One unmanaged port can open a plant network to a rogue device. One failed auth can also silence an emergency phone. Both outcomes are avoidable with a clear 802.1X plan.
Yes, many explosion-proof IP telephones can support 802.1X, but it is model- and firmware-dependent. In real deployments, EAP-TLS or PEAP are the common options, with MAB as a controlled fallback.
802.1X on hazardous-area endpoints: what “supported” should mean
802.1X is a three-party handshake, not a checkbox
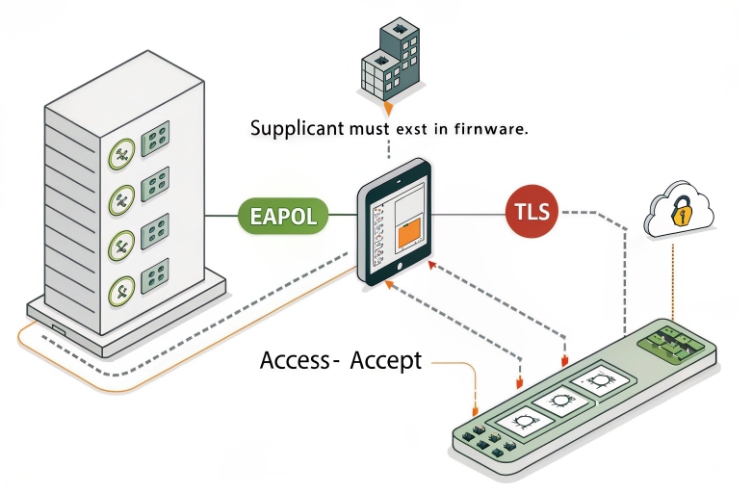
802.1X only works when the whole chain is aligned: the phone (supplicant), the switch (authenticator), and the RADIUS server (authentication server). The 802.1X authentication 1 process only works when the device can handle the EAPOL handshake correctly. A phone can “support 802.1X” and still fail if it cannot store a CA chain, cannot do the right EAP method, or cannot recover cleanly after link flaps. On industrial networks, those edge cases happen every week.
On explosion-proof telephones, field access is harder. The device may be mounted high, behind permits, or inside a restricted area. That changes the priority. A stable supplicant, strong identity, and a safe rollback path matter more than fancy features.
What to expect from an explosion-proof SIP phone
Most explosion-proof telephones are SIP endpoints first. That means:
- The phone must keep voice service stable, even when the port is reauthenticating.
- The boot sequence must handle “no network until auth” without getting stuck.
- The phone must store credentials or certificates safely without a local keyboard.
In my deployments, a phone is “802.1X-ready” only if it can:
- Run EAP-TLS or PEAP reliably
- Store certificates and private keys with clean import and renewal
- Expose enough logs to debug without a site visit
- Support a safe fallback policy (critical VLAN, MAB, or both) for emergency use
A simple readiness matrix
| Item | What to verify on the phone | What to verify on the network | What success looks like |
|---|---|---|---|
| Identity | EAP method list, cert storage, key protection | RADIUS policy for that method | Auth completes in seconds |
| Survivability | Reauth timers, link flap recovery | Switch timers, storm control | No reboot loops |
| Operations | Remote logs, syslog, web UI access | NTP/DNS reachability | Logs explain failures |
| Safety | “Critical voice” fallback plan | Critical VLAN / ACL policy | Emergency call still works |
A plant team does not need perfect. It needs repeatable. The next sections break down EAP methods, certificate scale, dynamic policies, and a practical troubleshooting stack.
If 802.1X is being introduced into a live site, start with a pilot on a small zone and lock the template before expanding.
Which 802.1X methods are available—EAP-TLS, PEAP-MSCHAPv2, or EAP-TTLS—with RADIUS compatibility?
One weak method can leak credentials. One unsupported method can block the phone at boot. Choosing the wrong EAP type is the fastest way to stall a rollout.
EAP-TLS and PEAP-MSCHAPv2 are the most common 802.1X methods for IP endpoints. EAP-TTLS is less common on many SIP phones. RADIUS compatibility is usually strong for EAP-TLS and PEAP on mainstream NAC platforms.

EAP-TLS: best security and clean device identity
EAP-TLS uses certificates on both sides. It gives mutual authentication and removes shared passwords from the device fleet. This matters in factories because:
- Phones are “headless” most of the time
- Password rotation is painful
- Credential reuse spreads fast
The EAP-TLS protocol 2 also scales better when the PKI process is mature. Once a device has a certificate, onboarding becomes predictable.
What to confirm on the phone:
- It supports EAP-TLS on wired 802.1X
- It can store client cert + private key
- It can store intermediate and root CA chains
- It can validate server cert and server name rules
PEAP-MSCHAPv2: common, but depends on password hygiene
PEAP creates a TLS tunnel using the server certificate, then authenticates with username/password (often MSCHAPv2). PEAP-MSCHAPv2 authentication 3 is widely supported and often easier to start with because it avoids a full device certificate lifecycle on day one.
The trade-offs are real:
- Shared secrets live on the endpoint
- Password rotation becomes an operational project
- If server validation is misconfigured, it can expose credentials to rogue networks
PEAP can still be acceptable for smaller deployments, or for transition phases. But for large fleets in regulated sites, EAP-TLS is usually the end goal.
EAP-TTLS: possible, but not a safe assumption on phones
EAP-TTLS is popular in some IoT and Linux-based supplicants. Many SIP phones do not expose it, or support it inconsistently across firmware trains. So it should be treated as “only if proven,” not “likely.”
RADIUS compatibility: what “compatible” should include
RADIUS compatibility is not only “it authenticates.” It should include:
- Correct handling of EAP fragmentation and retransmits
- Clean reauth behavior after link changes
- Correct processing of RADIUS attributes for VLAN, ACLs, and QoS (when used)
In harsh networks, EAP exchange timing matters. If the phone is slow to answer EAP requests, the switch can timeout and bounce the port.
| Method | What the phone must handle | Security strength | Operational effort | Best fit |
|---|---|---|---|---|
| EAP-TLS | Cert + key + CA chain + server validation | High | Medium (PKI) | Factory-scale fleets |
| PEAP-MSCHAPv2 | Server cert validation + stored credentials | Medium | High (password ops) | Transitional or small fleets |
| EAP-TTLS | Vendor-specific support | Medium to High | Medium | Only when confirmed in tests |
In a hazardous-area emergency workflow, the “best” method is the one that stays stable and is supportable at scale. For most modern fleets, that points to EAP-TLS with a strong certificate lifecycle plan.
How are certificates managed—device CSR, private keys, renewal, and CA chains—for factory-scale deployments?
A few devices can be managed by hand. A few hundred cannot. Certificate work must be designed like manufacturing, not like a one-time IT task.
Factory-scale certificate management works best with per-device keys, automated issuance, and planned renewal. The strongest pattern is: device generates a CSR, a trusted CA signs it, and the device stores the full chain and key securely with a renewal workflow.
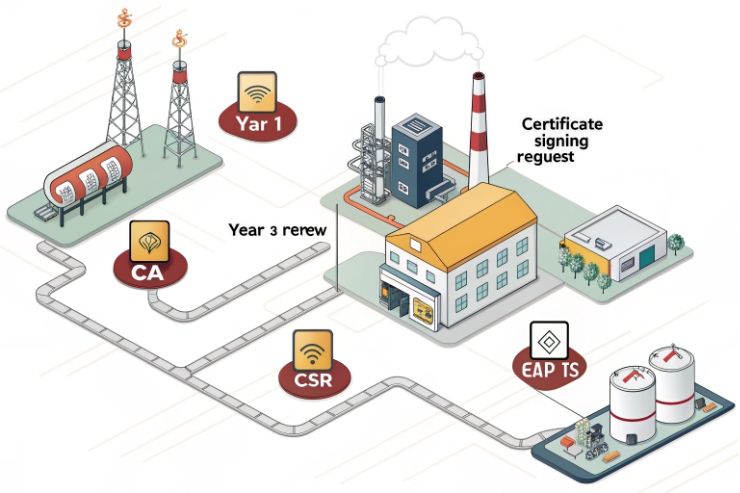
Choose the key ownership model first
There are two main models:
1) Device-generated keys (preferred)
- The phone generates a private key internally.
- The private key never leaves the phone.
- The phone produces a Certificate Signing Request 4 (CSR).
- The CA signs and returns a certificate.
This reduces risk because the factory or integrator does not handle raw private keys.
2) Factory-injected keys (sometimes required)
- A keypair is generated in a secure factory process.
- The key is injected into the device during provisioning.
- Certificates are preloaded.
This can be fast for true “zero touch,” but it demands strong controls. If key handling is width, a breach can affect the whole fleet.
Handle CA chains like a real deliverable
Phones fail EAP-TLS for simple reasons:
- Missing intermediate CA
- Wrong root store
- Expired server cert on the RADIUS side
- Time is wrong, so cert validation fails
So CA chain handling must be part of the template:
- Root CA
- Intermediate CA(s)
- Client certificate
- Private key
- Validation rules (server name or SAN checks)
Also plan for NTP early. A device with the wrong date will reject valid certificates.
Renewal and rotation: do not wait for the first expiry
A good renewal plan answers these questions:
- How far before expiry will the device renew?
- What happens if renewal fails?
- Can the device keep using the old cert until expiry?
- How will revocation be handled in emergencies?
Some customers want short-lived certificates. That increases security. It also increases renewal volume. In harsh networks, short-lived certs can create avoidable outages unless renewal is solid.
Practical approaches that scale
- SCEP or EST (if supported): automated enrollment using SCEP and EST protocols 5 for secure certificate management.
- HTTPS provisioning with certificate bundles: controlled distribution of certs and chains
- NAC-driven onboarding: quarantine VLAN until the cert is installed, then move to production
- Per-site sub-CA: reduces blast radius and simplifies policy
For explosion-proof endpoints, a clean method is to use remote provisioning to push a bootstrap identity, then enroll for EAP-TLS once the device can reach the enrollment service.
| Scale method | How it works | Strengths | Risks | When to use |
|---|---|---|---|---|
| CSR from device | Device generates key and CSR | Best key protection | Needs enrollment workflow | Most large fleets |
| Preloaded certs | Factory loads cert + key | Fast onboarding | Key handling risk | Controlled OEM programs |
| SCEP/EST enrollment | Automated issuance/renewal | Low touch at scale | Requires PKI services | Sites with mature IT |
| Manual import | Upload cert bundles by UI | Simple for pilots | Not scalable | Lab and pilot only |
A strong certificate plan is the difference between “802.1X works” and “802.1X works for five years.” That matters most on hazardous-area phones, because a site visit is expensive and slow.
Can 802.1X trigger dynamic VLANs, ACLs, or QoS policies, and how is MAB fallback handled for legacy devices?
A phone should not get the same access as an engineer laptop. A legacy endpoint should not block an emergency port. The policy must be strict and still safe.
Yes, 802.1X can drive dynamic VLAN assignment, dynamic ACLs, and QoS policies using RADIUS authorization results. For legacy devices, MAB can be used as a fallback, but it should be tightly scoped and monitored.
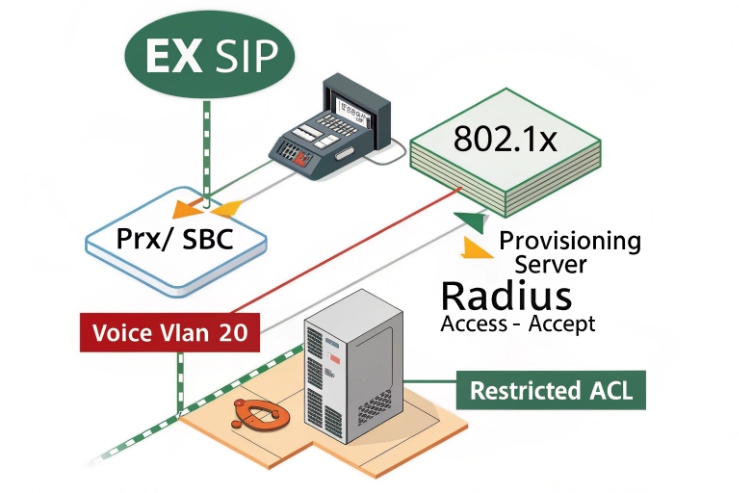
Dynamic VLAN: move the phone to the right network after auth
Dynamic VLAN assignment is a common and effective pattern. The RADIUS server returns RADIUS authorization attributes 6, and the switch places the port in that VLAN. In plants, this is used to:
- Separate voice/security devices from data devices
- Quarantine unknown devices
- Apply per-site segmentation without touching switch configs per port
A clean design uses:
- A “bootstrap VLAN” for unauthenticated state (very limited)
- A “voice/security VLAN” for authenticated phones
- A “quarantine VLAN” for unknown or failed devices
Dynamic ACLs: least privilege without a VLAN explosion
VLAN sprawl is real. Dynamic ACLs (often downloadable ACLs) solve that by keeping VLANs stable while controlling what the endpoint can reach. A phone often needs:
- SIP/SBC/PBX IPs
- NTP and DNS
- Provisioning server
- Syslog and monitoring
Everything else can be blocked.
QoS: enforce voice quality by identity
QoS can be applied by:
- Placing the phone in a policy VLAN that has trust settings
- Applying a policy based on the authenticated identity
- Marking or trusting DSCP for RTP while remarking other traffic
This matters because industrial networks can congest fast during outages or maintenance.
MAB fallback: safe use cases and safe limits
The MAC Authentication Bypass 7 (MAB) can help when a legacy device has no supplicant. But MAB is weaker because MAC addresses can be spoofed. So use it only with controls:
- Restrict MAB devices to a limited VLAN or limited ACL
- Use device profiling where possible
- Alert on MAC moves
- Keep MAB lists tight and reviewed
A common deployment model for phones is: try 802.1X first, then fall back to MAB only if the supplicant is missing or fails in a controlled way.
| Policy feature | What it enables | Best practice for phones | Common mistake |
|---|---|---|---|
| Dynamic VLAN | Segmentation by identity | Voice VLAN only after success | Mixing phones and PCs by accident |
| dACL | Least privilege on same VLAN | Allow only PBX, NTP, DNS, prov | Leaving “any-any” for convenience |
| QoS policy | Stable voice under load | Protect RTP and SIP | Trusting all DSCP from any device |
| MAB fallback | Legacy onboarding | Restrict access and monitor | Treating MAB as equal to 802.1X |
On hazardous-area deployments, the safety goal matters. If an emergency phone fails auth, the site loses a safety function. So every policy plan should include a “critical voice” path that is approved by both IT security and HSE operations.
What provisioning and troubleshooting tools support 802.1X—supplicant logs, EAPOL captures, RADIUS accounting, and switch templates?
802.1X issues feel random when logs are missing. The team blames the phone, then blames the switch, then blames the server. A good tool stack ends that loop.
Successful 802.1X operations need device supplicant logs, EAPOL packet captures on the access port, RADIUS authentication and accounting logs, and standardized switch templates with known-good timers and fallback behavior.

Provisioning tools that reduce on-site work
For explosion-proof phones, remote provisioning is the foundation. It should cover:
- Enabling 802.1X mode
- Choosing EAP method
- Installing CA chain and device identity
- Setting reauth timers and fail behavior
- Setting syslog targets and log level
A staged rollout helps. Push config to a test group first. Watch auth and call stats. Then expand.
Device-side visibility: what logs must exist
A phone should provide:
- 802.1X state: “authenticating / authorized / failed”
- EAP method used
- Certificate errors that are readable, not just “fail”
- Time, NTP status, and server validation errors
- Syslog export or remote log download
If the phone has no usable logs, support cost explodes. In that case, build the troubleshooting around switch and RADIUS logs and keep phone configs simple.
Packet capture: EAPOL frames tell the truth
An EAPOL capture on the switchport shows:
- Whether the phone starts EAPOL
- Whether the switch sends identity requests
- Whether TLS negotiation fails
- Whether retries and timeouts occur
Even short captures can show if the issue is timing, certificates, or policy mismatch.
RADIUS logs and accounting: separate “auth worked” from “session stayed up”
Authentication logs show:
- Why a request was rejected
- Which EAP method was negotiated
- Which policy matched
Accounting adds:
- Session start and stop records
- Interim updates for long sessions
- A session ID that can be used to track stability
In industrial sites, accounting helps prove if ports are flapping or if a device is bouncing between policies.
Switch templates: make ports behave the same everywhere
A good switch template includes:
- 802.1X enabled with known timers
- MAB fallback rules (if used)
- Critical VLAN or critical auth behavior for safety endpoints
- Voice VLAN plan (dynamic VLAN, LLDP-MED, or static)
- Logging and SNMP/telemetry settings
This prevents “one port config” from becoming a snowflake that nobody can maintain.
| Tool | What it answers | Who uses it | What to record for audits |
|---|---|---|---|
| Phone supplicant logs | “What did the device try?” | Voice/security team | Auth state, EAP method, cert errors |
| EAPOL capture | “What happened on the wire?” | Network team | Start/Identity/TLS failure pattern |
| RADIUS auth logs | “Why did policy allow/deny?” | NAC team | Rule hit, method, cert status |
| RADIUS accounting | “Did the session stay stable?” | Ops/SOC | Start/Stop/Interim with session ID |
| Switch template | “Is the edge consistent?” | Network team | Template version and port role |
A practical runbook for field teams helps:
1) Confirm link and VLAN.
2) Confirm time and NTP reachability.
3) Check switch 802.1X status and recent logs.
4) Check RADIUS reject reason.
5) Capture EAPOL if needed.
6) Roll back to last known-good template if safety is at risk.
When the tool stack is ready, 802.1X stops being scary. It becomes routine maintenance.
Conclusion
802.1X can work well on explosion-proof telephones when EAP choice, certificate lifecycle, dynamic policy, and troubleshooting visibility are planned as one system.
Footnotes
-
IEEE 802.1X standard for port-based Network Access Control overview. ↩ ↩
-
Technical documentation for the Extensible Authentication Protocol Method for Transport Layer Security. ↩ ↩
-
Guide to protected EAP methods using passwords for secure network authentication. ↩ ↩
-
Explanation of how a CSR is used to apply for a digital identity certificate. ↩ ↩
-
Standards for automated certificate enrollment and renewal in large-scale network deployments. ↩ ↩
-
Specification of attributes used to carry authentication and authorization information over RADIUS. ↩ ↩
-
Technical guide on using MAB as a fallback for non-802.1X capable devices. ↩ ↩