Manual setup looks fine on day one. Then devices reboot, sites expand, and one wrong parameter breaks calling. Remote auto-provisioning stops that pain before it starts.
Yes. Explosion-proof telephones can be auto-provisioned remotely as long as they are IP endpoints. “Explosion-proof” changes the enclosure and certification, not the provisioning logic, so ZTP works like any SIP device.

Remote provisioning is a system design, not a single feature
“Explosion-proof” does not block provisioning, but the site network often does
An explosion-proof telephone still boots like a normal IP device. It requests an IP address, it resolves DNS, it checks time, and it pulls config. The friction usually comes from plant rules, not from the device. Many industrial networks block internet access, block multicast, and lock down DHCP options. These policies are reasonable. They also mean the provisioning plan must be chosen early and tested on the real VLAN, not on a bench switch.
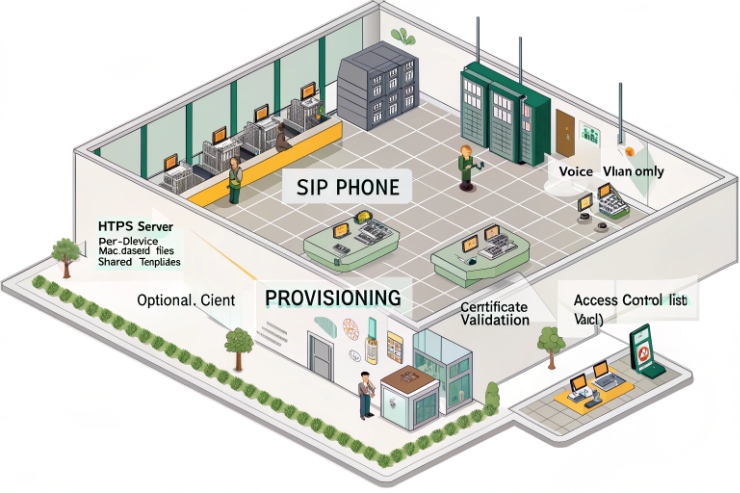
A practical rule guides most deployments: keep provisioning traffic predictable and easy to audit. That usually means HTTPS to an internal server, plus a clear device identity model. When the site accepts cloud services, vendor redirect servers can reduce labor. When the site blocks cloud, DHCP-based redirection and internal provisioning servers become the core.
Trust model comes first: how the device proves it is allowed
Provisioning is a security workflow. The device must prove it belongs to the right customer and the right site. MAC address mapping is simple and common, but it is not the strongest identity. IP endpoints 1 are secured best when certificates are used, though they need lifecycle management. The right choice depends on the customer’s security team and the size of the rollout.
Which zero-touch methods are supported—DHCP options 66/160, PXE, SIP Plug-and-Play, or vendor redirect servers?
Hands-on provisioning wastes time and introduces human error. The worst moment is a shutdown window when one phone has the wrong proxy and nobody knows why.
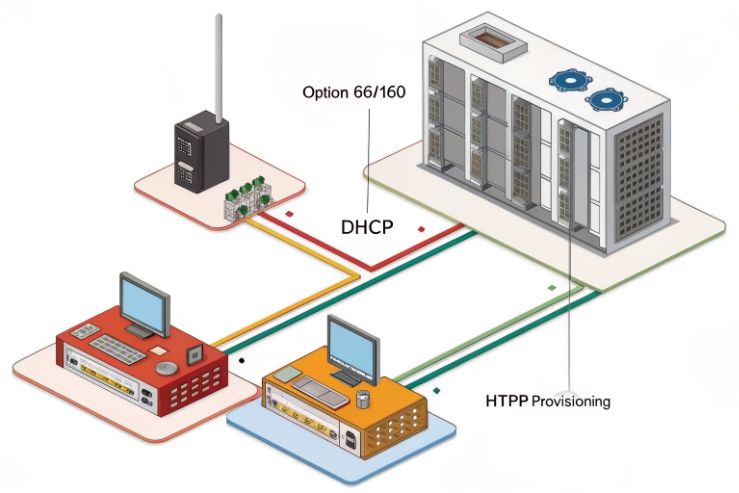
Zero-touch is usually done through DHCP options (66/160), SIP Plug-and-Play on multicast, or vendor redirect servers. PXE is uncommon for phones and is rarely the right tool for SIP endpoints.
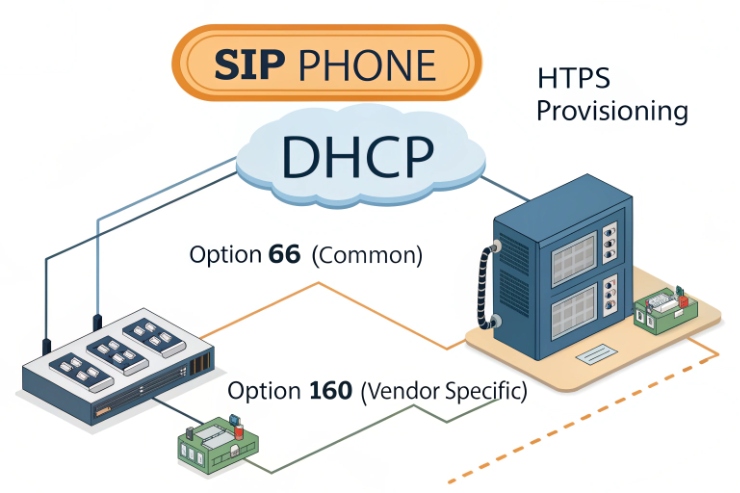
DHCP Options 66 and 160: simple redirect inside the LAN
DHCP Options 66 and 160 2 are widely used to point a phone to a provisioning server name or URL. It fits sites that already manage DHCP centrally. Option 160 is used by some vendors and can deliver a provisioning URL and file paths. Both methods shine when the plant blocks internet and the provisioning server sits on-prem.
Key design points:
- Use a dedicated voice/security VLAN so one option does not hit the wrong endpoints.
- Keep the URL short and stable.
- Prefer HTTPS provisioning even if DHCP delivers the URL.
SIP Plug-and-Play: fast in flat networks, fragile across VLANs
SIP Plug-and-Play 3 often works like this: the phone sends SIP SUBSCRIBE messages to a multicast address and waits for a server response that includes the provisioning URL. This can be great for quick deployments in a single broadcast domain. It can fail when multicast is blocked or when the phone and the server sit on different VLANs.
Can bulk provisioning use HTTPS, TR-069/TR-104, or MQTT with certificate-based authentication and ACLs?
Plants demand control and proof. Security teams want strong identity. Operations teams want repeatability. Bulk provisioning must satisfy both.
Yes. Bulk provisioning often uses HTTPS file provisioning, and it can also use TR-069/TR-104 for managed fleets. MQTT can work for custom device agents, and it supports TLS client authentication, but it is less common on standard SIP phones.
TR-069/TR-104: carrier-grade device management for VoIP fleets
TR-069/TR-104 4 defines VoIP data model parameters for provisioning voice endpoints and gateways in that ecosystem. This is not “just provisioning.” It is lifecycle management: config, firmware, and reporting.
MQTT: strong when a device platform already uses it
The MQTT protocol 5 is common in IoT telemetry. It can also drive provisioning when a device has an agent that subscribes to a “config topic” and applies signed updates. MQTT supports TLS client authentication and ACLs at the broker level. This can be powerful in industrial systems that already run MQTT brokers.
How are config templates versioned and applied—per model, per site, with rollback and staged rollout?
Most outages come from “small changes.” A codec setting changes. A proxy address rotates. One site has a special dial plan. Without versioning, these details drift and break.
Templates should be versioned like software. A model template defines device-specific keys. A site overlay defines VLAN, SIP server, and emergency rules. Rollback and staged rollout reduce risk during updates.

Versioning that works with real operations
Version each template and overlay, and treat every change as a release. Many engineering teams utilize semantic versioning 6 to maintain clarity.
- Use a structured versioning system or a simple date-based version.
- Add a change note for every edit.
- Store templates in a repo with reviews.
What network requirements ensure success—VLAN, QoS, NAT traversal, firewall ports, and redundant provisioning servers?
Provisioning fails most often for basic reasons: DNS fails, time is wrong, TLS breaks, or a firewall blocks one port. These failures look “random” until the network checklist is clear.
Provisioning succeeds when the device VLAN has stable DHCP/DNS/NTP, predictable outbound paths to provisioning and SIP services, and redundant servers. QoS helps voice, and it can also protect provisioning during congestion.
QoS and DSCP: keep voice stable, keep boot predictable
Provisioning traffic is not huge, but plants can have bursts during power restoration. QoS helps when dozens or hundreds of endpoints reboot at once. Proper DSCP marking 7 ensures that critical signaling is prioritized over general background data.
Conclusion
Remote auto-provisioning is practical for explosion-proof phones when discovery, identity, templates, and network rules are designed together. The result is faster rollout and fewer site visits.
Footnotes
-
Definition of hardware or software devices that connect to a VoIP network using Internet Protocol. ↩ ↩
-
Technical specifications for DHCP options used to automate the configuration of network boot servers. ↩ ↩
-
A mechanism allowing SIP devices to automatically discover provisioning servers within a local area network. ↩ ↩
-
The industry standard protocol for remote management of customer-premises equipment by internet service providers. ↩ ↩
-
A lightweight messaging protocol designed for low-bandwidth, high-latency, or unreliable networks in industrial IoT. ↩ ↩
-
A structured numbering system for software releases to ensure clear communication of changes and compatibility. ↩ ↩
-
A network architecture that specifies a mechanism for classifying and managing network traffic using priority levels. ↩ ↩











