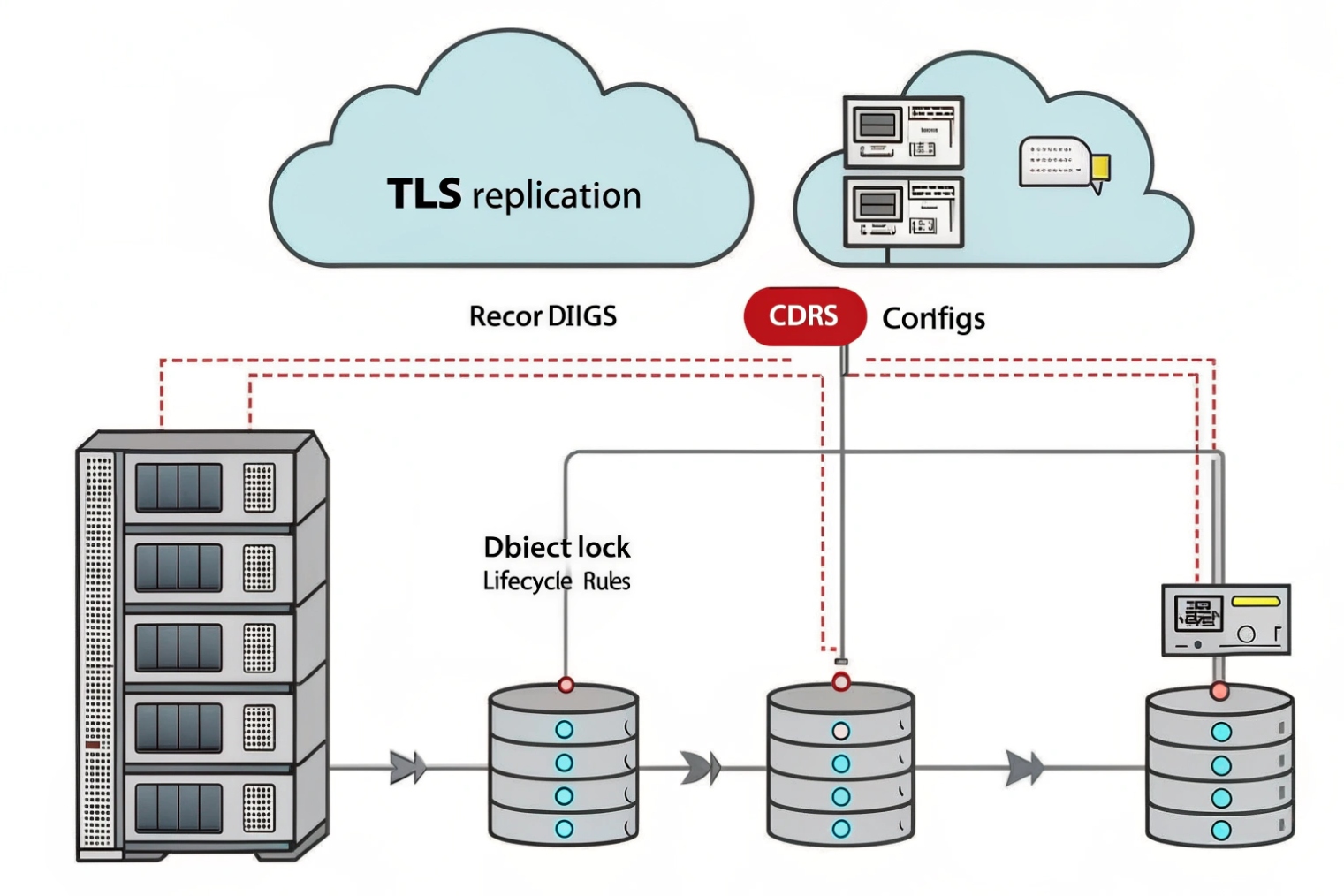
On-prem patterns (choose one, keep it consistent)
1) Hypervisor/agent-based CDP (common, fast to deploy)
2) Storage-based CDP (strong at scale, needs careful consistency grouping)
3) DB-aware protection for CDR/metadata (recommended if you can)
Cloud PBX / SaaS reality
You usually can’t CDP the provider’s disks. Instead:
- Export recordings to your controlled storage (if supported)
- Export CDRs/audit logs on a schedule
- Export configs/routing reports regularly (and keep versions)
S3/object storage controls that matter
- TLS in transit
- Encryption at rest (managed keys or KMS)
- Block public access + strict bucket policies
- Separate roles for write-only backup vs read/restore
- Versioning + Object Lock/WORM when required
The test that proves the design
Run restore drills that mirror real incidents:
- Restore one voicemail box
- Restore one day of recordings plus metadata/index
- Restore a CDR slice used for billing/compliance
- Roll back a “bad routing change” cleanly
If any step is slow or confusing, fix runbooks and permissions until recovery is routine.
Conclusion
CDP gives near real-time rollback for VoIP data like recordings, CDRs, voicemail, and configs. Pair it with immutability, encryption, and real restore drills so recovery works under pressure—not just on paper.