Phone bills stay high while your old lines sit half idle. Expanding means new circuits, contracts, delays. This pain pushes many teams to look at SIP trunking.
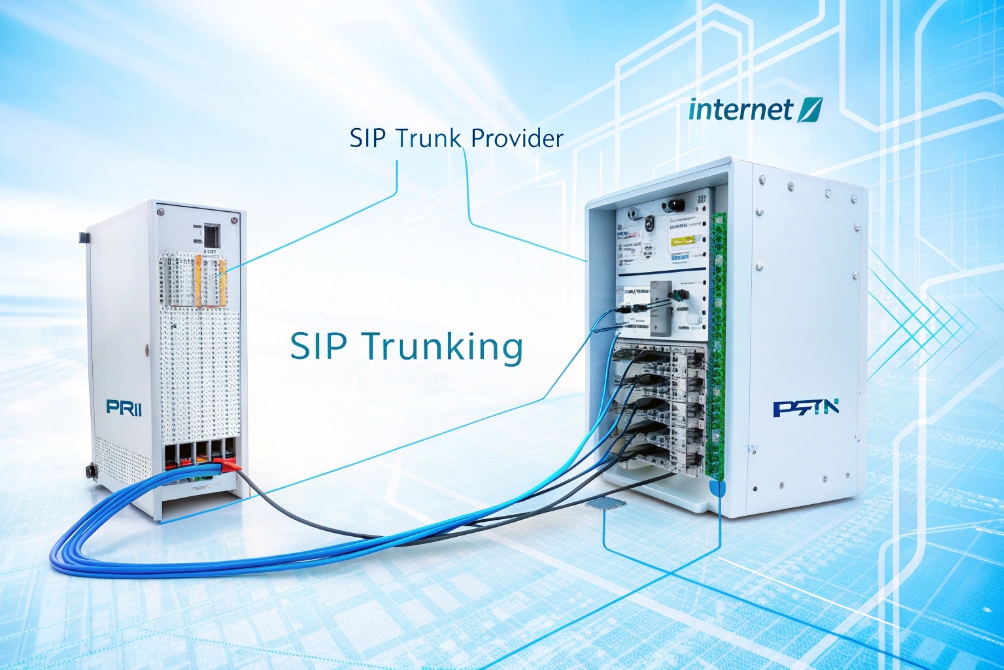
SIP trunking replaces physical phone lines with virtual channels over your internet link. It connects your IP PBX to carriers using SIP, so you scale simultaneous calls and numbers in software while cutting line costs and gaining flexibility.
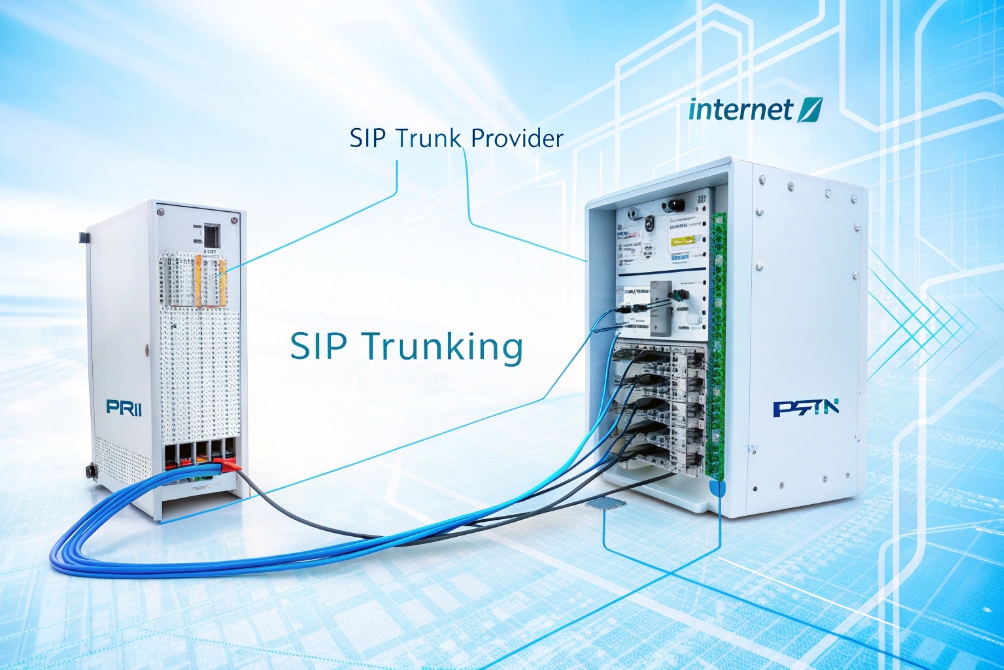
Instead of ordering new PRI circuits every time the business grows, you treat voice like any other IP service. Your IP PBX talks Session Initiation Protocol (SIP) 2 to a provider, and the provider bridges you into the public phone network. Once this is in place, capacity and features become configuration choices, not cable pulls and site visits.
How does SIP trunking connect my IP PBX to carriers?
Many people hear “SIP trunk” and imagine a special cable or box. When they cannot see it, they assume it must be very complicated.
A SIP trunk is a logical SIP connection between your IP PBX and a service provider’s SBC over IP. The provider then routes your calls to and from the PSTN using that single virtual link.

The basic call path
At a simple level, SIP trunking has three main parts:
- Your IP PBX or UC platform on-site or in the cloud.
- The SIP trunk provider (ITSP / carrier).
- The PSTN and mobile networks where most numbers still live.
When a user dials an external number:
- The IP phone or SIP intercom sends SIP signaling to the IP PBX.
- The IP PBX applies dial plan rules and sends an INVITE to the provider across the SIP trunk.
- The provider accepts the call, picks the right route, and connects to the destination network.
- Media (RTP/SRTP) flows between your PBX or SBC and the provider’s edge.
- When the call ends, SIP BYE messages close the session.
For inbound calls, the path is reversed. The provider receives the call from the PSTN, looks up which customer owns that DID, and sends an INVITE to your PBX across the trunk.
Registration vs IP authentication
Your PBX can connect to the trunk in two common ways:
-
Registration-based
The PBX behaves like a SIP “user”. It REGISTERs to the provider with credentials. The provider sends inbound calls to that registered contact address. This is common for smaller deployments and dynamic IP addresses. -
IP-authenticated
The PBX or SBC uses a fixed public IP. The provider whitelists that IP. No username/password is needed for each INVITE. This is common in enterprise, data centers, and when an SBC fronts many PBXs.
A simple comparison:
| Aspect | Registration-based trunk | IP-authenticated trunk |
|---|---|---|
| Uses username / pwd | Yes | Often no |
| Needs fixed public IP | Not required | Usually required |
| Good for | Small sites, dynamic IPs | Data centers, enterprises, SBC edges |
| Inbound routing | To last registered contact | To pre-defined IP and port |
Role of the SBC at the edge
Most serious deployments put a Session Border Controller (SBC) between the IP PBX and the external trunk. The SBC:
- Terminates the SIP trunk from the carrier.
- Normalizes headers and codecs for your PBX.
- Anchors media and handles NAT.
- Enforces policies and security.
From the PBX side, the trunk then looks like one clean SIP peer, even if you have multiple providers and complex routes behind the SBC. This is how large systems keep their dial plan clear while still using several carriers, failover paths, and local breakouts.
Will SIP trunks cut costs vs PRI lines?
When people hear “SIP is cheaper”, they often expect the bill to drop in half on day one. Later they see new costs for bandwidth, SBCs, or licenses and feel disappointed.
SIP trunks usually reduce monthly line and long-distance costs compared to PRI by using shared IP bandwidth and flexible channels. Real savings appear when you centralize trunks, right-size call paths, and remove unused legacy circuits.

Where the real savings come from
A PRI circuit gives you about 23 voice channels per physical line. If you need more, you add another circuit, even if you only need a few extra call paths. You also pay line rental, sometimes per-site.
With SIP trunks:
- Channels are virtual, so you can order exactly the number you need.
- You can burst above your normal channel count with some providers.
- You can share capacity across many sites using a central trunk.
This lets you do things like:
- Shut down small PRIs in branches and host all external traffic at a central SBC.
- Use the WAN or VPN for internal site-to-site voice, not PSTN.
- Move international traffic to a cheaper global SIP provider.
Cost components to compare
When I look at cost with partners, I always put components side by side:
| Cost area | PRI / legacy lines | SIP trunking |
|---|---|---|
| Access lines | Per physical circuit | Per trunk or per channel |
| Channel granularity | In blocks (23 per PRI) | One or a few channels at a time |
| Long-distance | Often higher tariffs | Often lower VoIP rates |
| Hardware | PRI cards, gateways at every site | SBCs, IP PBX licenses |
| Network | Separate voice circuits | Uses IP network (may need bandwidth upgrade) |
| Flexibility | Slow to resize | Fast to add or remove channels |
How many call paths and DIDs do I need?
SIP trunks let you order any number of channels, but that choice can be confusing. Many teams ask for “as many as possible” and then overpay for idle capacity.
You size SIP trunks by peak simultaneous calls, not by headcount. DIDs are separate: you buy enough numbers to cover required direct lines, departments, and special services, then map them onto a smaller pool of shared channels.

Call paths vs DIDs in plain words
Two key concepts often get mixed:
- Call path / channel: one active call, inbound or outbound. Ten channels mean up to ten concurrent calls.
- DID (Direct Inward Dial): one phone number that routes into your PBX.
You might have:
- 200 staff.
- 100 DIDs.
- 40 call paths on your SIP trunk.
Not everyone talks at once. Not everyone has or needs a personal DID. The art is to match channels to realistic peak use.
How do I secure SIP trunks with TLS, SRTP, and SBCs?
Once your voice leaves the building as IP traffic, it faces the same risks as any other service on the internet: eavesdropping, spoofing, scans, and abuse.
You secure SIP trunks by combining SIP over TLS for encrypted signaling, SRTP for media, and SBCs at the edge for NAT traversal, topology hiding, rate limiting, and policy enforcement.

Protecting signaling with TLS
Plain SIP over UDP or TCP exposes:
- Phone numbers.
- Usernames and domains.
- Some internal IP information.
SIP over TLS wraps signaling in encryption:
- The provider and your SBC or PBX establish a TLS session, usually on port 5061.
- Certificates verify server identity.
- SIP messages travel as encrypted bytes, not readable text.
This protects registration, call setup, and some metadata from casual inspection on intermediate networks. It also aligns with many corporate policies that now expect encryption for almost all services.
Protecting media with SRTP
Even if signaling is encrypted, unprotected RTP can still be captured. SRTP solves this:
- It encrypts audio (and video) payloads.
- It adds integrity checks.
- It can use keys exchanged via SDP (inside TLS-protected SIP) or via DTLS-SRTP.
On a secure SIP trunk:
- SIP runs over TLS between your SBC and the provider.
- RTP runs as SRTP wherever possible.
- Recording and lawful intercept are handled in controlled points, such as the SBC or PBX.
Why SBCs are central for secure trunks
A Session Border Controller sits between your internal voice network and the provider. It acts as a smart firewall for SIP:
- Blocks malformed or abusive SIP messages.
- Hides internal IPs and extensions from the outside.
- Enforces call limits per trunk, per IP, or per customer.
- Normalizes SIP headers and codecs.
- Anchors media, which simplifies firewall rules and QoS.
On top of this, modern providers also sign caller IDs using frameworks like STIR/SHAKEN caller ID authentication 7. Your SBC or PBX can pass these attestation levels through, which helps your outbound calls avoid spam blocking and builds trust with called parties.
In practice, a well-secured SIP trunk looks like this: phones and SIP intercoms talk to the PBX over a protected LAN or VPN; the PBX talks to an SBC; the SBC talks to providers using TLS and SRTP. Logs from the SBC and PBX feed your monitoring, security tools, and compliance systems. This structure keeps your internal voice network flexible while your borders stay tight and controlled.
Conclusion
SIP trunking replaces rigid phone circuits with flexible SIP channels, so you size call paths smartly, cut legacy costs, and secure your voice traffic with TLS, SRTP, and SBCs as the system grows.
Footnotes
-
Diagram showing how SIP trunks replace PRI circuits and connect to a provider. ↩ ↩
-
Official SIP standard explaining requests like INVITE/REGISTER/BYE and core call setup behavior. ↩ ↩
-
Visual call-flow overview of cloud and on-prem SIP trunk connectivity. ↩ ↩
-
Example dashboard view for comparing trunk utilization and cost drivers. ↩ ↩
-
Quick illustration of users vs concurrent channels for trunk sizing. ↩ ↩
-
Security topology visual for TLS/SRTP/SBC protection layers. ↩ ↩
-
Practical overview of STIR/SHAKEN, why it matters, and how caller ID verification works. ↩ ↩