You launch a new outbound campaign, but contact rates drop overnight. Agents wait, dashboards show failures, and customers say they never saw your call ring at all.
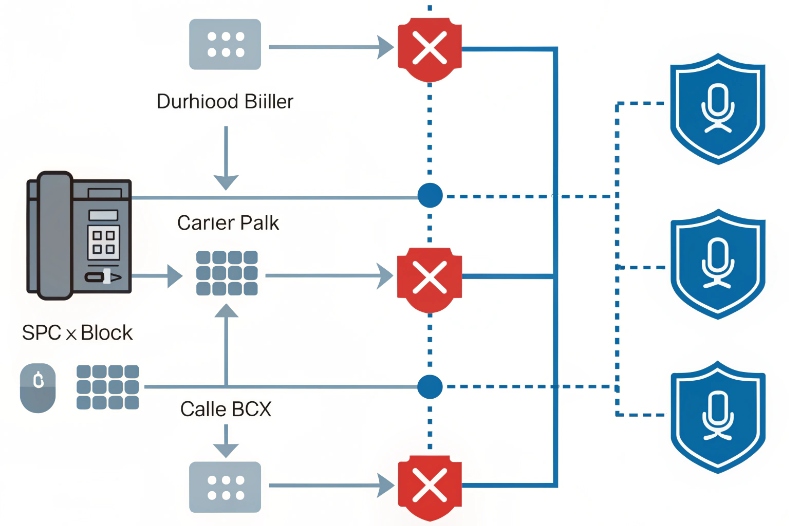
A blocked call is a call that is intentionally stopped from reaching the destination by a device, PBX/SBC, carrier network, spam filter, or app. It never really “gets through”, even if your dialer shows it as attempted.
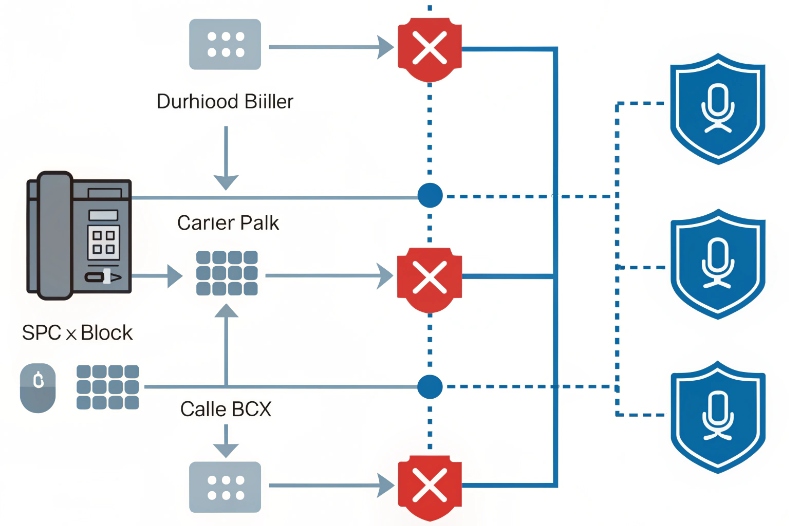
In real deployments, blocking can happen on many layers at once. A mobile user can block a number on the handset. An enterprise can block ranges on the SBC. A carrier or analytics provider can block calls based on spam algorithms 1, malformed caller ID, STIR/SHAKEN signals, or compliance rules. For call centers, SIP intercoms 2, and outbound notification systems, this is no longer a niche issue. It directly impacts answer rates, sales, and even emergency workflows.
So it is important to separate three things: simple user blocking, “spam likely” labels, and true carrier-level blocking. Labels hurt answer rates but calls still arrive. Blocking stops the call path at some hop and usually returns a specific SIP or ISUP cause code 3. Once you see call blocking as a multi-layer decision process, you can start to debug it from the signaling, align your caller ID, and work on your reputation data with carriers and analytics partners.
Why are my calls flagged as spam likely?
You may have valid opt-in customers, real agents, and a clean CLI, yet phones still show “Spam Likely” or similar warnings. This feels unfair and random.
Spam labels usually come from analytics engines that see high-risk patterns: high call volumes, short calls, bad answer ratios, untrusted caller ID, missing attestation, or user complaints against your numbers.

How spam labeling actually works
Spam tagging is not magic. Carriers and analytics providers run scoring models on traffic they see on their networks. They mix many signals, for example:
- Call velocity from each number or trunk.
- Ratio of answered calls to attempts.
- Very short calls, fast redials, or repeated retries.
- Calling at sensitive hours in each region.
- History of user “report spam” or “block” actions.
- Caller ID number not matching valid ranges or registries.
- Low STIR/SHAKEN attestation or unsigned caller ID in some countries.
Their goal is to stop illegal robocalls and fraud, not your customer service. But their models are not perfect, and sometimes good traffic looks similar to bad traffic.
Here is a simple way to think about what the algorithms see:
| Signal they see | What it might mean | Why it raises risk |
|---|---|---|
| Thousands of short calls per hour | Predictive dialer or robocall traffic | Many people hang up confused or annoyed |
| Low answer rate on a number | People do not trust this number | Could indicate unwanted or cold traffic |
| Many user spam reports on one caller ID | Recipients are actively unhappy | Strong reason to tag future calls as spam |
| CLI not assigned or mismatched | Caller ID may be spoofed | High risk, often linked to fraud |
| Mixed or low attestation levels | Network is unsure about caller identity | Adds weight to bad patterns |
If you call fast, call cold, or call people who did not clearly consent, your traffic looks risky to these systems even if your business is legitimate. This is why two companies with the same dialer can see very different outcomes. One collects strong opt-ins, uses good timing, and rotates call patterns. The other keeps blasting generic lists. The second one gets flagged first.
So the practical question is not “Why do they hate my calls?” but “What does my traffic look like when they score it?” Once you see it this way, you can adjust patterns, register your numbers with reputation partners, and align your caller ID and consent flows.
How do I avoid carrier-level blocking?
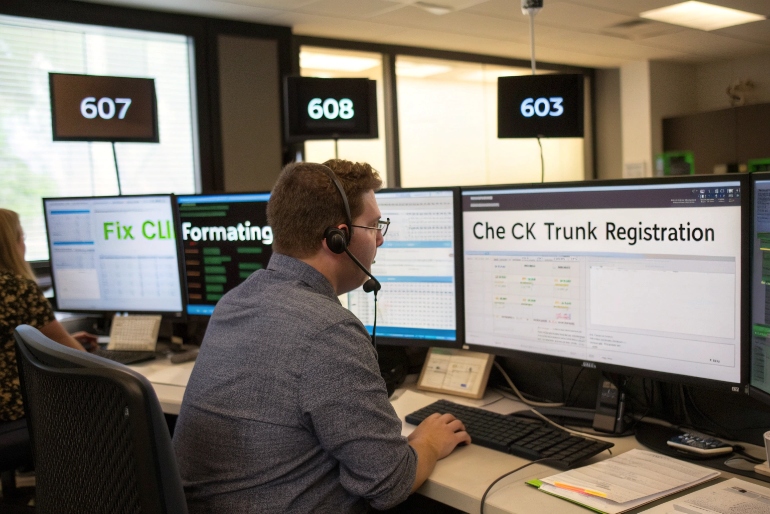
When calls never reach the handset, your business has a serious problem. You might see many SIP 607/608/603 responses, “call rejected” messages, or strange drops at the same point in the route.
You avoid carrier-level blocking by fixing caller ID, cleaning contact lists, controlling dialing behavior, respecting compliance rules, and working with carriers and analytics vendors to prove that your traffic is wanted.
Build a clean technical foundation
The first step is simple hygiene on the signaling side. Many blocked calls are not “punishment”; they are technical rejects. For example:
- The caller ID (CLI/ANI) is malformed, not in E.164 format 4, or too short.
- The number is not assigned or not associated with your trunk.
- The caller ID country does not match the trunk’s region or type.
- You send anonymous or withheld caller ID into networks that do not allow it.
A strict carrier may block or downgrade such traffic before analytics even start. So you should:
- Use valid, assigned numbers for outbound.
- Align caller ID with the trunk and contract.
- Avoid random rotating numbers from dubious sources.
- Respect local dialing rules for each destination country.
When we help partners debug SIP routes, we always start with call traces and CDRs. Look for patterns in SIP codes such as 607 “Unwanted”, 608 “Rejected by an intermediary”, 603 “Decline”, 480/486 for busy or unavailable, and any mapping to ISUP cause 21 on TDM legs. These codes show where and why calls are stopped.
Shape your calling behavior
Analytics-based blocking is more about behavior. Here the rules are simple, but they require discipline:
| Area | Good practice | Risky behavior |
|---|---|---|
| Consent | Strong opt-in, clear expectations | Buying lists, unclear or missing consent |
| Dialing pattern | Controlled pacing, retries after reasonable intervals | Rapid redials, “hammering” busy numbers |
| Campaign design | Specific, targeted campaigns | Always-on generic campaigns to huge lists |
| Time-of-day rules | Respect local quiet hours and regulations | Calling early morning, late night, holidays |
| Call handling | Real agents, clear scripts, short intros | Long IVR trees, misleading openings |
Carriers see these patterns. If your numbers start to trigger many 607 “unwanted” responses from end users, your reputation will fall, and some networks may start blocking upstream.
Work with trust and remediation services
If your outbound volumes are high, you should also:
- Register your brand and numbers with major analytics providers.
- Set up branded calling or rich call display 5 where supported.
- Use STIR/SHAKEN (where available) with the highest valid attestation.
- Monitor and remediate reputation hits across carriers.
Many ecosystems now have formal remediation flows. You submit your numbers, prove your business, explain your use cases, and adjust your behavior if needed. It takes some effort, but it is often the only way to repair damage once call blocking has started.
Does STIR/SHAKEN certification help me?
STIR/SHAKEN is often sold as a magic shield. Some people think that once calls are “signed”, spam labels will vanish and blocking will stop. Reality is more nuanced.
STIR/SHAKEN helps by proving caller ID is not spoofed and by improving attestation levels, but it does not override bad behavior or guarantee that your calls will never be tagged or blocked.

What STIR/SHAKEN really does
STIR/SHAKEN 6 is a caller ID authentication framework. On each call, the originating provider signs the call with a digital certificate that says how confident they are about the caller’s identity and right to use that number. In many countries, this is expressed as three attestation levels:
- A (Full) – Provider knows the customer and knows they are allowed to use that caller ID.
- B (Partial) – Provider knows the customer but is not sure they control that number (for example, behind a PBX).
- C (Gateway) – Provider only knows from which gateway the call came, not who is actually behind it.
For enterprises, the goal is to get as close to level A as possible on key outbound numbers. That shows downstream networks that your calls are more trustworthy than unsigned or C-level traffic.
Why STIR/SHAKEN is necessary but not enough
From a design view, STIR/SHAKEN is one input into analytics, not the final judge. Think of it like this:
| Factor | What it answers | What it does not answer |
|---|---|---|
| STIR/SHAKEN attestation | “Is this caller ID likely spoofed?” | “Is this traffic wanted or ethical?” |
| Reputation scoring | “How do people react to these calls?” | “Is the caller ID technically valid?” |
| Compliance checks | “Does this campaign follow regulations?” | “Is the number itself genuine?” |
So, yes, STIR/SHAKEN helps. It reduces the risk that your calls are blocked as obvious spoofing. It often improves answer rates when combined with branded caller ID. It is also required in some regions for certain types of traffic.
But if you use STIR/SHAKEN on aggressive robocall campaigns, it will not save you. Analytics engines still see high volumes, low answer rates, and many 607-style “unwanted” signals. In some cases, signing fraudulent calls can even cause extra regulatory attention, because it shows you are willing to authenticate bad traffic.
For most contact centers and enterprises, the best approach is simple: work with a provider that offers proper STIR/SHAKEN implementation, ask for clear documentation of attestation levels for your numbers, and then combine that with strong consent and careful campaign design.
How do I monitor call reputation scores?
You cannot fix what you never measure. It is common to see teams guess about reputation based on gut feeling or one carrier’s feedback, while problems grow silently on other networks.
You monitor call reputation by combining carrier analytics portals, third-party score dashboards, active test calls, and your own SIP and CDR data to track tagging, blocking, and end-user behavior over time.

Build a simple monitoring toolkit
There is no single global “credit score” for calls. Each carrier and analytics vendor has its own model. So you need a small toolkit that covers the main angles:
-
Carrier and analytics portals
Many large networks now offer portals where verified brands can see if their numbers are flagged, and sometimes see simple risk levels. -
Reputation services
Third-party tools 7 can check your numbers against multiple carriers and apps, and show how each one labels you. -
Test call programs
You can run controlled test calls to different networks and devices, then capture what the handset displays and any warning tones or messages. -
Internal SIP and CDR analysis
Your own platform can log SIP responses, call durations, answer ratios, and patterns that match blocking or heavy spam tagging.
Here is one way to structure the data:
| Source | What you see | How often to review |
|---|---|---|
| Carrier analytics | Label status, limited risk metrics | Weekly or after big campaign changes |
| Reputation vendors | Cross-carrier scores for key numbers | Weekly or monthly |
| Test calls | Real handset display, “spam likely” banners | Before and during major campaigns |
| SIP/CDRs | Codes like 607/608/603, answer rate trends | Daily in active call centers |
Turn data into action
Monitoring only helps if it drives changes. When you see sudden drops in answer rates or spikes in codes related to blocking, take concrete steps:
- Pause or slow down the campaigns that caused the spike.
- Check if new lists or new scripts were used.
- Rotate to alternate verified numbers only if they have clean history.
- Contact carriers or reputation partners through their remediation channels.
- Adjust your dialing and consent practices based on their feedback.
For high-value lines, such as emergency hotlines, critical alerts, or important B2B contacts, you can also set up alerts when key metrics change. For example, you can trigger an alarm when the answer rate from a specific carrier drops below a set baseline, or when 607/608 responses pass a threshold. This keeps your operations team proactive instead of reactive.
Conclusion
Blocked calls and “spam likely” labels are not random. With clean caller ID, careful dialing behavior, proper STIR/SHAKEN, and active reputation monitoring, your outbound traffic can stay trusted and reachable.
-
Overview of how carriers use analytics and spam algorithms to identify and block high-risk call traffic. Back ↩
-
Learn how SIP intercom devices use VoIP to manage secure building entry and communication. Back ↩
-
Reference table of SIP and ISUP cause codes used to diagnose blocked or failed calls. Back ↩
-
ITU explanation of the international E.164 numbering format used for global telephone numbers. Back ↩
-
See how branded calling and rich call display improve answer rates and trust for legitimate businesses. Back ↩
-
Background on the STIR/SHAKEN framework for authenticating caller ID and combating spoofed calls. Back ↩
-
Independent reputation tools that check how multiple carriers and apps label your phone numbers. Back ↩